We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- Re: AnyConnect SAML Group Policy assignment
AnyConnect SAML Group Policy assignment
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
AnyConnect SAML Group Policy assignment
Does anyone know of a way to assign a group policy to a VPN Session via SAML Authentication?
With radius Authentication you can pass back an attribute that would put the VPN Session into a Group Policy.
Is this possible with SAML Authentication as well?
- Labels:
-
Client VPN
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Ruben2 : check this out
https://documentation.meraki.com/MX/AnyConnect_on_the_MX_Appliance/Authentication
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can't do it ... yet.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is this still the case?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It is still the case.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It is still a work in progress.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
".... yet" ... have you heard anything about this being talked about ? 🙂
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Alas it is still a work in progress.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Do you know if an early access release is planned?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have asked this myself. I don't think there is much motivation to do this at the moment.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
have anyone noticed that this (Group Policy) does not even work statically with anyconnect and SAML ?
I just tested with a customer, and the static Group policy in the config (at the very bottom of the page) does nothing.
It works fine in non-SAML ... how strange.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@PhilipDAth Hey Philip, you seemed pretty helpful wanted to ask you about this topic. I am trying to do Cisco AnyConnect w/ SAML authentication with Microsoft Azure.. do you know if this is still a limitation where group policy cannot be applied if SAML is being used?
And if it's not possible, is there any workaround for it? I was looking at Azure, and their conditional access policies don't support time-based restrictions.. which is what I'm trying to implement in group policy.
Our company has a requirement where VPN access has to be restricted from 8am-5pm.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
>do you know if this is still a limitation where group policy cannot be applied if SAML is being used?
It is being worked on, but is not available today.
>Our company has a requirement where VPN access has to be restricted from 8am-5pm.
I haven't tried this - but try configuring the default AnyConnect group policy and put a schedule in there.
You might need to do something like configure the firewall rules to block everything, and then use the schedule to allow access.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It baffles me for how long SAML is already supported for AnyConnect, but group policy support has been missing ever since. It's just not a viable authentication mechanism if you would like to design separate access policies in Meraki dashboard. Hopefully the team at Secure Client puts this somewhere at the top of their list.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We're now headed in a different direction. Going with Fortigate for SSLVPN w/ SAML Authentication to O365. Without rules for vpn traffic, we can't continue to use Meraki.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We are waiting for this very important function too and hope that meraki will implement this soon!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Still eagerly awaiting this as well. Support for SAML assertion attributes, which can be used to make DAP policy selections, has been added in ASA 9.17 (almost 2 years ago!), but still no news on Meraki side. 😞
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This is an essential function we are missing. Come on Meraki team!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This has actually forced us to move on to a different firewall, that supports basic enterprise features like this.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Our company is also in desperate need for this to function. We have this working through ASA but that is the only function of the ASA at the moment since Meraki still doesn't support SAML Groups policies.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Want to raise attention to this issue once more. There is still a need for this functionality to be implemented, so hoping Meraki development team finally takes notice. Authentication & Control methods need to be revamped to be on par with other industry leaders.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If you send an email to meraki-anyconnect-beta@cisco.com with a link to your org dashboard and ask them to enable "SAML AnyConnect Group Policy", then they'll turn it on for you.
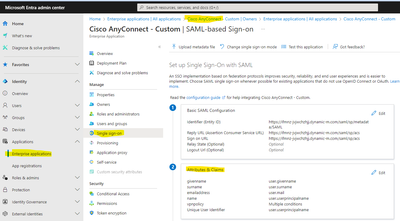
Once enabled you'll see this:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello PhilipDAth,
Thank you for the information. It's good to know that Meraki is working on this feature and that we can use it in beta!
Do you know if we can define multiple group policies for different SAML groups?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oh wow, this would be handy no longer requiring Radius to get this functionality.
I don't know anything of SAML itself.
How can you map Entra ID groups to group policies then?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
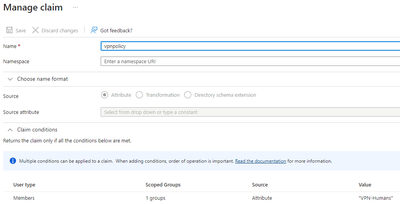
To answer @znet and @GIdenJoe , if you are using Entra ID you can map Entra groups to Meraki group policies. There are several ways of doing it. Basically you pass whatever Meraki group policy you want applied to the user in the SAML attribute (called "vpnfilter" in my example - but you can call it anything you like).
Basically you can say if you are a member of "this" list of groups, apply this policy ("VPN-Humans" in this example). You can keep adding more and more criteria and specifying different Meraki group policies to apply.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@PhilipDAth , Have 4xVMX-Large appliances in Azure, since each vMX-L can only support 500 client remote vpn sessions, to load share 1900 clients between 4 vmx's using traffic manager in azure to do the DNS load balancing.
Does SAML required to add 4 identifiers(Entity ID)&replay URL's for the each vMX DDNS name ?
or just one URL that client use on anyconect client ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Keep an eye out for VMX-XL ... you might be able to get your Meraki rep to give you a discount for the unused portion of your licence against these larger appliances coming out. My guess, pure speculation, I think it might support around 5,000 client VPN users. Most of its limits are about 10x more.
You can get a feel for the XL here:
https://documentation.meraki.com/MX/MX_Sizing_Information/MX_Sizing_Principles#vMX-Series_2
Tricky question about the SAML. Basically this is how it works:
- User connects to MX. MX redirects it to Entra with some session specific information.
- Entra ID sends the use a redirect back to the MX with session specific information.
If you can guarantee the user will end up talking to the same MX both times during this flow, then you should be able to use a single app definition in Entra ID. Note that this will also require you to buy 4 x SSL certificates (one for each MX).
A safe option would be to use the dynamic DNS name, add four apps in Entra ID, and configure "Optimal Gateway Selection" in the AnyConnect client, and let AnyConnect use whatever VPN is responding the fastest.
If it was me - I think I would prefer the safety of OGS.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
>would be handy no longer requiring Radius to get this functionality
One of the nice things is that it doesn't require any compute on-premise to be working. You can have your whole VMWare farm down, you can have all your servers wiped out by CrowdStrike - and you can still VPN in like normal.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oh great. So with this new feature you reference in Meraki dashboard the name of the attribute you have added to the Entra ID users. In this case this is vpnfilter.
And then per group you can define the value inside that attribute to match the group policy name you want applied in dashboard?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Correct.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
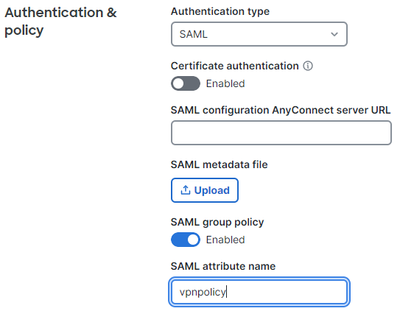
This is a great feature! I was able to add the attribute in the "Attributes & Claims" area of the Entra ID Enterprise App, but cannot find where to reference the attribute in the Meraki Dashboard. I'm trying to use this config to dynamically assign a group policy for the Cisco VPN client / SAML.
Any hint on how to accomplish this in the Meraki client vpn config?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Send an email to meraki-anyconnect-beta@cisco.com with a link to your org dashboard and ask them to enable "SAML AnyConnect Group Policy". Then they'll turn it on for you.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I tried writing that email last week no response unfortunately 😕
Did anyone else had any luck ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have also managed to get support to turn it on before - but many of them don't know how yet. You need to ask for "AnyConnect SAML Group Policy" to be enabled.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I asked support, and they enabled it for me 🙂
Now ... the big question, where to find documentation, because even though you have provided a screenshot from Azure, that really does not tell me, a non-Azure speaking person, much 🙂
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
There is more than one way to do this. Start at https://entra.microsoft.com/, go into Applicatoins/Enterprise Applications/<select your AnyConnect app>/Single Sign On, and edit (2) Attributes & Claims.
Then click "Add new claim". For the name enter "vpnpolicy". Expand "Claim Conditions". Set "User Type" to "Members". For "Scoped Group" select an existing Entra ID group. For the "Source" put "Attribute".
The attribute field is a down down list - but that is just a guide. Instead just type in the Meraki group policy that you want to apply.
Add as many claim conditions as required to match Entra ID groups to Meraki group policies.
I prefix my group policies that are used for VPNs with VPN- but you can use whatever naming convention you want.
On the Meraki side, make sure you put the same claim name in the AnyConnect config, in this case, vpnpolicy.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In your example, Im a little confused how "vpnfilter" is used ... your claimname (in the sceenshots), is "vpnpolicy" ? .. so would that not be the correct config ?
I know its just a screenshot thing .. but just to be sure.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Buggar. Change vpnfilter to vpnpolicy.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Do you know if this can also be done with Duo? If so, I'll also try to activate it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It is much easier doing it with Duo. Define "Role Attributes" so it looks like this:
"VPN-Humans" is the Meraki group policy to apply.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This looks so good; I wish I had this from day one of SAML ...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I only found time today to test this. But where are these Role Attributes configured? I don't see anything in my Duo SSO-Config.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I configure AnyConnect using as a "Generic SAML Service Provider" (this shows all the options).
This is what it looks like for me:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Oh yes, there it is. What a pity that it's not in the "easy" SSO setup. Now I have to look up how to map each attribute. But I got the path I have to follow! 👍
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If I get bored, I'll put in a feature request to Duo to add this to the "easy" setup.
I have previously asked them to add a field for AWS, and they did!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can we achieve the route separation of every group in the Meraki Anyconnect?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can have per group firewall rules, but everyone has to share the same set of routes.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I ended up calling Meraki's support and they were able to enable the feature. It's working like a charm!
They should have this enabled for all organizations. Manually assigning the group policies is not practical, even for SMBs.
This thread is a life saver. Thank you very much for sharing!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Every now and then I try to encourage Meraki to release it as an Early Access feature that can be enabled via the dashboard.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dear @PhilipDAth
any new about early access for this features?
is something that we are looking forward.
thank you
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
While it's not possible to activate by yourselves it is possible to get it. We are using it now and working as it should.
Just create a support ticket in your dashboard and ask to enable Anyconnect SAML group policy.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have not heard anything about it being made available via the Early Access program.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Does anyone have any info on how to do this with Okta?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you all for this information. We are changing from the Meraki VPN solution to anyconnect and we use group policies.
I have just emailed meraki to enable it for us so i hope they do it soon.
Thank you @PhilipDAth for that guide. 🙂
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What is an example scenario to test this implementation?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@PhilipDAth Much appreciated!
I have been used to build most of my VPN connectivity around DAP, so this was a huge problem when we started to move towards Meraki. At the moment I still stay with my old ASA's as VPN Concentrators for only this feature.
Hopefully when Meraki enable the SAML Group Policy thing it will start working!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@PhilipDAt
any new about enable "SAML AnyConnect Group Policy" become General Availability ?
is still Beta ? is there any roadmap ?
thank you
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I believe it is GA now.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It is not showing up on my dashboards. How to get it to appear as expected?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In that case, you'll need to open a support ticket and request that they enable "SAML Group Policy for AnyConnect". If they get stuck, point them to this thread.
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
305 -
AWS
36 -
Azure
70 -
Client VPN
382 -
Firewall
866 -
iOS
1 -
Other
556 -
Wireless LAN MR
1