- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Setup a non meraki vpn site-to-site
Setup a non meraki vpn site-to-site
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Setup a non meraki vpn site-to-site
Hi All,
I’m trying to create a Ubuntu VPN Gateway to connect to Meraki MX 65 VPN Service.
Basically my network is simple and has following configuration:
Meraki VPN Appliance is located on network 192.168.1.0/24
The Ubuntu VPN Gateway is located at 192.168.2.0/24 and has the following ip address 192.168.2.254
When the vpn service on gateway I can ping to all host that are located at 192.168.1.0/24 network.
But from a client located at network 192.168.2.0/24 example 192.168.2.101 I cannot ping to any host located at network 192.168.1.0/24.
I set up a static route on Meraki to respond request from 192.168.2.0/24 to sent to vpn appliance 192.168.1.254
Please help to troubleshoot the issue in order to fix
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
your mx is in routed mode?
192.168.1.x and 192.168.2.x are interfaces on the mx?
what static route did you set exactly?
you have a small drawing maybe?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello @ww, Here you found the answers of the questions,
your mx is in routed mode?
Yes, my mx is in routed mode and has vpn site-to site configured 192.168.1.x and 192.168.2.x
are interfaces on the mx?
192.168.1.x is lan of mx
192.168.2.x is tp-link 3420 lan
what static route did you set exactly?
i have configured the following static route on mx subnet next houpe 192.168.2.0/24 1921.168.1.254 you have a small drawing maybe? right now i dont have a draw
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This link may help regarding connecting non-meraki VPNs with Meraki's Auto-VPN.
https://www.willette.works/merging-meraki-vpns/
AutoVPN + non-Meraki VPN Integration Considerations
Only subnets local to the MX can be advertised to the remote Non-Meraki VPN peer. The subnets specifically selected as Use VPN, yes on the Security appliance > Site-to-site VPN configuration page will be included as the local interesting traffic in the IPSec exchange.
Non-Meraki VPN routes are not advertised to OSPF or BGP peers.
Non-Meraki VPN remote subnets cannot overlap with existing local, static, or AutoVPN routes. Doing so generates a Dashboard validation error when trying to save the configuration.
Non-Meraki VPN routes are not advertised to AutoVPN peers.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Firewall enabled on Ubuntu appliance?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The ubuntu box was connecting to MX using client vpn that require username and password.
What i want is connect Ubuntu with Meraki via site to site VPN.
I made some changes in ubuntu. and now i wont be able to connect
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The firewall is not enabled on router.
i made some changes and seems the connection is estabelished and then goes down.
Here the logs:
sudo ipsec up vpn2
initiating Main Mode IKE_SA boane-vpn[1] to 165.90.79.78
generating ID_PROT request 0 [ SA V V V V V ]
sending packet: from 192.168.2.254[500] to 165.90.79.8[500] (212 bytes)
received packet: from 165.90.79.8[500] to 192.168.2.254[500] (156 bytes)
parsed ID_PROT response 0 [ SA V V V V ]
received XAuth vendor ID
received NAT-T (RFC 3947) vendor ID
received DPD vendor ID
received FRAGMENTATION vendor ID
generating ID_PROT request 0 [ KE No NAT-D NAT-D ]
sending packet: from 192.168.2.254[500] to 165.90.79.8[500] (244 bytes)
received packet: from 165.90.79.8[500] to 192.168.2.254[500] (228 bytes)
parsed ID_PROT response 0 [ KE No NAT-D NAT-D ]
local host is behind NAT, sending keep alives
generating ID_PROT request 0 [ ID HASH N(INITIAL_CONTACT) ]
sending packet: from 192.168.2.254[4500] to 165.90.79.8[4500] (100 bytes)
received packet: from 165.90.79.8[4500] to 192.168.2.254[4500] (92 bytes)
parsed ID_PROT response 0 [ ID HASH V ]
received DPD vendor ID
IKE_SA boane-vpn[1] established between 192.168.2.254[192.168.2.254]...165.90.79.8[165.90.79.8]
scheduling reauthentication in 3337s
maximum IKE_SA lifetime 3517s
generating QUICK_MODE request 1050748777 [ HASH SA No KE ID ID NAT-OA NAT-OA ]
sending packet: from 192.168.2.254[4500] to 165.90.79.8[4500] (356 bytes)
sending retransmit 1 of request message ID 1050748777, seq 4
sending packet: from 192.168.2.254[4500] to 165.90.79.8[4500] (356 bytes)
received packet: from 165.90.79.8[4500] to 192.168.2.254[4500] (92 bytes)
parsed INFORMATIONAL_V1 request 3971823612 [ HASH N(DPD) ]
sending retransmit 2 of request message ID 1050748777, seq 4
sending packet: from 192.168.2.254[4500] to 165.90.79.8[4500] (356 bytes)
received packet: from 165.90.79.8[4500] to 192.168.2.254[4500] (92 bytes)
parsed INFORMATIONAL_V1 request 4073732075 [ HASH N(DPD) ]
received packet: from 165.90.79.8[4500] to 192.168.2.254[4500] (92 bytes)
parsed INFORMATIONAL_V1 request 3012882346 [ HASH N(DPD) ]
sending retransmit 3 of request message ID 1050748777, seq 4
sending packet: from 192.168.2.254[4500] to 165.90.79.8[4500] (356 bytes)
received packet: from 165.90.79.8[4500] to 192.168.2.254[4500] (92 bytes)
parsed INFORMATIONAL_V1 request 3714477588 [ HASH N(DPD) ]
received packet: from 165.90.79.8[4500] to 192.168.2.254[4500] (92 bytes)
parsed INFORMATIONAL_V1 request 3520459203 [ HASH N(DPD) ]
sending keep alive to 165.90.79.8[4500]
sending retransmit 4 of request message ID 1050748777, seq 4
sending packet: from 192.168.2.254[4500] to 165.90.79.8[4500] (356 bytes)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
#/etc/ipsec.conf
conn %default
ikelifetime=60m
keylife=20m
rekeymargin=3m
keyingtries=1
keyexchange=ikev1
authby=secret
ike=aes128-sha1-modp1024,3des-sha1-modp1024!
esp=aes128-sha1-modp1024,3des-sha1-modp1024!
conn vpn2
keyexchange=ikev1
left=%defaultroute
auto=add
authby=secret
type=transport
leftprotoport=17/1701
rightprotoport=17/1701
rightsubnet=192.168.1.0/24
rightid=165.90.79.78
# set this to the ip address of your meraki vpn
right=165.90.79.78
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
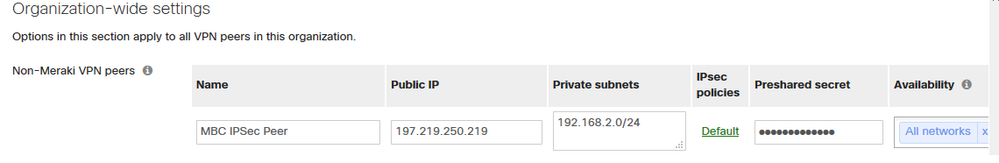
the meraki configuration of non-meraki-devices
-
3rd Party VPN
167 -
ACLs
101 -
Auto VPN
313 -
AWS
38 -
Azure
70 -
Client VPN
428 -
Firewall
703 -
Other
588