- Technical Forums
- :
- Security & SD-WAN
- :
- New MX 17.7 Stable Release Candidate Firmware - huge number of fixes includ...
New MX 17.7 Stable Release Candidate Firmware - huge number of fixes including NBAR categorisation
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
New MX 17.7 Stable Release Candidate Firmware - huge number of fixes including NBAR categorisation
Security appliance firmware versions MX 17.7 changelog
Important notice
- While Meraki appliances have traditionally relied on UDP port 7351 for cloud communication and TCP ports 80 and 443 for backup communications, with MX 16 we are beginning a transition to using TCP port 443 as the primary means for cloud connectivity. In order to ensure proper connectivity to the Meraki cloud after this upgrade, please ensure that traffic using TCP port 443 between 209.206.48.0/20 is allowed through any firewalls that may be deployed upstream of your Meraki appliances.
- HTTP proxy, which allows default management traffic from MX appliances to be sent through a proxy, is deprecated on MX 16 and higher firmware versions.
- The transition to Cisco Talos intelligence for our content filtering services means that some URL categories have changed names, some categories are no longer available, and multiple new categories are now available. Please review your configuration after upgrading to ensure content filtering is effectively tailored to your needs and deployment environment.
Legacy products notice
- When configured for this version, Z1, MX60, MX60W, MX80, and MX90 devices will run MX 14.56.
- When configured for this version, MX400 and MX600 devices will run MX 16.16.2.
Bug fixes
- Corrected an issue that resulted in the PoE status icons not being displayed in Dashboard for MX95 and MX105 appliances.
- Fixed a case where fragmented IPv6 packets were not being discarded when reassembly could not be completed properly.
- MX appliances will now allow clients to use their link-local addresses to reach an MX appliance’s global address.
- MX appliances will now send an ICMPv6 error message when packet reassembly exceeds 60 seconds.
- Fixed an issue that resulted in DAD not running on the WAN2 interface if it had been disabled and reenabled.
- When an IPv6 packet is received that requires fragmentation, but has incomplete information in its headers, the packet will be dropped and an ICMPv6 error message will be sent.
- Updated the AnyConnect VPN service
- Resolved an MX 17 regression that resulted in Uplink Decisions in the VPN status page showing 0.0.0.0 as the source and destination IP addresses.
- Performance improvements across various configurations and traffic types.
- Improved the reliability of traffic classification decisions made by NBAR traffic analysis engine.
- Corrected an issue that resulted in MX appliances not sending wireless deauthentication frames when mandatory DHCP was enabled.
- Fixed an issue that could result in valid client traffic being dropped after a reboot of an MX appliance if mandatory DHCP was enabled.
- Corrected an MX 17 regression which resulted in USB cellular modems not providing primary or backup connectivity on MX84, MX100, MX250, and MX450 appliances.
- Resolved an issue that could result in the power LED on MX95 and MX105 erroneously not being set to white.
- Fixed an issue on MX67(C,W), MX68(W,CW), MX75, and MX85 appliances that could cause ports to occasionally disconnect and reconnect (“flap”) when connected to some devices.
- Corrected an issue that could result in MTU values being set to 1280 when an invalivd IPv6 ICMP error message specifying an MTU lower than 1280 was received.
- Resolved an issue that resulted in MX appliances dropping traffic that relied on IPv6 static routes to communicate correctly.
- Corrected several issues that could result in wireless clients being unable to successfully connect and communicate on the network.
- Resolved a rare case that could result in a device reboot when FTP traffic was present in the network.
- Corrected an issue that resulted in MX appliances sending ICMPv6 error-replies to multicast addresses.
- Corrected an issue that could result in spurious error messages being generated in the Windows Event Log when Active Directory group policy integration was configured with MX appliances.
- Resolved an issue that could result in an MX appliance expiring a SLACC too early.
- Corrected several issues that could result in MX appliances inappropriately switching between IPv6 routers.
- Improved throughput when a large number of flows were present on the network.
- Resolved an MX 16.16 regression that resulted in Event Log messages for Source IP and/or VLAN mismatch events not populating correctly.
- Corrected an issue that resulted in an AutoVPN peer being unable to ping another peer using the IPv6 version of their L3 VPN IPs when one of the peers was configured to operate in passthrough mode.
- MX appliances will now drop traffic received on the LAN that has a source IP of the IPv6 loopback address.
- MX appliances will now reply to multicast pings to ff02::1 (all-nodes) and ff02:1::1 (all-routers).
- Fixed an issue that resulted in NetFlow reporting an incorrect interface number for LAN ports that had been converted to operate as a secondary WAN.
- Corrected a rare issue that could result in Z3(C) appliances failing a connectivity safety check after upgrading to MX 16 and falling back to their previous version.
- Resolved an issue that could prevent BGP sessions from forming correctly when 1) the MX appliance was configured to operate in NAT mode and 2) only static routes were configured to participate in the VPN.
- Fixed an issue that could result in MX appliances replying with an ICMPv6 “packet too big” error message for messages received with the source addresses of the unspecified (zero) address.
- Resolved an issue that could result in ICMPv6 messages not being emitted.
Known issues
- After making some configuration changes on MX84 appliances, a brief period of packet loss may occur. This will affect all MX84 appliances on all MX firmware versions
- Due to an MX 15 regression, the management port on MX84 appliances does not provide access to the local status page
- Client traffic will be dropped by MX65(W), MX67(C,W), and MX68(W,CW) appliances if 1) The client is connected to a LAN port with 802.1X authentication enabled and 2) The VLAN ID of the port is configured to 16, 32, 48, 64, 80, 96, 112, 128, 144, 160, 176, 192, 208, 224, or 240.
- MX84 and MX100 appliances have significantly reduced VPN throughput.
- There is an increased risk of encountering device stability and performance issues on all platforms and across all configurations.
Other
- Added support for processing IPv6 traffic that has extension headers.
- Added more speed and duplex configuration options for 2.5Gbps-capable ports on the device local status page.
- MX appliances now support forwarding IPv6 traffic that isn’t TCP, UDP, or ICMPv6.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Just to note; I upgraded an MX75 from 17.6 to this release and it required a hard power cycle to bring up the WAN port. I will try some other devices next week.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
So far no issues on the couple of MX67's I have upgraded.
Will try a couple of more models a little later. - Unfortunately I dont have a MX75 or MX85 in the lab ...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
MX250 - seems fine (it was offline for a little while longer then I thought, but .. all good)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
MX100 ok.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
MX75 upgraded from 17.6 without issue here
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Same here, upgraded fine.
Lets see if this fixes the wan port going down/up.
Mx75 port 12 does not indicate poe status(anyone can confirm this?)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@ww my MX75 also had the WAN port (port 2 in my case) go down and I had never had that issue with 17.6. The connection is direct into the ISP's ONT...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Fixed an issue on MX67(C,W), MX68(W,CW), MX75, and MX85 appliances that could cause ports to occasionally disconnect and reconnect (“flap”) when connected to some devices.
Is this the EEE 802.3az issue ? - If it is, didnt know it was also present on MX67 and 68 ... 😕 - But good thing if it is now fixed.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm guessing so, but the release notes are a bit vague on this one. Hopefully someone can confirm soon.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I see that a 16.16.2 has showed up , with the same vague formulation on this fix.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It seems that this "phrasing" is the fix for the EEE problem. I had it confirmed in a mail from support.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
MX67C / MX84 / MX85 upgrade without any hickups.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello, could I ask if you had any issues with the WAN port on MX85 flapping before you upgraded the firmware. I have an issue with WAN port to ISP kit flapping and causing user interupptions. Hoping this upgrade fixes. Cheers!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
....
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Any insights on these two items? Stable release candidate with significantly reduced VPN throughput? After all the 16.16 issues we are going to need some more details!
- MX84 and MX100 appliances have significantly reduced VPN throughput.
- There is an increased risk of encountering device stability and performance issues on all platforms and across all configurations.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
MX75 updated without problems (and no power cycle needed), MX64s are fine. Only my own pair of MX68 didn't update because they state that the dashboard is not reachable on TCP/443 which is obviously not true as I run 16.16 and have MR28 running inside the network.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Connection to Google file stream slowed significantly after upgrading to 17.7, had to roll back.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@joshuathure what model and licence on that MX?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
MX68
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
MX 68 Advanced Security
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Upgraded MX250 over the weekend. Extreme slowness when trying to negotiate an initial connection to any HTTP or HTTPs
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi DavidTX, did you upgrade to 17.7 or 16.16.2 on your MX250? How is the performance? We have MX450 and having lots of performance issues with MX16.16. We are hesitant to upgrade till school testing is over.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
My Infra manager mistakenly went to 17.7 on our production MX250's - big mistake. While things appear functional, outbound web traffic was quite a bit slower for me, sometimes receiving 'this page cannot be displayed'
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
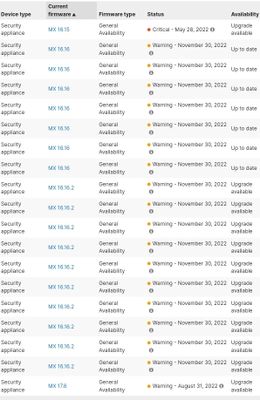
why 17.7 fw upgrades page reports: Warning - August 31, 2022🙄
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I wish there would be more detailed information for every warning/critical label.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The bizarre thing is that there isn't a single version that isn't on a warning or critical...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am now seeing MX16.16.3 (latest patch, Released on June 8th) and MX17.8 (Looks like it was released on June 9th) under Stable Release Candidate instead of MX17.7 and Warning options only to update to MX16.16.3 or MX17.8. I hope the MX17.8 update has resolved the issues in MX16.16 and MX17.7.
-
3rd Party VPN
168 -
ACLs
101 -
Auto VPN
313 -
AWS
38 -
Azure
70 -
Client VPN
428 -
Firewall
704 -
Other
591