- Technical Forums
- :
- Mobile Device Management
- :
- Anyone else seeing Unverified Certificates
Anyone else seeing Unverified Certificates
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Anyone else seeing Unverified Certificates
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
So everyone is aware, the command mentioned in the previous post is now live in your Dashboard. Use the Refresh Management Profile for any devices that have a profile that appears as Unverified.
Note that in the unlikely chance of a failure on the endpoint device, in refreshing the profile, you will have to manually re-enroll that device in SM. For this reason you should use this command selectively on devices known to have an issue rather than refreshing all devices at once.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Where in particular are you seeing?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Windows 10, Mac, IOS, Android, something else?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Richard_W This has definitely been seen by multiple admins across the community. I noticed it about a week back on a Catalina VM and figured since Catalina updates have yet to be pushed it was related to that. Then I saw this on roughly 800 machines.
What appears to have happened was Meraki either let the certificate lapse on the 16th or didn't plan ahead to ensure the update was pushed out in time. If you go back to m.meraki.com and reinstall the configuration profile it pulls a new verified profile signed by another Authority (image attached). From the case I have open with this the agent said it was up to Apple to trust the certificate they had updated and that it should be fine. In my opinion pushing a new cert that you are waiting on Apple to trust (what?!) into production on the premise it should be fine is unacceptable regardless of having planned it or for some reason waiting until it expired.
The solution given is to ignore this on current machines, because it is a "cosmetic" issue, or push an update to each profile to every machine to update this which again should work. I can verify that new profiles pushed are verified and signed by the updated certificate, but this doesn't address the entire fleet of machines that didn't happen to start this week.
Ive said it elsewhere, but while I don't see this as having a huge impact or presenting an immediate issue it just seems par for the course for issues we have seen and it is endlessly frustrating. We place implicit trust in Meraki as an MDM provider and an assumed part of that would be Meraki staying on top of upcoming changes. Do mistakes happen? Yes. That could easily be addressed by clear communication ahead of possible breaks or changes that make it easier on all of us managing hundreds and thousands of machines that may be impacted.
Rant over but TLDR; it's happening because of that cert expiration, you get to push the changes to fix it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@jm_peterson You've captured the details of the "unverified profiles" very well and your rant is justified: once we knew that the Certificate Authority change was going to take place we should have done a better job at informing our customers about what was going on.
With regard to the current situation, as you pointed out, the warning is indeed cosmetic. However, clearly it is not a tenable situation for you to leave management profiles in place that are not part of a proper certificate trust chain.
As far as what to do right now:
* For profiles that are not the main management profile: any minor change, such as modifying the name of the profile, will cause it to refresh with the new root CA.
* For the main management profile, a re-enrollment will fix it, but as pointed out this is only useful when dealing with small numbers of devices directly. To solve the "at scale" issue we are developing a feature to re-install the management profile as a bulk action initiated by the Meraki Admin. I can't provide an ETA just yet but it is an important issue for us to get fixed, we don't want to leave those "unverified" profiles sitting out there confusing your users.
Once again, to all of our customers affected by this, please accept my apologies for how this issue was handled. We are hopeful we will have this remedied shortly.
Noah Salzman
Product Manager for Meraki SM
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Kudoed to signal the importance 🙂
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If this was twitter we would have to continually restate: "Kudos are not necessarily endorsements". 😉
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hey All, sorry for the delay on this one. The feature we are building to address this is still in our queue, it just got put behind a couple more critical issues. I'll provide an update as we get closer to delivering it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Update: we've made good progress on our feature for refreshing certificates. We're trying to get this wrapped up and tested by the second week in March.
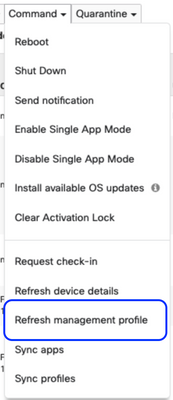
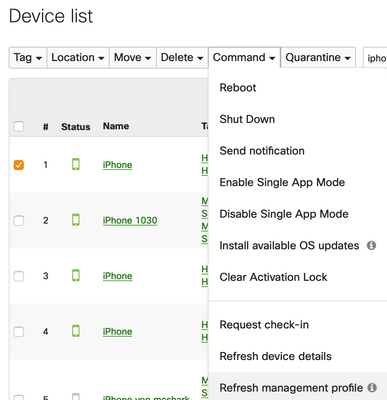
What are we delivering? The way to fix the Unverified Certificates is to refresh the management profile on the device. We are adding a new command so that you can pick the time and targets rather than Meraki doing this en masse in the backend. The new command will be next to "Refresh Device Details".
Every deployment is a little different and because of that it's always prudent to run tests before pushing out a change to the management profile. We will be recommending that you run this command on a subset of your devices before performing this command on all devices that are showing "unverified". We do not expect issues with refreshing the profiles, however, if there is an issue the device will need to be manually re-enrolled.
We will update this thread once the feature has been released.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
So everyone is aware, the command mentioned in the previous post is now live in your Dashboard. Use the Refresh Management Profile for any devices that have a profile that appears as Unverified.
Note that in the unlikely chance of a failure on the endpoint device, in refreshing the profile, you will have to manually re-enroll that device in SM. For this reason you should use this command selectively on devices known to have an issue rather than refreshing all devices at once.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
All that leaves is a quick way to figure out which machines need to be refreshed then, any ideas?
R.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Where in the Dashboard is this new command "Refresh Management Profile?"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
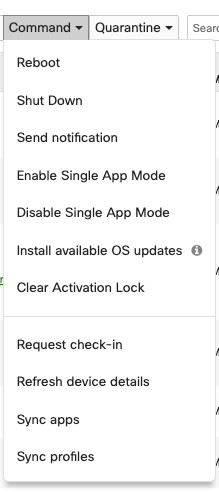
A little late to the party, and not sure if I'm missing something, but I'm not seeing the option to refresh management profiles from the Commands dropdown.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@AndrewMorales I asked @Noah_Salzman about this myself and he said the command has been removed.
I believe that when you used this command it would cause some devices to remove the Meraki Management Profile all together rather than re-installing the profile.
About this time is when the profiles stopped mysteriously being removed when iPad changed networks and all of the issues with profiles within Meraki not behaving correctly appeared.
I'm still waiting for them to fix the profiles not being removed when a device changes networks as this is a very much needed functionality within Meraki. The response of profiles not being deleted or a device should be reset is not a valid response.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
we have a big number of iPads which mysteriously got their management profile removed by itself without any action.
this happened on the 29th of March 2020
Problem is that communication is impossible thru the dashboard and impossible to enroll again with m.meraki.com because of the Ui Configuration Profile Installation restriction set to NO still present
is there a magic fix instead of having to manually reset the iPad ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is there any solution to this?
A year and more has passed with a solution offered then removed.
What are we to do?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
My solution was to switch to a different MDM that didn't do things like this that made me want to rip my hair out every day.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Richard, do you still have devices that have unverified certificates from the original incident in this thread? (Also, if you have a case number, can you send it to me in a private message.)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Are there any security implications? We have quite a few devices enrolled in 2019 that have 3 out of 5 signing certificates expired, which marks Management Profile as "Not Verified". I'd rather not re-enroll a thousand odd devices.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
is there a reason why this option has disappeared from Dashboard ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is there a solution for this ongoing issue?