- Technical Forums
- :
- Mobile Device Management
- :
- Re: Overriding iCloud activation lock on supervised devices
Overriding iCloud activation lock on supervised devices
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Overriding iCloud activation lock on supervised devices
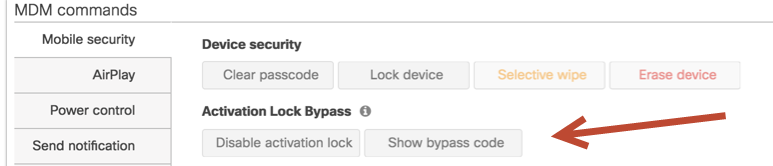
Has there been any change in the way that bypassing activation locks/iCloud accounts on supervised devices is handled?
We've recently had an iPhone device returned where the user has entered his personal iCloud account and has "Find my iphone" activated. When we set our system up 1½-2years ago it was tested so that the devices were completely overwritable including the iCloud-lock as long as the device was supervised and you used the bypass code from the Meraki device dashboard.
Now that we've gotten an actual situation where this is required entering the bypass code does not work.
We've also tried to do it on "clean" testdevices and we keep getting the same result, can't get past the iCloud account sign in.
Has the procedure changed, did some update break it or is this feature just not applicable anymore?
- Labels:
-
DEP
-
Enrollment
-
iOS
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That's interesting. We've had issues with one of our staff iphones which has gone through the same thing. I thought it was just his iphone. I'll ask my colleague what's been done with the phone in question.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@ZeMoMo I do hope that this is a bug that gets fixed for you as the alternative is called Apple and jump through a bunch of hoops that include providing a copy of the purchase invoice, its a long process that took a week from start to finish when I had to do it earlier in the year.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We've not had any support on this one. I believe we rebuilt the phone once we got it back into the office.So I am very curious to hear what you get back.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Checked in with our guy today.
Here's what happened here and it's not really a bug per se.
For whatever reason the user's iphone factory resets.
On boot it goes through it's normal setup process.
The user enters the wrong credentials.
This fails check in with SM.
But the phone starts.
User is now missing the SM setup we'd configured.
He doesn't have adinistrative access so he can't make the changes he needs to get the profiles working on his phone. He reboots - the phone is stuck in this weird twilight state.
What our guy did was change the associated account in SM from the wrong credentials to the correct one.
He then pushes a new profile to the phone.
This prompts the use for his password which he enters.
At this point all of the pending config tasks execute.
His phone is fine now.