- Technical Forums
- :
- Security & SD-WAN
- :
- VPN clients connect to MX100, act as if they are split tunneled.
VPN clients connect to MX100, act as if they are split tunneled.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
VPN clients connect to MX100, act as if they are split tunneled.
VPN clients connect to MX100, act as if they are split tunneled.
We have most of our Meraki VPN clients connecting to the MX 100 just fine. But their traffic does not all flow through the VPN to the MX. The clients all have the default setting "Use default gateway on remote network" selected.
I really need all traffic to flow through the VPN to the MX for filtering.
Client VPN connections that have their local LAN subnet as 192.168.1.0/24 then cannot reach any resources on the corporate internal 192.168.1.0/24 subnet. Because the local LAN uses the DG of itself, most of the time its 192.168.1.1.
How can I make the Meraki Client VPN settings on Windows 10 (1803) use only the VPN connection for all traffic?
Example: Users log into their computers. Click on the “connect” to connect their computers to the Meraki MX100 through the configured Meraki Client VPN. They connect to all but one office and can use most resources on most subnets fine. Except when they have a matching subnet they use at home that matches with one at the other offices. Also their internet traffic also goes through the Home LAN network router instead of through VPN to tunnel. Acting like it is split tunnel but by settings on the client appear to be set for non-split tunnel.
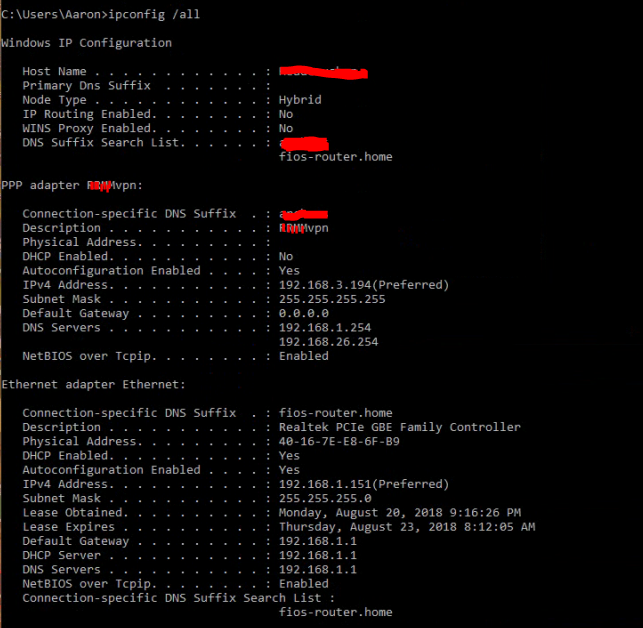
The Ipconfig /all on the client is:
On the MX100 the client subnet is 192.168.3.0/24.
Nameservers: 192.168.1.254 and 192.168.26.254
Active Directory authentication is turned on and authenticating with AD.
There is a static route to the office that has 192.168.1.0/24 listed in the MX100 and all other subnets internally connect to that subnet without an issue.
From the MX100 I cannot ping the 192.168.3.194 client either.
However, on the Z3 teleworker appliances; I just select default route on the site-to-site and then done, they work fine.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We've run into this in the past if I'm on the same page as you.
Remote user connects to Wi-Fi and receives a 192.168.1.0 network address and gateway
Remote user connects to VPN, but cannot see company resources on the company 192.168.1.0 network
Solution is the change the local routers DHCP and Gateway settings. The local router, which I'm guessing is for the local ISP like a Cable or DSL modem, will always try to use the local network it's connected to over the company network at the other end of the tunnel.
For the 192.168.3.0 network issue if I had to guess it's possible there is a second network like Guest built into the modem. I would check the config on that device and make changes as needed. Like I said it sounds very much like a problem I've seen several times and changing the modem/routers config was the easiest way to fix it.
Hope that helps
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You are correct MMoss on your analysis.
My remote users will use their personal LAN networks to connect to their Wi-Fi. My own home local LAN is also similar. We get the default subnet 192.168.1.0/24 with DG at either 192.168.1.1 or 254.
On my home network I can change it to whatever I need to make it work. But I don't have access to other users personal or even public LANs they connect to before connecting the VPN.
Changing the office IP from 192.168.1.0/24 to something else was discussed and almost implemented back when we used Barracuda devices and had similar issues. We moved to Meraki about four years ago and everything worked good on the Meraki's until just recently.
I am trying to track back Windows updates somewhere between Windows 10 1801 and 1803 builds is when we noticed this starting. I also looked at the 192.168.3.0/24 on my local LAN to see if there was a guest or other subnet playing. Nothing on either.
DNS works on client. It resolves names on the corporate subnet 192.168.1.0/24 just fine. Since it does get the DNS servers from MX. But will not ping.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If there is a 192.168.3.0 network local to the MX side of the VPN then it's the same issue but in reverse. The ping doesn't traverse the VPN but tries to ping a device on the company LAN.
The only options I can think of are using ipv6.
Setting up the VPN to use the DNS on 192.168.26.0 and then assigning a second IP address to the servers or adding a second virtual NIC off the 192.168.1.0 and 192.168.3.0 networks.
Finally windows has the ability to set static routes. I dont know if you can set one of those up as a type of gre tunnel where the traffic would be sent over the VPN first and then it would route to the IP from the company gateway. Problem with using a static is it'll affect traffic on and off of the VPN unless its added and removed after each use unless you can set the source network. I've not worked with it in a very long time so I'm throwing it out as a hail mary. Windows can do some routing on it's own so it may be an option buried in there.
-
3rd Party VPN
169 -
ACLs
102 -
Auto VPN
323 -
AWS
39 -
Azure
73 -
Client VPN
449 -
Firewall
651 -
Other
603