- Technical Forums
- :
- Meraki Go
- :
- Re: Compromised printer? Meraki Go
Compromised printer? Meraki Go
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Compromised printer? Meraki Go
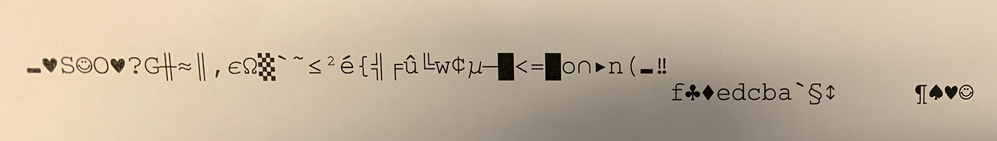
Today the office printer produced three sheets with what seems to be random characters, and in the middle a string random1random2random3random4. This raised a red flag with us. Is this something to be worried about? We use the full stack of Meraki Go (router, switch, AP) with Cisco Umbrella subscription activated for the router. The printer model is Brother DCP-L5500DN, which is connected over ethernet directly to the router.
Here are the prints:
Could this be an attack? Any advice on how to approach this from here on? Thanks!
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
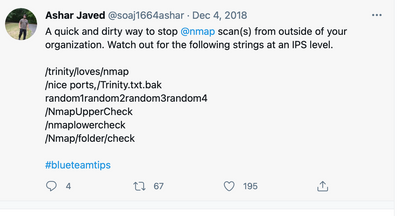
Look what I found. I am going to try this on some of my printers: https://github.com/nmap/nmap/issues/2237
Describe the bug
Aggressive option '-A' on printers produce unwanted print : binary blob with 'random1random2...'.
The printed payload 'random1random2...' is located here : "/usr/share/nmap/nselib/shortport.lua" line 261
To Reproduce
Run the following command on a printer device :
nmap -A X.X.X.34 -vvvvvvvvv -p 9100 --script-trace
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'd give that a very low, almost zero probability of any kind of attack.
I would dig into the printer settings and web GUI to see what you can find about that print job and look through logs, etc. How certain are you that it isn't just a corrupt print job from one of your users?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
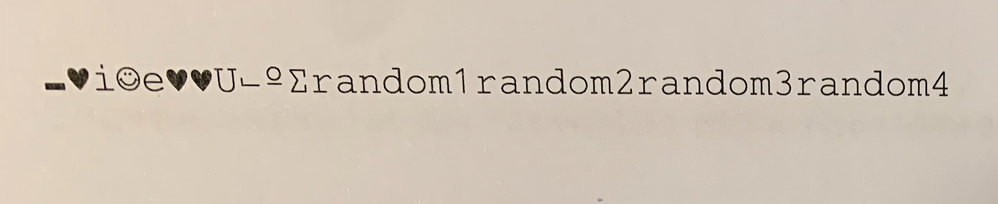
Hi Brandon, thanks for the reply. This print job came out several times when no one gave this command. Also a quick Google search provided a warning about exactly this string: random1random2random3random4. This caught my attention. See screenshot below. Not exactly sure about what to make of this...
Good tip about the print job settings. Unfortunately I reset the printer in a panic move. However if such a print comes out again, I will definitely look into this.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Interesting. I would not expect an NMAP scan to cause a printer to print anything, but I suppose it is possible. Do you have any port forwarding on your firewall to the printer or anywhere else that could even allow outside access into your network? If not, I suppose it is possible someone inside the network was playing around and caused this unintentionally (or intentionally).
Also- this is not really the right forum for Meraki Go. This is "regular" Meraki here. Meraki Go has it's own community: https://community.meraki.com/t5/Meraki-Go-Community/ct-p/go
Best
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Look what I found. I am going to try this on some of my printers: https://github.com/nmap/nmap/issues/2237
Describe the bug
Aggressive option '-A' on printers produce unwanted print : binary blob with 'random1random2...'.
The printed payload 'random1random2...' is located here : "/usr/share/nmap/nselib/shortport.lua" line 261
To Reproduce
Run the following command on a printer device :
nmap -A X.X.X.34 -vvvvvvvvv -p 9100 --script-trace
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Bless you! This explains it all. I certainly did not expect this. The reply from my colleague on our Slack channel just now: "oh yeah, today I ran a few nmap scans".
(Yes... I know)
In any case, maybe this thread can be useful for some others in the future. Will stick to the Meraki Go community from here on. Thanks for the help, Brandon!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What a fun read 🙂 glad the mystery has been solved!
Who would have thought an nmap scan would cause a printer to spit out garbage 😄
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I've just moved this post over to the Meraki Go forum; thanks for the heads up, @BrandonS!
New to the community? Get started here