We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Simulate Intrusion Attack
Simulate Intrusion Attack
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Simulate Intrusion Attack
Hello Cisco Meraki Community,
We have a mix of MX67C, MX84 and MX100 deployed at our branch offices with Advance Security license. I wanted to test intrusion prevention by simulating an attack. Can anyone share the tools and applications they used? I would like to test one of the offices and safely simulate an attack. I would like to see how the alert looks like and the behavior of the MX. Any information is appreciated. Thank you.
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Network & Security Engineer
CCNP | JNCIP-SEC | CMNA
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I've used EICAR files to test AMP in the past:
http://2016.eicar.org/85-0-Download.html
But you may be looking for something to test the Snort IDS/IPS module?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm sure there will be tools to help you in Kali and Metasploit, but I have no experience myself.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Kali is now available integrated into Windows 10
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Kali is now available integrated into Windows
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@mags If you want to get this done and don't have time I suggest you approach a cyber security testing company, yes they are expensive however if you just want to test one or two simple functions I cannot imagine it being to bad cost wise.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi BlakeRichardson,
That would be the last option I would like to take because it will be a lot more complicated to get third party involved. Thanks for your suggestion.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Network & Security Engineer
CCNP | JNCIP-SEC | CMNA
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Metaspolit Community edition is good - but be prepared for an uphill learning experience.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi PhilipDAth,
At the moment, I don't have much time to spare to learn Metasploit but I'll put that in the list of nice things to learn in the future. Thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Johnfnadez,
Is it just simply opening notepad.pw in a webrowser? I tried to do it but nothing comes up on the MX email alerting or Security Center.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
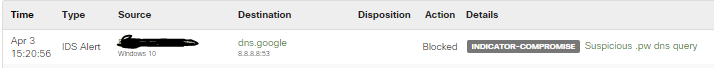
Yes!
Look my MX 🙂
Try to check you Policies in your group policies that you have assigned in your device or VLANs
Network & Security Engineer
CCNP | JNCIP-SEC | CMNA
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Regards!
Network & Security Engineer
CCNP | JNCIP-SEC | CMNA
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
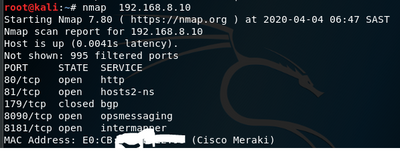
i just did a simple network scan using nmap on kali linux on one of my sites
shouldnt this type of scan be considered as intrution? nothing shows up in the event log and nothing under security center also
below is if i do a scan on my home mx but within the lan
in my mind i wouldnt want anyone whether external or internal to be able to run scans
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can't do anything to stop an nmap scan. I guess you could say after you have seen so many syn packets from a specific host to block further syn packets, but it is pretty easy to get a false positive and block legit traffic.
nmap is a scanning tool. It doesn't actually utilise a compromise to try and gain access or run code.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The website popped up and my security log on my MX shows that a suspicious .pw query was blocked.
If the DNS query was blocked, why could I get to the site?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Johnfnadez,
In Security & SD-WAN > Threat Protection, I have IDS/IPS mode intially set to detection and ruleset to connectivity. I changed it to prevention and security with the thought that it will capture the notepad.pw malicious DNS query but no joy. The client I am using for testing is not assigned to any Group Policy so I think default policies will apply.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
After changing the Threat Protection settings, did you make sure that the MX had updated it's settings?
Sometimes it takes a few minutes for the setting to apply, especially firewall and security rules.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi DHAnderson,
I saw the alerts in Security Center this morning when I checked. I tested again and it is now showing as suspicious .pw DNS query.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Johnfnadez,
I got the alerts now showing in Security Center. I thought there would be an email alert generated as well but there wasn't any. Thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
306 -
AWS
36 -
Azure
70 -
Client VPN
383 -
Firewall
868 -
iOS
1 -
Other
557 -
Wireless LAN MR
1