We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- Restrict computers for VPN access.
Restrict computers for VPN access.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Restrict computers for VPN access.
Does anyone know if there is a way to restrict client VPN connectivity to allow only specific computers, when it comes to Meraki? Is it possible to do this with RADIUS perhaps?
I have a client that has a policy to only allow AD domain joined computers to connect to the VPN, and if Meraki/RADIUS/?, can do this I would like to sell them on Meraki. They are currently using a Sonicwall TZ400 for their firewall and an SRA1600 vpn appliance of which handles the required setup currently itself.
Thanks,
Ryan
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
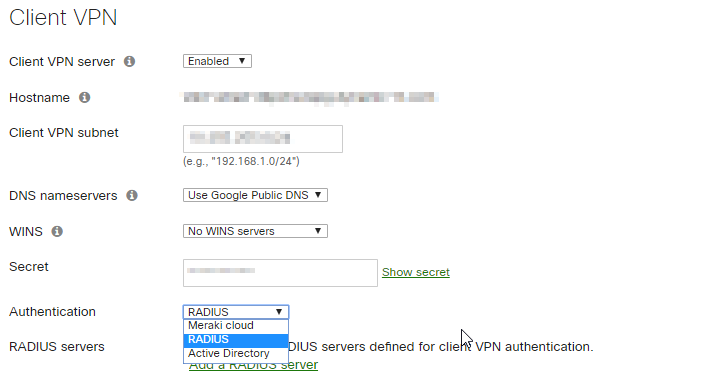
Yes, you can define which account database is to be used with Client VPN:
Don't expect a fully featured client VPN though. The creation of the VPN profile on the clients is described here:
https://documentation.meraki.com/MX/Client_VPN/Client_VPN_OS_Configuration
Rollout can also be scripted (credits to @PhilipDAth) :
http://www.ifm.net.nz/cookbooks/meraki-client-vpn.html
The built-in clients are limited in features.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
>I have a client that has a policy to only allow AD domain joined computers to connect to the VPN
You wont be able to do this. All you can do is checked that the user has entered an AD username/password - but not verify that it is being done from an AD joined computer.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @PhilipDAth,
Can you elaborate on why this isn't possible? We're looking to implement this (we already have RADIUS configured to authenticate based on a specific user group) but it sounds like it wouldn't work. NPS in Windows Server 2012 has the option to do both user and computer via Windows Group (which says it does both?), or, one or the other meaning you can select Machine Groups or User Groups.
Is this a limitation on the Meraki side?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Because the only information the RADIUS server gets is the users name and password. The RADIUS server is not told which machine the user is logging in from.
Consequently there is no way to restrict the machine being used.
This is a fundamental restriction of the Windows L2TP over IPSec client. Microsoft did not create a way for the machine name to also be passed or authenticated.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks @PhilipDAth,
That answers my question. I appreciate you replying to this old thread! Hopefully this info is helpful to others looking for this info as well.
Quick edit: If RADIUS doesn't get computer information, what mechanism would make it possible to authenticate the computer/device the user is logging in from? Would we have to use something different altogether?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm also seeking a way to do this. I had hoped that I could use DHCP reservations for the Client VPN subnet and create reservations for known MAC addresses. This isn't perfect but it is a lot better than nothing.
Unfortunately I am not seeing any way to specify DHCP reservations for a client VPN subnet.
Has anyone else figured out a way to either restrict or somehow validate the computers that are connecting to VPN in addition to validating the user?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
There might be another way to accomplish this using a different paradigm.
Google BeyondCorp or Perimeter 81 are both Zero Trust products that can link local applications, sites and services with cloud based services. Basically you create a site to site VPN to Google BeyondCorp or Perimeter 81 and then manage everything through those services. For instance, you want to provide Remote Desktop in a secure manor to a RDS server. You would configure the either vendor site with a Remote Desktop link, and grant access to the users who need that service.
Users are authenticated into Perimeter 81 or Google BeyondCorp and see a screen with the services and application that they access to. Google BeyondCorp can use user and machine certificates as part of the authentication process. Perimeter might be able to do that as well.
One benefit that is made clear during this Covid19 lock down, is that instead of all employees coming in through a VPN and overwhelming the firewall, there is only one VPN connection that the firewall needs. The employees sign into the BeyondCorp or Perimeter 81 site instead. This is more scalable and secure that a traditional VPN solution.
I apologize that this is a short and incomplete summary of these products. My intent was only to make you aware of different options for your VPN solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I see we have a number of people looking at this old thread.
Since this was originally posted a new method is now available. You can now configure certificate with username+password authentication with RADIUS.
You setup an Enterprise CA, and issue every machine with a certificate. Meraki+AnyConnect will first check that the machine has been issued a certificate, and then check the users username and password.
You can also use AnyConnect+SAML+Duo, and use Duo device trust to verifify the computer is a member of AD or manually trusted.
https://duo.com/docs/trusted-endpoints
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
306 -
AWS
36 -
Azure
70 -
Client VPN
382 -
Firewall
867 -
iOS
1 -
Other
557 -
Wireless LAN MR
1