Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Wireless
- :
- Re: COnfiguration question with MX MS and MR
COnfiguration question with MX MS and MR
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
COnfiguration question with MX MS and MR
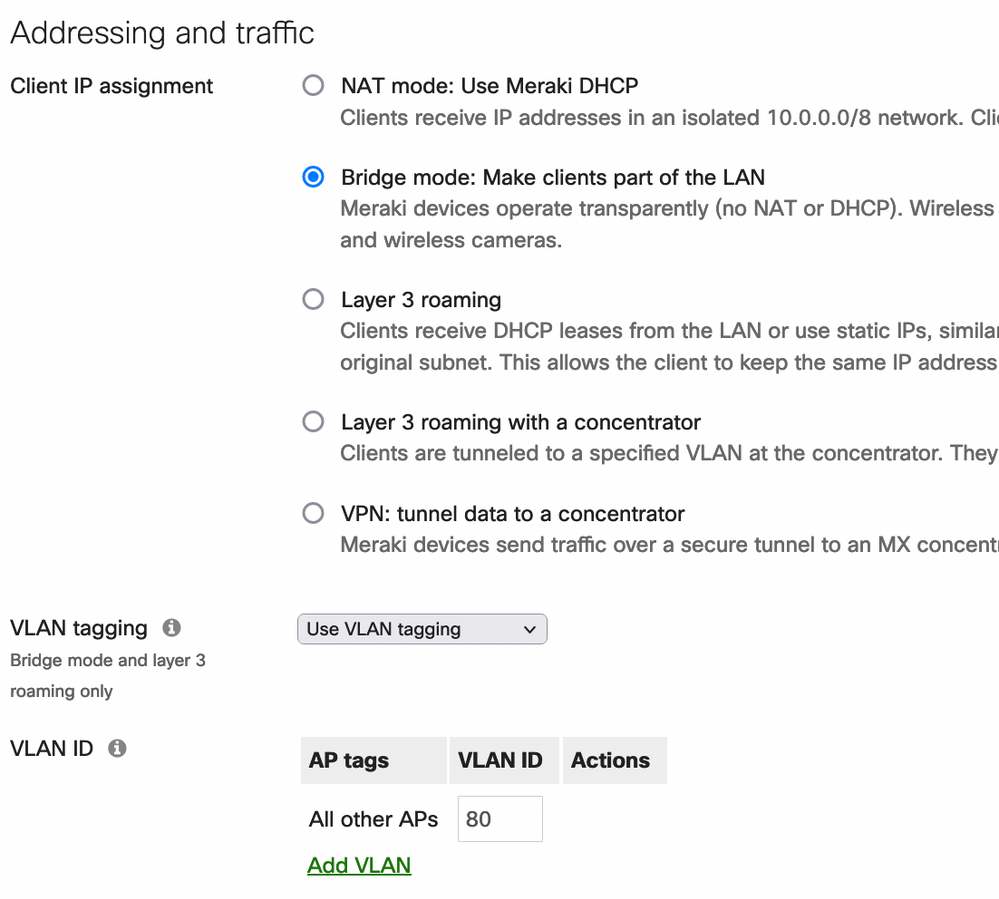
Take a look at screenshot. I want to setup my MX to handle all the DHCP services. I am trying to figure out how to create the SSIDs on the MR to correspond to the VLAN created on the MX.
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That is tunneling the SSID to your MX. That is typically used for remote teleworker deployments where the AP is remote and tunnels over the internet back to the MX. I wouldn't use that mode in your topology.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Make the port on the MX a trunk. Make the ports of the switch connected to the MX and the MRs trunks. Last, on the SSIDs use bridge mode and specify the tagged VLAN. That'll do it.
Here's an example of my SSID putting clients on VLAN 80.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I actually got it to work a different way before I saw your post. I want to decrease the size of my broadcast domain, and increase security. So if I choose the L3 roaming with a concentrator. Doesn't that do what I need it to do?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That is tunneling the SSID to your MX. That is typically used for remote teleworker deployments where the AP is remote and tunnels over the internet back to the MX. I wouldn't use that mode in your topology.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Also, take a look at this screenshot of my MX. It says Native VLAN is 120, why can't it be 160?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can edit that port and choose the native vlan. Also change it on the switch side to the same vlan
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Another ? is that I can't seem to ping any of my MX ip's from the 140 vlan wirelessly... Perhaps something needs to be configured on the switch?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I was able to update my native vlan to the choice of my choosing being 160. I was able to change the SSID traffic to go via bridge using a vlan ID, instead of the L3 roaming option.
However, I still can't ping any of the gateway's of the vlans. Thoughts?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
On page Wireless > Firewall & traffic shaping is the first rule showing as Deny or Allow? It needs to be Allow if this is an internal/employee SSID.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks first rule shows Deny, but how do I specify which wireless clients can access the LAN, and what exactly is the LAN? so I know which network?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Local LAN is a default object for subnets 10.0.0.0/8, 172.16.0.0/12, 192.168.0.0/16. So you want this set to Allow so clients can access internal resources. If you want to lock things down you can add more explicit rules or do it at the MX.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks, I want to lock it down more, really what I am trying to do is lock down the network subnet by vlan.
SO is it best to do it at the MX? For example. I don't want these three subnets to be able to access the LAN.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I wonder why I can't ping the NVR at 10.10.120.4 or a camera at 10.10.130.3 on the 10.10.140.0 subnet???
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
My problem is 10.10.120.4 is showing VLAN 160 in the arp table, and it should be 120.