We're migrating to the Cisco Community on March 31. The Meraki Community will enter read-only mode starting on March 26 through March 31.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- MX in Routed Mode with No Nat
MX in Routed Mode with No Nat
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
MX in Routed Mode with No Nat
I have a new client (private school) that has an unusual requirement for their MX firewall. Their internal network connects directly to a private circuit to a managed data center provider for Internet access. They currently have an MX100; however, it is in pass-through (bridge mode). The provider requires the school to maintain the assigned the RFC1918 address space to the provider and therefore, they are unable to NAT at the firewall. They desperately need network segmentation and a zone-based firewall to isolate traffic between the internal VLANs. For simplicity purposes, I would like the MX100 to do this.
I would like to change the Meraki MX firewall from pass-through to routed mode; however, the routed mode requires NAT to the uplink (Internet). I thought I read in one of the Beta release notes that this could be done, although, I cannot find the specific article. Any suggestions?
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We ran into this same issue with a client that has a private MPLS connection to an office. The new 15.4 beta code has no NAT in it. We upgraded to it and that fixed our issue.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can't 1:1 NAT anything that needs connectivity to the provider address space?
If this was helpful click the Kudo button below
If my reply solved your issue, please mark it as a solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Unfortunately, no. Almost every device on the network will need Internet access.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We ran into this same issue with a client that has a private MPLS connection to an office. The new 15.4 beta code has no NAT in it. We upgraded to it and that fixed our issue.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Content Engineering Manager
Product Enablement
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@AdamS can you just put specific interfaces into "no-nat" mode, or does the entire MX have to be put into that mode?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Content Engineering Manager
Product Enablement
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@AdamS ...Jaw drop
I'm pretty sure I get the concept of the Beta mode with no NAT mode.
Could you please elaborate a little further for me?
We have dozens of sites with dedicated MPLS only, the data VLAN is Auto-VPN'd back to the data centre concentrator while the voice VLAN is nat'd whereby the MPLS provider then takes the voice traffic out to their media and SBC gateways. Does this mean I can get a private /24 routed to down the link and not nat'd to the handsets?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am also trying to achieve this.
Where I would like the Data network Tunneled to the Data Centre and Voice Network directly routed to the MPLS network.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I've enabled no NAT, but packets destined to private addresses (10.100.1.49) sent to the "uplink2" interface are being dropped. There are no specific firewall rules. (Any/Any is permitted in both directions).
How do we achieve this?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have the same issue at the moment with both 15.4 and 15.7. Source NAT isn't applying from inside to outside and return traffic for these sessions initiated from inside is able to return fine (as you expect for a stateful firewall with no NAT turned on) but sessions initiated from outside are being dropped by the MX.
Support says that when you enable no NAT on an uplink that a permit any/any is added to the firewall policy for outside initiated connections to inside but this appears to be broken. I'm amazed that this hasn't been tested by the developers before allowing the software into the wild.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Owen,
Same problem here. What I've had to do is create a 1:1NAT rule for external hosts to be able to get to internal hosts.
Okay for a dozen or so hosts in some of the small deployments that I have but I'm not looking forward to filling out a whole /24 for a voice network!
Support are working on 15.4 with me and my situations, they've explained that they're are continuing to develop this new no-nat mode in the labs.
Regards,
Ben
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi everyone,
The No Nat feature seems to be really usefull and i want to know when it will available?
In my company, we have a "non risky" politics of firmware upgrades and we use only stable firmware (currently 13.33).
Regards,
Oran
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Content Engineering Manager
Product Enablement
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
Thanks for your answer. I'll follow the next Meraki release until this feature will be available in stable firmware.
Regards,
Oran
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have upgrade to the 15.x firmware but I can't find the No-NAT feature. Where is it located? Or do I need to call support for them to turn it on?
-Since it is pre-beta, I called up support to set it up.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes you'll need to call Meraki support. Make sure you ask them to update these following areas
1. Update the MX to No-Nat 15.x
2. Update the Network dashboard to see and configure No-Nat
3. Apply the No-Nat feature to the interfaces (they need to do this initially)
If you have trouble let me know. Not all of support are aware on how to successfully implement this No-Nat feature
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Adam, any news on the no-NAT feature being released in production firmware? It's been about a year since you last posted about this, and I was wondering if this is still in the roadmap for the MX code. Thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
NO-NAT is available in the 15.x code, which you can deploy to your device right now via the dashboard.
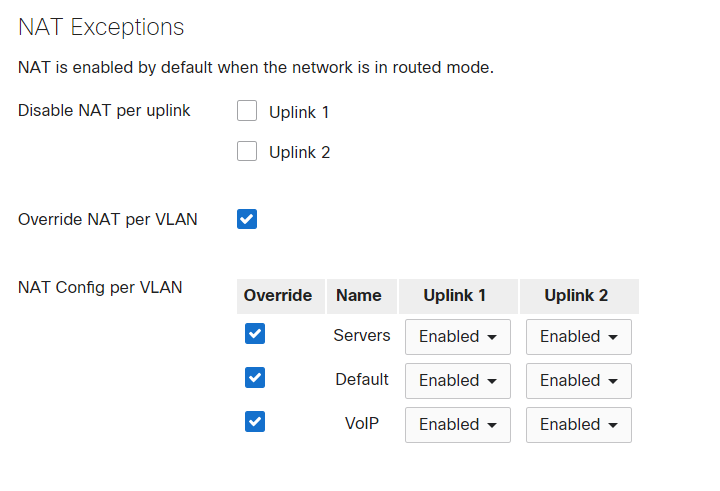
This is a screenshot of the settings relating to it:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This is great. Do you know if we can setup inbound firewall rules when we are in No NAT mode? It would be a shame to have a security appliance with a bunch of important servers behind and no way to deal with granular inbound rules.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
To answer my own question. Upgrading to 15.X does not by default enable the ability to add inbound firewall rules. You still need to open a ticket with Meraki support to get this done. I just did, and it was done quickly.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is the code version you refer to beta or a production release?
thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
15.x code is beta.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks, though I believe the question is still the same, when can we use no-NAT in production environments? I don't think Meraki encourages using beta code in production.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Philip,
My current firmware is 15.33, but I cannot find the option like your screenshot.
Could you advise me on the exact firmware version for this option?
Thank you
SCV
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You'll need to open a support ticket and ask them to enable the NO-NAT mode feature. Then you'll see it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Meraki have to do a separate device-specific change on the backend to the add the "allow any" incoming connection rule.
I had exactly the same situation where I had the no-NAT options enabled but the device was still preventing inbound connections. Once you have the additional change done the firewall tab of the web UI then changes to be similar to the "passthrough mode" UI where it defaults to allow any and you create your restrictions, rather than locking you out of the inbound rules settings.
This was a separate feature and you have to go back to meraki support to get the inbound firewall disabled after the v15 firmware and no-NAT enablement.
We have been using this as our main office router since February with no issues and recently had the v15.7 upgrade which hasn't caused any problems either. It's going to be deployed to another remote site of ours soon because it has worked so well for us.
Now lets hope they can get LAN side link aggregation/LACP support added too and the MX will start to be a useful router!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi ccnewmeraki,
Thanks for the update and advice on how you have successfully enabled the NO-NAT feature.
Support have advised me there is no modification to the inbound rule, yet the NO-NAT mode still is not working for me. I have quoted word for word what you supplied in your last post. Apparently as well the NO-NAT mode does not work on VLAN based exceptions and can only be done per interface. Have you had this issue?
Regards,
Ben
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
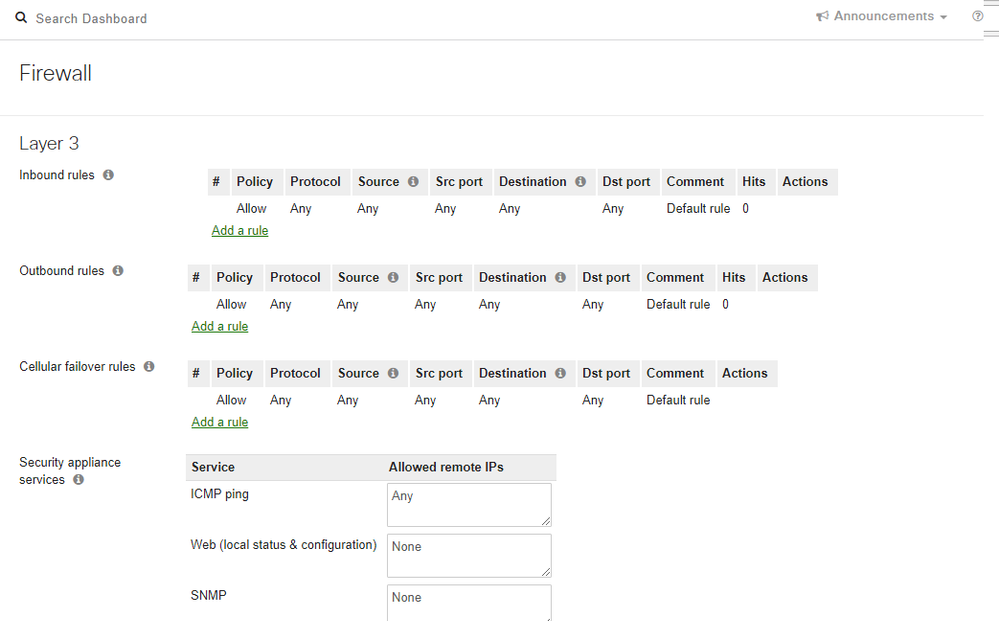
This is how the firewall page looks after they have made the additional change to allow inbound connections:
As you can see the "inbound rules" default rule is "allow any". It has been changed from a stateful firewall to just a firewall.
It sounds like you have the "incorrect" partial configuration that I had (and managed to get resolved) when I initially asked to be included in the NO-NAT beta. It's a very new feature and it's clear that not all meraki case support are experienced with setting it up yet.
I'd ask the meraki support person you are talking with to check their internal NO-NAT documentation which one of the people I was dealing with confirmed has been updated to include instructions on how to do disable the inbound firewall too.
Apparently, they have to apply this change to the serial number of the device rather than the network at the moment (which is odd, as it appears as a difference in the network firewall user interface).
It's very strange that they have separated the two features as the vast majority of people disabling outbound NAT are also going to want to be able to connect to devices behind the LAN interfaces from some place upstream on a WAN link. Strictly speaking, a true L3 router should have no WAN/LAN distinction.
I've not tested out the VLAN based exceptions yet although they are present in the UI so I had assumed they will work.
I have been seeing an issue where I can't ping any of the the LAN interfaces of the meraki from any place upstream of it (ICMP is allowed from any remote IP as you can see). However, I can access the client devices in my meraki created vlans from the upstream router (and our other locations) so it's working for us.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi ccnewmeraki,
Thank you for your extensive reply. I'll get back in touch with Support and hope we can get this sorted out.
Regards,
Ben
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It's ridiculous this seems to be the situation that they are only setting up 50% of NO NAT when you ask for it.
If they come back to you and are still clueless I can PM you my ticket number.
Kind Regards,
Christian
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Christian,
I've sent you a PM, if you could send me your ticket number to pass onto support that would be great!
Thanks,
Ben
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Done.
This was the message in the ticket after I went back to them:
"Hi Christian,
Our documentation was just updated and I'm seeing there is another back-end change I need to add which will disable the inbound firewall for the WAN for a specific MX. Since you've put this device back into production, please let me know if you would still like me to add this and please verify which MX to add it too since this change will be specific to a single device.
Thanks!
Chris Kordus
Cisco Meraki Support"
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Stupid question here but how does one go about setting up and using the No Nat feature. I assume it is something I'd use when the MX is in 'Network Address Translation (NAT)' mode or does it have to be in 'Passthrough' mode? Please advise. I'd like to do some testing on one of my lab MX64's to see if I can use this feature.
If this was helpful click the Kudo button below
If my reply solved your issue, please mark it as a solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Adam you need to be user the beta beta 15.x code. To get this you have to ask support.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Christian,
Support eventually figured it out with the assistance of your ticket number. My whole Organisation dashboard was missing a setting that was necessary for the changes to take affect. Once I then rebooted the MX appliance the NO NAT finally worked as expected and required.
The No NAT has addressed some issues that we were experiencing and believed was caused by NAT.
We still have one major issue which we are still trying to work out with Meraki support.
Has anyone else come across issues with MX routers not handling fragmented UDP packets correctly?
Cisco Traditional ISR's allow up to 24 fragments per packet while a Meraki MX64 only allows up to 4, which is still causing issues with our VOIP handsets.
Thanks,
Ben
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The best fix for the fragmentation is to lower the MTU on whatever the phones are talking to, so that there is no need for fragmentation.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I suspect you life would be easier if you could use a Cisco Meraki switch running in layer 3 mode, and have it do the VLANs and routing ...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That is what I told my client - he should have purchased a router or layer 3 switch instead of turning off an MX84's primary feature sets - kind of a waste IMHO
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have been having i think similar issues when building vpn between a cisco router and the meraki MX. Phase 1 is up. Phase 2 is okay. I tend to think its the ACL limiting this, since from Cisco router am not natting the subnet to the vpn. But i think Meraki is natting LAN VPN traffic.
With the new No-NAT mode, i am i able to exclude the subnet from being natted to a specific destination?
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
306 -
AWS
36 -
Azure
70 -
Client VPN
383 -
Firewall
868 -
iOS
1 -
Other
557 -
Wireless LAN MR
1