Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Sanity check for AutoVPN Hub and Spoke with Default route, and disabled net...
Sanity check for AutoVPN Hub and Spoke with Default route, and disabled network.
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sanity check for AutoVPN Hub and Spoke with Default route, and disabled network.
I have setup quite a few AutoVPN networks normally split tunnel with Adv. Sec on MX's.
But in this case the customer wants to run Full tunnel (only enterprise license) for networks (and that's fine) but they want ONE network to just have local internet breakout (no security , or as much as the Enterprise lic can give them, and of course no access through AutoVPN).
This should be pretty simple, just set that network to disable on the Site-to-Site page right ? ... right ?
The problem is that when i take this network out of AutoVPN (set that specific network to disabled) and try to ping from the MX (source "the internet only VLAN") I see these packets on the central HUB MX (in a packet capture).
I have NO idea why, this should not happen right ?
Or is this because I use the MX status page to test out connectivity (some random issue no-one was aware of).
Just wondering.
Or have I missed something ?
https://documentation.meraki.com/MX/Site-to-site_VPN/Site-to-Site_VPN_Settings
Documentation seems to agree with "how I think this should work".
Thanks
Thomas
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, clients on that VLAN should work and would NAT out fine. If they're not then something else is wrong in the config or topology.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
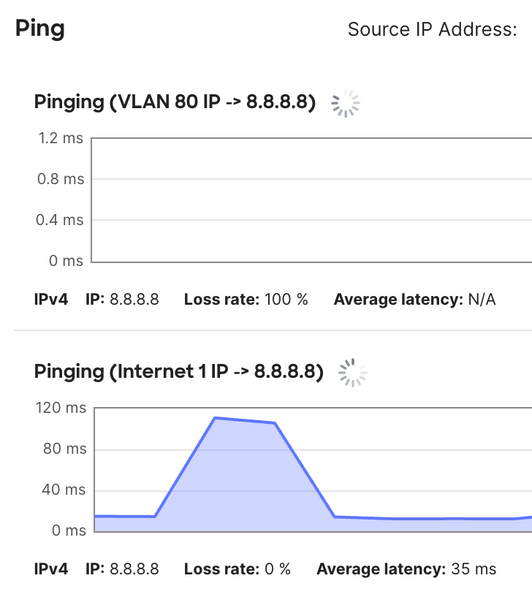
If I'm understanding your scenario and test of pinging from a MX VLAN interface to the internet that's not supported as the traffic is not natted as noted here.
For example this is from my MX
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
But It should not be seen on the vpn hub.
Afaik it leaves the wan interface with the vlan ip, but does not get response because there is no route back on the router behind the mx nat interface.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We don't know what other routing is in play here. My point is regardless that ping test isn't valid.
There'd still be a 0.0.0.0 default route to the hub even though the VLAN isn't VPN enabled. And because the MX VLAN interface doesn't NAT it's hitting that hub default route.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Lol .. I must never have tried to ping from a source vlan towards the internet on an MX .. how strange.
But , just to check my sanity.
This should work (internet access) for a client that connects to that VLAN right ?
And me seeing the ICMP packets on the HUB from this VPN disabled source VLAN is what ... a fluke ... ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, clients on that VLAN should work and would NAT out fine. If they're not then something else is wrong in the config or topology.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks (Im working remote and cannot "double check" with an actual client).
But I accept this as fact 🙂
-
3rd Party VPN
159 -
ACLs
88 -
Auto VPN
282 -
AWS
35 -
Azure
65 -
Client VPN
365 -
Firewall
826 -
iOS
1 -
Other
536 -
Wireless LAN MR
1