- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Best practice to deploy Meraki client VPN to laptops? All methods seem ...
Best practice to deploy Meraki client VPN to laptops? All methods seem to have downsides.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Best practice to deploy Meraki client VPN to laptops? All methods seem to have downsides.
Hi,
Implementing Meraki client VPN atm and all is working fine. Currently in the end stage where I need to deploy the VPN config to the end user laptops running Windows 10. I've tried a few methods but all have their downsides:
- GPO-Network option: not able to deploy IPsec pre shared key or configure split tunnel options.
- CMAK: Even though UserNameSuffix=domain.tld and UserName=%username% are set in config files, the vpn client doesn't use domain credentials by default and user is required to enter them as opposed to GPO-Network option where the connection automatically uses the domain credentials of a logged in user. Also the client wants to dial in through PTSN by default even though Dialup=1, Direct=1, ConnectionType=1 is set in the config files (can be manually fixed to force permanent connection though).
- GPO-Powershell: unable to deploy with required Meraki settings as the script produces the following error:
"The current encryption selection requires EAP or MS-CHAPv2 logon security methods."
Script:
Add-VpnConnection -Name "VPN" -ServerAddress "xxx.xxx.xxx.xxx" -TunnelType "L2tp" -EncryptionLevel "Required" -AuthenticationMethod Pap -UseWinlogonCredential -SplitTunneling -AllUserConnection -RememberCredential -PassThru
Ofcourse, I'm able to manually tweak some settings on the user end to make it work but I would to like do it automated since we have a lot of laptops.
Anyone else found a better approach?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Despite the error - the GPO Powershell method does work. It is not possible to change the Powershell command to avoid the error.
I have some more info here:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Lets clear that up straight away.
First of all an IPSec connection is bought up. Everything that goes over this is encrypted. L2TP is run over this IPSec connection.
100% of everything sent is encrypted.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I m using PowerShell script shared by you and it is working perfect fine for my requirement.
Just need little tweak.
Can we include check in script, that if same client VPN is installed it skip the installation.
What happens, when i push script to all computers, who ever have already installed client VPN got disconnected from VPN and script reinstalled it again on same computer.
I need to put check on script if there is same vpn is installed on client, it skip the installation on same end point and continue with other endpoint who do not have same client vpn installed,
Please suggest something, I not have much exposure on PowerShell.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have downplayed this post and am using CMAK now due to NO Local admin is required as long as you don't use routing table. These Scripts do work but ended up deploying a installer via CMAK.
2 Scripts use GPO to make a Logon Power shell Script first Script launches the second
I found this method will not prompt UAC and it even remembers the Login after the first connection.
initial destination is the client vpn pool the second is how I route traffic back to the On Prem from Azure
Clientvpn1.ps1
_
powershell -ExecutionPolicy ByPass -File '\\path\to\where\second\script\is\Clientvpn2.ps1'
_
Clientvpn2.ps1
$ServerAddress = "vpnaddress.mydomain.com"
$ConnectionName = "Meraki Secure Client VPN"
$PresharedKey = "putyoursecrethere"
$Destination = "10.0.2.0/24"
$Destination2 = "172.27.26.0/23"
Add-VpnConnection -Name "$ConnectionName" -ServerAddress "$ServerAddress" -DnsSuffix "mydnssuffix.com" -TunnelType L2tp -L2tpPsk "$PresharedKey" -AuthenticationMethod Pap -Force
Set-VpnConnection -Name "$ConnectionName" -SplitTunneling $True -RememberCredential $True -Force
Add-Vpnconnectionroute -Connectionname $ConnectionName -DestinationPrefix $Destination
Add-Vpnconnectionroute -Connectionname $ConnectionName -DestinationPrefix $Destination2
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We use the powershell method, but just to note that sometimes Windows 10 updates will cause the settings to get reset and you will need to be able to repush and run the script.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Now that I have 3 MX's deployed (Hub Mesh) I have found that using CMAK for a Windows VPN installer seems to work just fine. I don't have to deal with routes and users don't need Administrator access on device to Install.
Users that dial in to client VPN on my main Hub have access to all the other Hubs in the Mesh.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
CMAK creates a bunch of files. How do you distribute those to users? Zip them up?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
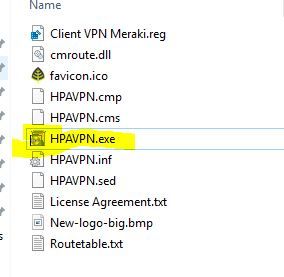
I thought the Same thing but those are just source files for when you build or modify the .exe. so you just distribute the Filename.exe file what I did is put the file on a internal web site and just gave out the URL
URL of web site /vpn.exe file
just need the one file Can customize with company Logos so its not so generic.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I see it is available (CMAK) under "Manage Optional Features" in Windows 10. I think I'll take another look at this tool. Thanks for the tip.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
September 2019
Moving 100 local users from an ASA onto their new Meraki Client VPN connected to their AD...
I want to put this into a login script so when the user logs in the new Meraki Client VPN gets created automatically on lots of computers.
Tell me what you think
$sharedkey = "The PSK here"
$VPNConnectName1 = "Click Here for VPN"
$ServerAddress1 = "Public IP of the MX"
$TunnelType = 'L2tp'
$AuthMethod = @('MSChapv2','Pap')
$EncryptionLevel = 'Required'
$RememberCredential = $true
$SplitTunnel = $true
#Cisco Needs This Registry Entry To Work Properly
$RegistryPath = "HKLM:\System\CurrentControlSet\Services\PolicyAgent"
$RegName = 'AssumeUDPEncapsulationContextOnSendRule'
$Regvalue = 2
New-ItemProperty -Path $RegistryPath -Name $RegName -Value $Regvalue -PropertyType DWORD -Force
#Create VPN Connections
Add-VpnConnection -Name $VPNConnectName1 -ServerAddress $ServerAddress1 -TunnelType $TunnelType -AllUserConnection -AuthenticationMethod $AuthMethod -EncryptionLevel Optional -L2tpPsk $sharedkey -Force
Add-VpnConnection -Name $VPNConnectName2 -ServerAddress $ServerAddress2 -TunnelType $TunnelType -AllUserConnection -AuthenticationMethod $AuthMethod -EncryptionLevel Optional -L2tpPsk $sharedkey -Force
Start-Sleep -Milliseconds 100
#Set Additional Settings
Set-VpnConnection -AllUserConnection -Name $VPNConnectName1 -SplitTunneling $true -RememberCredential $RememberCredential -IdleDisconnectSeconds $IdleDisconnect
Set-VpnConnection -AllUserConnection -Name $VPNConnectName2 -SplitTunneling $SplitTunnel -RememberCredential $RememberCredential -IdleDisconnectSeconds $IdleDisconnect
#Restart computer to load the Cisco Regkey you just updated.
Read-Host -Prompt "Press Enter To Restart Computer"
Restart-Computer -Force
David Burgess
CCNP R&S, Security,
CCNA Wireless, MCNA, ECMS1
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Did this work?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
PowerShell scripts for Windows 10 VPN? Sure, I do it all the time, across hundreds of endpoints now.
My script is a little different from the one in this thread. I modify the rasphone phonebook so the client VPN won't try to use the VPN credentials to access server resources.
I'm gonna go add that reboot reminder to mine now...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Do you have any solutions for Win 7? 🙂
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
My solution for Windows 7 is update your machines to Windows 10 right this second, because a) Windows 7 doesn't have the necessary PowerShell cmdlets, and b) Windows 7 goes end of support on Jan 14, 2020.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
so you are specifying a connection2 but you dont list the variable in the script was this intentional ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Great thread.
I would also recommend you add something to set VPN adapter metric lower than your local adapters. This will help with DNS resolution so that it will always try and resolve through VPN adapter first.
Based on what I see I am guessing this should do it:
(Get-Content -path $PbkPath -Raw) -Replace 'IpInterfaceMetric=0','IpInterfaceMetric=10' | Set-Content -pat $PbkPath
-T800
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Another recommendation is to set your MX to a non standard subnet than consumer routers. We found issues with this mostly on Mac, when they used client VPN and their home router was in the same subnet as the MX Lan then it default resolved locally. Its not a huge deal, but I would say better safe than sorry.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What @SoCalRacer said. Whenever possible, re-IP your work network so it's not 192.168.0.0/24 or 192.168.1.0/24. Avoids a lot of overlap, including third party tunnels to other people who use these subnets.
I've got a client who is stuck using an ASA solely because their location and Corporate both use 192.168.1.0/24, so they need VPN NAT.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
https://www.reddit.com/r/meraki/comments/c0ht6m/meraki_vpn_through_intune/
We're experiencing the same situation the user referenced in link above is.
"Hi,
Has anyone figured a way to enable Meraki VPN on Intune-joined devices?
I'm not sure how to get the EAP Xml parameter..
Meraki MDM also fails to load VPN parameters as it requires a Windows profile (apart from the Meraki Agent).. Apparently, you cannot have two MDM profiles on Windows 10.
There's also the issue of authentication. Meraki does not support Azure Active Directory."
I've tried deploying the VPN using System Manager (Meraki MDM) to no avail due to requiring Windows Profile and we cannot accomplish this due to enrollment with Exchange Online/MS365 Intune.
I've tried configuring the deployment via MS Intune due to the SM limitation but it requires the use of EAP XML which our Meraki VPN relies on L2TP/PSK with AD User Authentication over Radius. We will be using this for MFA and so far so good there.
Anyone have any feedback or suggestions?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
>Apparently, you cannot have two MDM profiles on Windows 10.
That is correct.
>There's also the issue of authentication. Meraki does not support Azure Active Directory."
We are 100% AzureAD joined, and use Azure authentication without issue. Here are the setup instructions.
>I've tried deploying the VPN using System Manager (Meraki MDM) to no avail due to requiring Windows Profile and we cannot accomplish this due to enrollment with Exchange Online/MS365 Intune.
I've written a tool to generate a powershell script to create VPN connections.
https://www.ifm.net.nz/cookbooks/meraki-client-vpn.html
You could configure either to download and run the script as SYSTEM and create the VPN.
If you look at the script closer you'll notice it actually builds the XML for the VPN connection. You could modify it slightly to print out the final XML, and perhaps you could use that.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for all of the tips and suggestions!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Just wanted to reference to this "UserVoice" idea which is that Intune should support configuring VPN w. L2TP-PSK / PAP;
https://microsoftintune.uservoice.com/forums/291681-ideas/suggestions/41712955-enhanced-l2tp-configu...
Please upvote that if you are using Intune and want to easier be able to manage MerakiVPN.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The simple fix is to change the encryption setting after the profile defined it as ‘Optional’
An example;
Add-VpnConnection -Name “VPN Name” -ServerAddress “remote..” -TunnelType "L2tp" -EncryptionLevel "Optional"
Then change values in the pbk file in use;
$rasphone = "$env:USERPROFILE\Appdata\Roaming\Microsoft\Network\Connections\Pbk\rasphone.pbk"
(Get-Content $rasphone) -replace 'DataEncryption=8', 'DataEncryption=256' | Set-Content $rasphone
You need to check your file, but for now Microsoft sets the value to DataEncryption=8 if there is no visible encryption.
MS dont know about the IPSEC solution in Meraki.
Check your value by replace line 2 with this one; Get-Content $rasphone
We've combined some of the scripts referenced in the tread, summarized under, it rolls out an VPN profile to logged-in user, tested Okey in Intune.
The trick is in short, set Dataencrypion to Optinal and then change the pbk file
*****
#Cloudflex AS
# VPN with PAP over IPSEC for Meraki VPN
[CmdletBinding()]
param(
[Parameter()][string]$Name='VPN Name',
[Parameter()][string]$ServerAddress='remote.domain.com',
[Parameter()][string]$PSK='The secret',
[Parameter()][string]$DnsSuffix='remote.domain.com'
)
$NeedsReboot = $false
Add-VpnConnection -Name $Name -ServerAddress $ServerAddress -TunnelType "L2tp" -EncryptionLevel "Optional" -AuthenticationMethod PAP -L2tpPsk $PSK -RememberCredential -DnsSuffix $DnsSuffix -PassThru -Force -Confirm:$false
If((Get-ItemProperty -Path 'HKLM:\SYSTEM\CurrentControlSet\Services\PolicyAgent\' -Name 'AssumeUDPEncapsulationContextOnSendRule' -ErrorAction SilentlyContinue) -eq $null) {
New-ItemProperty -Path 'HKLM:\SYSTEM\CurrentControlSet\Services\PolicyAgent\' -Name 'AssumeUDPEncapsulationContextOnSendRule' -Value 2 -PropertyType 'DWord'
Write-Host 'Please reboot before attempting to connect.' -ForegroundColor Yellow
$NeedsReboot = $true
}
$rasphone = "$env:USERPROFILE\Appdata\Roaming\Microsoft\Network\Connections\Pbk\rasphone.pbk"
(Get-Content $rasphone) -replace 'IpInterfaceMetric=0', 'IpInterfaceMetric=1' | Set-Content $rasphone
$rasphone = "$env:USERPROFILE\Appdata\Roaming\Microsoft\Network\Connections\Pbk\rasphone.pbk"
(Get-Content $rasphone) -replace 'DataEncryption=8', 'DataEncryption=256' | Set-Content $rasphone
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The latest system updates from Microsoft have caused some trouble, listed under you will find the needed fixe to install;
Windows 11, versjon 21H1 (opprinnelig versjon): KB5010795
Windows Server 2022: KB5010796
Windows 10, versjon 21H2: KB5010793
Windows 10, versjon 21H1: KB5010793
Windows 10, versjon 20H2, Windows Server, versjon 20H2: KB5010793
Windows 10, versjon 20H1, Windows Server, versjon 20H1: KB5010793
Windows 10, versjon 1909, Windows Server, versjon 1909: KB5010792
Windows 10, versjon 1607, Windows Server 2016: KB5010790
Windows 10, versjon 1507: KB5010789
Windows 7 SP1: KB5010798
Windows Server 2008 SP2: KB5010799
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you Meraki!!! - https://documentation.meraki.com/MX/AnyConnect_on_the_MX_Appliance
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The windows VPN method is plagued with constant problems. Just when you think you have it right, Microsoft changes something or an update resets your settings and breaks it. as @cwal21 mentions Anyconnect is now available for Meraki, switch to that. You have many more options for managing the VPN well, and most people are familiar with anyconnect from a user standpoint. Update the code on your MX's and give it a try, if you don't have a ton of users the anyconnect licensing isn't too bad price wise.
-
3rd Party VPN
166 -
ACLs
100 -
Auto VPN
313 -
AWS
38 -
Azure
70 -
Client VPN
427 -
Firewall
702 -
Other
588