- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Uplink traffic MX
Uplink traffic MX
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Uplink traffic MX
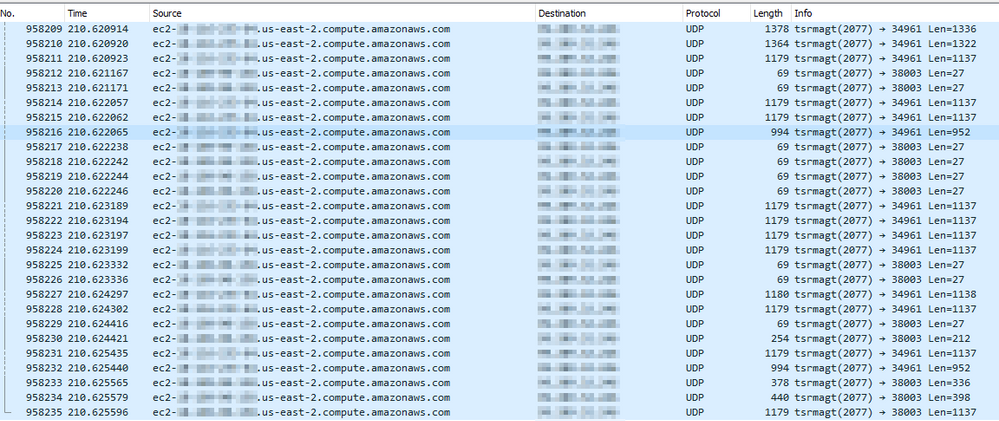
I see a lot of ec2-xxx-xxx-xxx-xxx-region-compute.amazonaws.com traffic on WAN ports pcap capture on MX appliances. Infact all Traffic on secondary WAN is from AWS. Any idea why this would be happening. I have no VPN tunnel setup with AWS or have any traffic coming from AWS instances.(pic attached)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I think you should open a support case.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I was wondering could get some advice from the forum on probably some AWS Direct Connect connection or if anyone has seen this before. I think if you don't have an answer it's better to keep shut than advising to open a support case.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is it terminating to anything on the LAN side? I notice a lot of hacking/scanning garbage from AWS in general so maybe just that? I would want to see a LAN side pcap to and from that AWS address to understand better.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If I'm reading the pcap correctly, all of the packets are sourced from a known port and designed for an ephemeral port. That would typically indicate that something in your LAN side initiated the connection.
As @BrandonS suggested, a LAN side capture might yield done better information.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
LAN side did not show any AWS public ip.I am checking with AWS support and will update this thread.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
More than likely, Meraki is simply hosting part of its cloud infrastructure in Amazon AWS.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for the info so far, I did check with Meraki Support and was told the public IP mentioned was not used by Meraki in AWS. Will check with AWS support.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Checking with AWS it is identified that there are EC2 instances from some account which have theses ips.AWS cannot reveal the account holder or their location as per their policy. I have blocked the xxx.xxx.xxx.xxx/32 public ip in layer 7 rules (ip range section) but still see traffic visible on WAN internet pcap capture on Meraki Dashboard. How else could I block "Internet Protocol Version 4, Src: ec2-xxx.xxx.xxx.xxx.us-east-2.compute.amazonaws.com from hitting our MX. We do not have advanced security features option.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@TheAlchemist you cannot stop any internet traffic hitting your MX from the WAN side unless you use a cloud/ISP proxy or firewall. Anyone in the world can try to send traffic to you. Is your public IP one you have had for a while, or a new one?
-
3rd Party VPN
166 -
ACLs
100 -
Auto VPN
311 -
AWS
38 -
Azure
70 -
Client VPN
427 -
Firewall
695 -
Other
582