We're migrating to the Cisco Community on March 31. The Meraki Community will enter read-only mode starting on March 26 through March 31.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Advanced Malware Protection (AMP) retrospect alert
Advanced Malware Protection (AMP) retrospect alert
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Advanced Malware Protection (AMP) retrospect alert
Is anyone else seeing quite a lot of alerts relating to a file that's been identified as malicious in retrospect at the moment?
The file looks to have come down from cdn.office.net
Thanks
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If you're talking about file i640.c2rx with sha256 d73298c7c8b8ce78f7003cf6832a8dd719ab4d240cf3e213fcf8824539c81873 yes, I'm seeing it across multiple networks currently, I'm hoping there more details to come...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks eyre-jr,
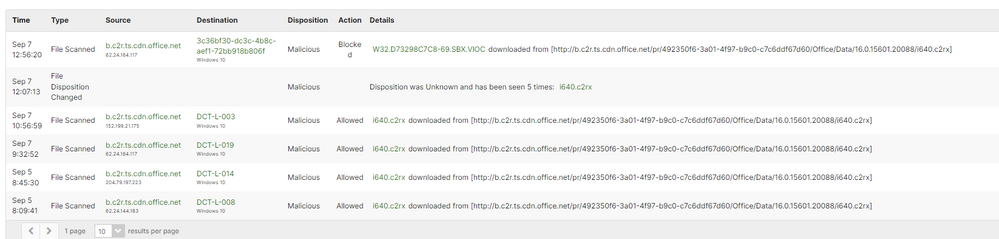
Yes the hash looks the same. Security centre reports the threat as: W32.D73298C7C8-69.SBX.VIOC
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes I have just seen this across many clients. when I look up hash on virus total it says item not found.
Support must be getting smashed as they are not answering....
Update: Got through to support and they are investigating but that this point they think a false positive. They are going to update the banner in security center once they know
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Does anyone have any ideas about what it is, best i can guess is its an O365 update
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes sir...seeing the same thing. Good times.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hey team,
We are seeing some of these pop up, and are currently investigating.
The file seems to be a recent O365 update, and we are trying to understand if this is a false positive.
Please bear with us!
Giac
Appreciate who helps and be respectful of every opinion and every solution offered.
Share the love, especially the Meraki one!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Getting hammered with this also, end users are only surfing "msn.com" for news.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We fall into the "us too" category.
SHA256: d73298c7c8b8ce78f7003cf6832a8dd719ab4d240cf3e213fcf8824539c81873
Filename: i640.c2rx
Type: Zip
Size: 1048576 bytes
URLs:
http://b.c2r.ts.cdn.office.net/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/16.0.15601.20088/...
http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/16.0.15601.20088/...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Same here, it looks a false positive, our antivirus didn't detect it but MX yes, more info:
https://www.joesandbox.com/analysis/347996/0/html
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
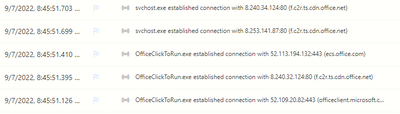
I'm getting slammed with hundreds of alerts this morning as well:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Seeing 131 clients affected across multiple networks.
Threat Name: i640.c2rx
First seen: 7:20AM EST
Size: 1048576 bytes
SHA256: d73298c7c8b8ce78f7003cf6832a8dd719ab4d240cf3e213fcf8824539c81873
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We also have the same issue, ticket reported straight away and at the time they didn't have other reports, looks like they are rolling in now.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
same for me today:
i640.c2rx
waiting to hear good news
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
same here this this is not the 1st time to consider Office update as Malicious
Anyone contacted Cisco Support ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Same......seems to be "Spreading" over our network as clients come online this morning......good times.....good times...
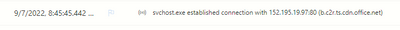
Update: Found this in our Defender logs at same time of alert from Meraki.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
same here too.
source [xxxx].[cdn].[office].[net]...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
+ us too
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
+us too - same file, same pattern, multiple international locations
It would be good to know what Cisco TAC know about this - hopefully a false positive, and the alternative is not very promising.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm thinking that TAC is aware, as Talos is the one flagging it, I think. https://talosintelligence.com/sha_searches
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Same situation
| Malicious | Blocked |
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That's a different SHA256 hash though?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Same issue across multiple clients
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
False positive guys. This is a Microsoft update where they used the file type C2RX which is not on the inspection list in the Meraki AMP.
Use the URL in the alerts to search VirusTotal. VirusTotal - URL - 1a81b30aaf0e0f44b913a3a1f53d1ecd91d274b23d03cf866a4f57d32cb5f487 The hash won't work.
The article about file types in AMP is here Advanced Malware Protection (AMP) - Cisco Meraki
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I think that it is Talos that flagged the file: https://talosintelligence.com/sha_searches Put in the SHA and Talos has that flagged.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi folks! As @GiacomoS said, the Meraki team is aware and investigating this issue currently. You can subscribe to this post for updates, which we will share as we have them. Thank you!
ETA: I'm going to mark this as the solution for now for greater visibility.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
we started receiving these alerts from 12:18, at all of out sites looking at the url we thought it could be a false positive likely the denial of service request for SSL we had a few weeks ago..
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is anyone aware of the effect on the Office clients - do they recover after the failed download?
Is the blocked update a Security or Feature update?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Same here. Slight panic but I'd rather have a few false positives than a single true positive 😉
Coinciding with an internet disruption made me think the worst...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Been working all morning to determine where this is originating from on my network. Wish I had seen the marked as benign earlier.
So we are safe to say it is clear. Great now I will start working on what I intended to this morning
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
For me Meraki determined the downloads as coming from Turkey... The IP is 8.252.195.124 which is registered with a US company but this seems suspicious.
SHA256 d73298c7c8b8ce78f7003cf6832a8dd719ab4d240cf3e213fcf8824539c81873
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
that's a distribution node on Level3's backbone. They have endpoints all over, and are pretty much a tier 0 network
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
306 -
AWS
36 -
Azure
70 -
Client VPN
383 -
Firewall
868 -
iOS
1 -
Other
557 -
Wireless LAN MR
1