- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Nexus -Vpc with Meraki MX 84
Nexus -Vpc with Meraki MX 84
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Nexus -Vpc with Meraki MX 84
Guys,
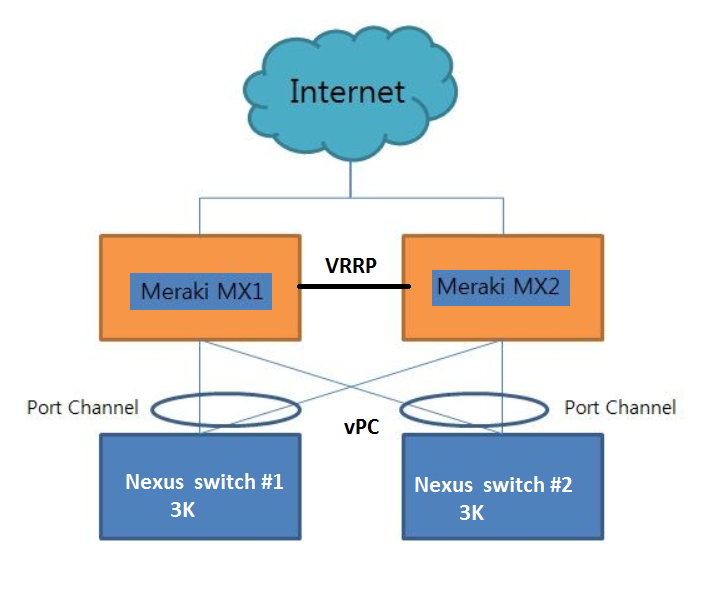
I am doing the following topology between MX84 and Nexus 3K , the Nexus 3K have a Port channel and use Vpc , I know Meraki MX do not support Port channel , so what is the best Practice configuration in MX 84 LAN which is facing the Nexus Port channel and how to do the scenario below. Keep in mind VPC in Nexus is means Active Active .
Note the Port type form MX84 toward the Nexus are trunk ports .
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
With "No Knowledge" on Nexus / vPC. Following are my observations.
As you know MX HA is Active - Standby.
MX1 will be the only device serving the network until fail-over happens.
You rightly said "Teaming" is not supported by MXes. Considering this I dot not see much advantage of "Port Channel" configuration on Nexus.
I understand you may consider leaving the "MX LAN Ports" as Trunk.
You may also consider reading following articles on HA Configuration (if already not) for more information
https://www.willette.works/mx-warm-spare/
https://www.syndicateinfo.com/post/mx-warm-spare-ha-pair
Ajit
AjitsNW@gmail.com
www.ajit.network
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi
Awesome question! 🙂
According to my understanding this is the deal:
vPC is basically a PortChannel so it expects LACP or a manually configured PortChannel from its peer.
I strongly believe your setup is not a supported configuration. It will probably work though, but some of the links will be disabled because of STP and LACP and I think you won't reap the benefits of a clean failover in case an MX or vPC member goes offline.
Also keep in mind the MXes *don't run STP*, take that into account when you design (= don't disable or filter STP).
We have a few clients with such a setup and the best way for us is to just use no vPC / bonding whatsoever between the MXes and the switches. Mainly because the MXes don't support bonding/aggregating their ports. (I don't know why they don't, it's a feature I dearly miss).
So basically just connect the MXes to each of the Nexuses (as in your diagram) just don't use any vPC between those. Let STP figure it out. And use "orphan-port suspend" (https://www.cisco.com/c/dam/en/us/td/docs/switches/datacenter/sw/design/vpc_design/vpc_best_practice... page 125 ) to safeguard against peer-link failure. Basically ports connected to MXes would be "orphan ports" as Cisco calls them.
And I strongly recommend not to use the VRRP link between the MXes. According to our experience this would perhaps result in a bit better switchover behaviour, but it increases complexity of the setup and some MX firmwares (I think all 14.x) have a problem where during startup they actually create loops and flood the network in such a setup (and never converge as a result). We have seen this on occasion before fixing it by removing the VRRP link between the MXes (even if configured correctly with VLAN pruning).
HTH
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can't use a VPC link to the MX's.
You could consider using the Nexus "bridge assurance" feature and use plain layer 2 ports.
Personally - I would simplify things. Nexus switches can be really finicking because of all their design rules. It is real easy to get caught out in different failure scenarios. Your diagram doesn't indicate if you have a seperate L2 forwarding path between the Nexus switches either.
I would single connect each MX84 to a Nexus switch. Then there are no loops and no spanning tree concerns. And it still preserves the "no single point of failure".
If you really want to you can put you could run a cable between the two MX84's (which you have labelled VRRP) but make sure this is using a dedicated VLAN that is not allowed on the trunk link to the Nexus switches. This is important to maintain a loop free solution. This link is used by the MX to exchange state information in this case.
You can check out this design guide by Aaron Willett:
https://www.willette.works/mx-warm-spare/
Aaron refers to the link between the MX84 as the "heartbeat" VLAN. Make a special note it is not trunked to the downstream switches.
Just keep in mind to keep your design loop free at layer 2 if you want an easy life and a reliable solution.
-
3rd Party VPN
170 -
ACLs
101 -
Auto VPN
316 -
AWS
39 -
Azure
71 -
Client VPN
431 -
Firewall
717 -
Other
594