We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Switching
- :
- Re: STP guard setup - best practices
STP guard setup - best practices
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
STP guard setup - best practices
Curious what the consensus is on STP guard settings for ports on Meraki switches. We've turned on BPDU guard for all access ports. However, I was wondering under what circumstances Root or Loop guard would be used. We have a few 3rd party switches uplinked to some of our Meraki switches (trunk ports). Would Root or Loop guard be worthwhile to activate?
The same question goes for fiber uplinks - from Meraki switches to a core. Is there a best practice on what STP guard settings should be? Or is "disabled" the norm?
Thanks for your input. Happy to provide more topology details if need be.
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- We use bpdu-guard for client ports to prevent spanning-tree problems f.e. when users connect switches to the ports.
- We use loop-guard on switches with multiple uplink-ports to prevent loops in case of spanning-tree or aggregation problems.
- We don´t use the root-guard option because our core-switch is the rootguard with the best bridge ID priority value. So it´s not neccessary.
https://documentation.meraki.com/MS/Port_and_VLAN_Configuration/RSTP_on_the_MS_Switch
https://documentation.meraki.com/MS/Port_and_VLAN_Configuration/Switch_Ports
https://www.cisco.com/c/en/us/support/docs/lan-switching/spanning-tree-protocol/10596-84.html
https://documentation.meraki.com/MS/Other_Topics/Switch_Settings
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- We use bpdu-guard for client ports to prevent spanning-tree problems f.e. when users connect switches to the ports.
- We use loop-guard on switches with multiple uplink-ports to prevent loops in case of spanning-tree or aggregation problems.
- We don´t use the root-guard option because our core-switch is the rootguard with the best bridge ID priority value. So it´s not neccessary.
https://documentation.meraki.com/MS/Port_and_VLAN_Configuration/RSTP_on_the_MS_Switch
https://documentation.meraki.com/MS/Port_and_VLAN_Configuration/Switch_Ports
https://www.cisco.com/c/en/us/support/docs/lan-switching/spanning-tree-protocol/10596-84.html
https://documentation.meraki.com/MS/Other_Topics/Switch_Settings
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for this redsector. A follow-up question, and to quote the Cisco STP article link you sent...
"The biggest issue with STP is that some hardware failures can cause it to fail"
With that said, is there any benefit (or drawback / issue) to enabling Loop guard on a single uplink port? I'm not certain on what type of hardware failure on a Meraki switch that would cause an overall STP failure. However, if Loop guard has inherent protections against something weird, it sounds like a good idea.
Thanks again for your input.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
LoopGuard is to protect against uni-directional links. So yes, even if there's only one uplink it can be useful.
However, my personal preference is to use UDLD over LoopGuard.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can we use loop guard and UDPD on same ports which is same port channel.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
So long as the configurations of the two ports are the same you should be able to aggregate them. You can certainly use Loop Guard and UDLD together, and the Meraki documentation recommends it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I don't ever use root guard. I have had it bite me in the past when various failures happened, and it made those failures more severe.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm not really a fan of loop guard unless there are redundant paths. Othewise if you have a single link and it triggers it'll take out the downstream network.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Follow normal recommendations for STP.
On out case, we are using MS devices as L2 only at the access layer.. Our core L3 devices are 4500 cisco.
we use the follwing settings that work perfect.
*Root guard: Configure at core on all ports to access switches and on access switches to APs
*BPDU guard: Configure in all access ports
*Loop guard: Configure in uplinks to core
*UDLD enforce on uplinks to core
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
On AP's do you mean Access Ports or Access Points?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I would think AP's meaning Wireless Access Points.
As a follow up, we now activate BPDU guard (with enforcement) on all access ports and any truck ports connected to a switch not under our control (a reality in a campus + residential environment). Has worked as advertised and saved our keisters on at least a dozen occasions since.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
AP = Access Points indeed. Wireless Access Points
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
On AP's do you mean Access Ports or Access Points?
---------------------
Accesspoints.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for bringing this question forward! We have published new documentation on STP guard configuration that incorporates STP guard recommendations. Check it out and let us know what you think!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
CJones - Thank you for posting this. It is very helpful.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Redsector had a great answer.
However that said, I don't use any of these settings because the Meraki already has RSTP on by default. I definitely don't configure them on Meraki-Meraki links because the expectation is to use RSTP. In my mind you should only use these spanning tree options if the port is connected to a switch that doesn't support RSTP.
As for root guard - I set the priority on my core switches, a stack of MS425s, to 0, and that stopped the inter-vendor squabbling over who thinks it's root.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have my root priority set to the core switch in the network but a few locations are still somehow wanting to use a core switch in another network.
Would that be something to be concerned with?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I always do the following:
- BPDU guard on all client ports and access point ports if they are Meraki (Meraki AP's don't send BPDU's).
- Root guard on all downlinks from CORE to access layer
- I would have wanted to put loopguard on uplinks of access layer switches but Meraki won't let me because we use the management inline with the network.
Also and this is important. If you have a MX warmspare with the four uplinks from the switch network towards those MX's that you DON'T enable bpdu guard on those ports leading to the MX and never ever use drop untagged traffic on the MX because that causes a loop.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
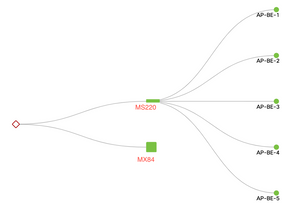
@GIdenJoeI see you mentioned MX upstream in HA mode. I have a MS225 switch stack of 4 switches with 4 uplinks going up from the the stack to the MX84s. All 4 trunks have loopguard enabled. Is this what you were suggesting with your comment about 4 uplinks to a warm spare MX? Or anybody else on the thread. Is this what you would recommend for a HA setup? I guess I could have burned more ports to the other two switches but seemed a little like overkill. **Forgot to mention that both trunks on SW1 are forwarding and both trunks on SW2 are blocking.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes your picture is completely correct in terms of HA setup and STP behavior.
In a stack only have four uplinks where two will be blocked because the BPDU's leave 1/0/1 and 1/0/2 with a lower Port-ID than 2/0/1 and 2/0/2 and the MX just forwards the STP messages since it does not participate in it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
May you please elaborate on the exact STP port related settings for the uplinks. I have the exact setup but with 2x MS120 (without a stack). I have tried almost any STP configuration on my 5 uplinks (including the one between the switches) but Im still getting a loop when I add the 2nd link from the firewalls.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
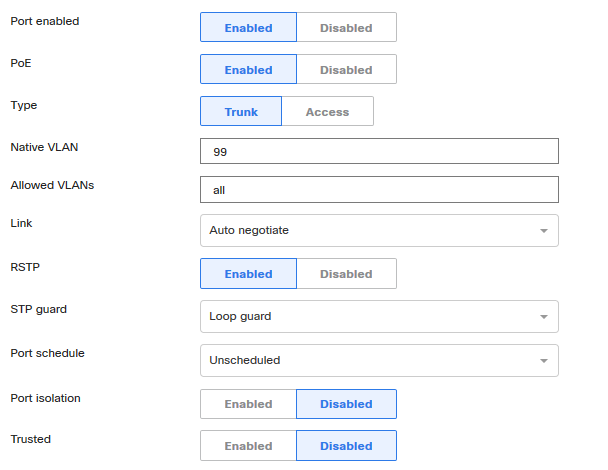
Now granted this is my lab at the moment but all of my switch trunks from my diagram are set like this. My MX is set to a trunk on native vlan 99, but I will eventually prune back the vlans back to only my vlans for the site.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Deguara, even without stacked switches it should work.
Since packets are bounced through the MX'es you should NOT enable any features like rootguard, loopguard or bpduguard on the links towards the MX'es.
The direct link between your switches can have root guard enabled in case of non-stack.
Make sure you don't have a link between your MX'es and you allow the same VLANs across the 4 links including the correct native. DO NOT USE drop untagged!. You can use a different VLAN native config between the switches.
Ensure one of your MS120's is root bridge for the L2 network.
You should see two links blocked on the switch that is not root bridge.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello GldenJoe.. You mentioned that, "I would have wanted to put loop guard on uplinks of access layer switches but Meraki won't let me because we use the management inline with the network". You mean we can not configure loop guard on Meraki switches.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The feature is there, but it seems if you are not using a physically separate mgmt network to reach the cloud you won't be able to set your access switch uplinks to loopguard. It will yell at you if you try to 🙂
I have yet to justify costs for extra SFP's and fiber connections to each access layer switch for a separate oob network...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello,
I have a question on the configuration of STP on my network.
We have one MX84 and one switch MS220. The switch is connected with a redundant optical fiber to the MX84 (Loop guard and UDLD is configured on the 2 uplink ports of the switch since support port aggregation is not supported by MX84).
When I check the topology, I see the topology is wrong and a message indicate "A switch was detected that improperly forwards LLDP packets. This can cause your network topology to be incomplete or incorrect."
What should I do / configure to have the right topology?
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
enable RTSP on both uplinks to make sure one of the uplinks is in blocking state.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
RSTP is active on both uplink ports.
STP guard is active in "Loop guard" on both uplink ports.
Port isolation is disabled and Unidirectional link detection (UDLD) is enforce.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hey @Johan
Basic things first. Remember the MX is not a switch and does not speak STP and does not support UDLD either. So what you are dealing with is one switch only which is your root bridge too.
- Both ends of a link need to support UDLD for this feature to initiate. Since the MX does not support it, enabling UDLD in your topology is useless
- Loop guard does not apply to your topology either. I'd not apply it.
For your topology enabling RSTP without any STP guard options (root, loop, bpdu-obviously) is enough. doing to should give you one of your fibre links in forwarding and the other in blocking.
A note on UDLD, as mentioned in your case is useless since the MX does not support it, in valid cases when UDLD is enabled, Meraki recommends to do it in "Alert Only" mode
Finally, regarding the "correct" topology. I am afraid that what you have is correct because of your two uplinks to the same box (MX). if you disable one of the uplinks you should see a more comprehensible topology. with both enabled you should be able to see a check box "Show redundant links" which makes the topology a tiny bit more comprehensible.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
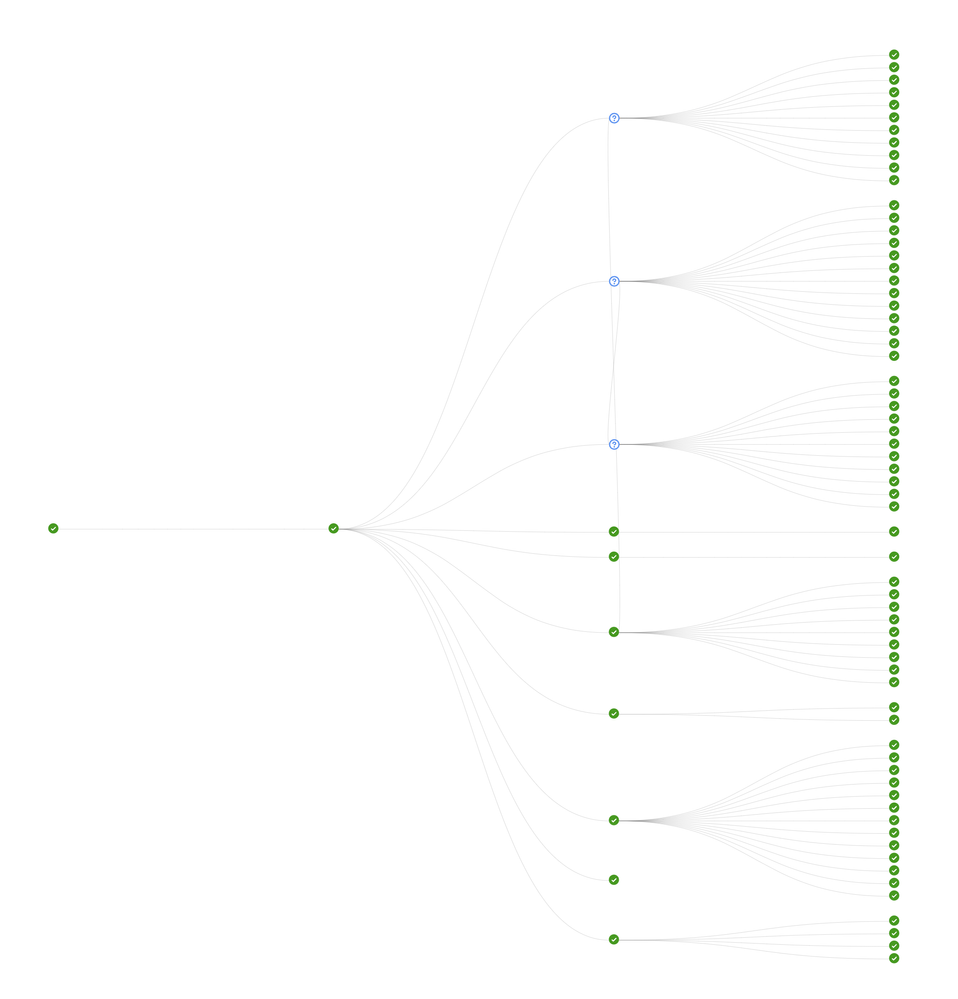
Sorry to reopen this thread, but I want to see if I understand how UDLD and STP guard should be set up on my topology. Here's the high level image from the dashboard. Very simple hub-spoke. Single uplinks from IDFs (either a stack of two or just a single switch) run back to MS425. Do I enforce UDLD and loop guard both ends, or just the uplink port for the IDF?


![2020-02-04 16_06_32-India - Tier3 design.vsd [Compatibility Mode] - Visio Professional.png 2020-02-04 16_06_32-India - Tier3 design.vsd [Compatibility Mode] - Visio Professional.png](https://community.meraki.com/t5/image/serverpage/image-id/11542iF1FA36C07BE23D46/image-size/large?v=v2&px=999)