- Technical Forums
- :
- Switching
- :
- Re: Meraki MS NTP server - exit-relay.tor.world
Meraki MS NTP server - exit-relay.tor.world
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Meraki MS NTP server - exit-relay.tor.world
Hi there,
I have a customer who is getting logs on its Internet Edge firewall regarding NTP requests made from his Meraki switches. The weird thing is that some NTP requests are to the following domains/IPs between others (cloudfare i.e)
exit-relay.tor.world (178.162.211.152)
support.russianbridesnetwork.com (95.216.218.15)
formularfetischisten.de (85.10.240.253)
pauseq4vntp2.datamossa.io (103.126.53.123)
Which don´t seem to be related with an NTP service, specially the exit-relay.tor.world domain. He is very concerned about these requests.
Can you please help me to understand why Meraki switches are sending NTP requests to those domains? Is there any list with specific time server that meraki uses?
I opened a case with Meraki support but their answer so far is that "it is expected" however, I can not come back with my customer with that answer specially due the domains are being requested.
Looking forward for some help
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi!
Meraki Devices use the NTP server from Meraki Cloud, based in the network location, that you can find in "Network wide --> General." and efectively uses the NTP protocol port 123. It´s probably that the traffic that you have seen is it.
Network & Security Engineer
CCNP | JNCIP-SEC | CMNA
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
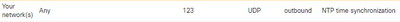
As you can see, Meraki recommends this rule to NTP service, bc neither Meraki knows what NTP server they´ll be ussing due that the location would it be any.
Regards,
Network & Security Engineer
CCNP | JNCIP-SEC | CMNA
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Guess your customer is simply using something like pool.ntp.org which handles out "random" DNS names that are acting as NTP servers.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am curious what evidence you have of this? Packet captures?
NTP is a protocol well known to be abused and vulnerable to various attacks, but I am skeptical these requests are actually coming from the switches. More likely a compromised host behind the switches, I would guess.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Brandon,
I have the firewall logs where I can see clearly the request being originated from the Meraki SW to the IPs/domains mentioned.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
it makes sense, bc Meraki will find different NTP server based on you time zone. So the firewall info says that you have to configure an any any eq 123 bc it will use different ip addresses(domains) as a destination
Network & Security Engineer
CCNP | JNCIP-SEC | CMNA
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I just ran a test and this particular domain exit-relay.tor.world does not respond to NTP request. What is concerning to my customer is not the NTP requests per se, it is this particular fqdn where the requests are being sent. As it looks like to be related as TOR exit point even when its reputation and risk scores are low.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @Johnfnadez . No Meraki device sends NTP queries.
So the question now becomes what device is actually making these queries. Are these switches running in L3 mode? Is the IP that is showing up the switching management IP or the L3 interface IP (if running in layer 3 mode)?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Switches are running in L2 and the source IP is the switch management IP address
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I found what the issue is. As you guys mentioned, Meraki uses ntp.pool.org however, these particular IPs host some ntp.pool.org sub-domains as well as, other domains such as exit-relay.tor.world and because of it, checkpoint firewall is relating the IPs with that domain instead.
As you said, it should not be nothing to be worried about, it is normal and expected behavior.
Thanks