- Technical Forums
- :
- Wireless
- :
- Re: Meraki Wi-Fi DHCP/WLAN Options versus SonicWALL
Meraki Wi-Fi DHCP/WLAN Options versus SonicWALL
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Meraki Wi-Fi DHCP/WLAN Options versus SonicWALL
Greetings,
As I continue on my bumpy road of Meraki discovery, I've again needed to pull off to the side of the road and make sure I'm not holding the map upside down.
In this case, I'm looking to setup multiple Wi-Fi SSIDs within any given environment. With SonicWALL, I'd simply create the required zones and interfaces, then create the virtual access profile and groups. The end result would be an access point (or more) getting an address (from WLAN pool) from the router, broadcasting 3 Wi-Fi SSIDs with specific subnets (again, provided from the router). For example, I'd set a location up with the following:
Secure Wi-Fi, broadcast, 2.4 and 5GHz, 10.50.30.0/24 (DHCP scope 10.50.30.30-10.50.30.240), WPA2, specific content filter policy
Therap Wi-Fi, hidden, 2.4 and 5GHz, 192.168.0.0/24 (DHCP scope 192.168.0.30-192.168.0.240), WPA2, specific content filter policy
Client Wi-Fi, broadcast, 2.4 and 5GHz, 10.11.30.0/24 (DHCP scope 10.11.30.30-10.11.30.240), WPA2, specific content filter policy
WAP(s) would be on the 10.40.30.0/24 network.
With Meraki, I'm struggling to create the same setup WITH content filtering. What am I missing? What is Meraki's plan with content filtering? For our environments, our Secure Wi-Fi has strict content filtering, while Therap and Client have reduced, but still present, content filtering. None of our Wi-Fi interacts with the wired LAN environments, which also have their own content filtering rules. We have VERY different user groups for each environment (with some crossover), so different content filtering rules are important. With Meraki, it seems to be more "all or nothing". Currently, we don't use AD or RADIUS authentication. I expect that we'll implement AD and RADIUS, but we're still going to have networks that don't rely on either.
I appreciate any assistance that can be provided.
Thank you,
Jeremy
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can do this using Group Policies. Content Filtering rules can be set in a group policy, and you can then apply the GP to the MX VLAN. Naturally, you'll need to have your SSID's in bridge mode set to the appropriate VLAN so the SSID hits the desired GP.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for the reply.
I had previously tried utilizing GP, but couldn't find a way to have the separate networks and apply them... and I still can't. I don't see how using bridge mode works for this, but I'll keep investigating. I'm obviously missing a step... or more.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
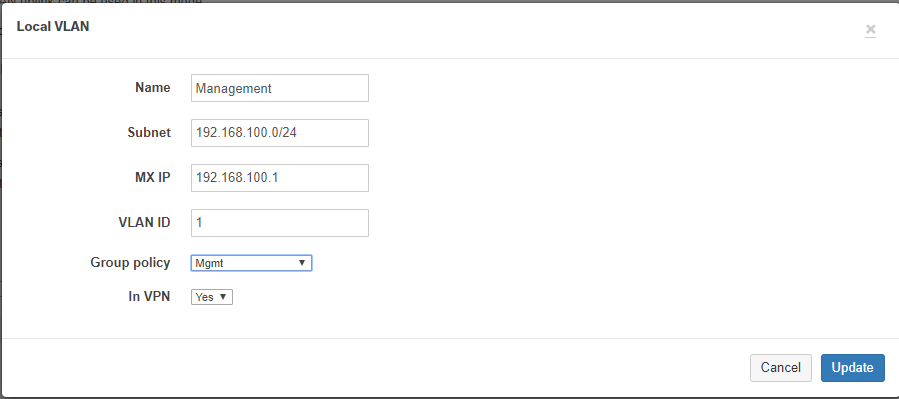
Let's say you have an SSID called "DunJer's Radical Wifi". Under Wireless --> Configure --> Access Control you then configure that SSID to bridge to VLAN 1 (for example). Next, create a Group Policy under "Network-wide --> Configure --> Group policies" and set up the Content Filtering the way you like. Now on the MX you go to "Security appliance --> Configure --> Addressing & VLANS" and in the Routes section for the VLAN you add the GP to that VLAN.
If you do it this way you bridge each SSID into a different VLAN, and you apply a unique GP to each VLAN giving you the ability to apply policies to each group of users. Every user who connects to "Dunjer's Radical WiFi" is placed into VLAN 1 and will be subject to the content filtering for that VLAN.
Does that help?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Perhaps it is just the verbiage that I get hung up on. I'd done the VLAN and GP creation, but it was the assigning of it that was causing me grief. So, in this case, as one of my defined VLANs is 101, within the SSID config page, I'd select Use VLAN tagging and enter 101 in the box next to All other APs?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
SSID configuration applies to all APs in the network automatically unless you configure exceptions Wireless>SSID Availability
If this was helpful click the Kudo button below
If my reply solved your issue, please mark it as a solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Adam On the "Access control" page the settings only apply to the SSID you have selected in the dropdown.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@jdsilva Right, I thought he was asking if it had to be configured on each AP. You are correct. Setting applies to whatever SSID selected in the dropdown.
If this was helpful click the Kudo button below
If my reply solved your issue, please mark it as a solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content