Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Site-to-site outbound firewall
Site-to-site outbound firewall
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Site-to-site outbound firewall
Hi there ,
We have a remote site ( MX65 ) with site-to-site VPN tunnel going to one of our MX cluster.
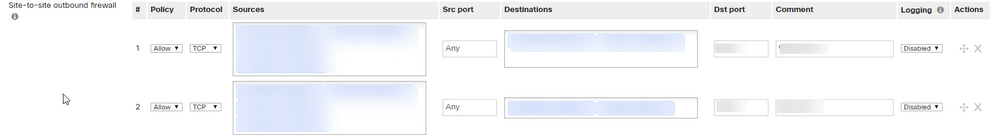
Somehow , someone managed to configure many Site-to-site outbound firewall rules ( those rules are Org wide ! ).
Those rules are only there to permit or deny specific traffic comming from the remote site.
Why would you configure those rules on the site-to-site outbound firewall and not the MX ( remote site ) ? Currently any remote site ( that is participating to the site-to-site VPN ) is bound to those rules ( they are org wide )
Site-to-site
Vs firewall rules
Am I missing something ?
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
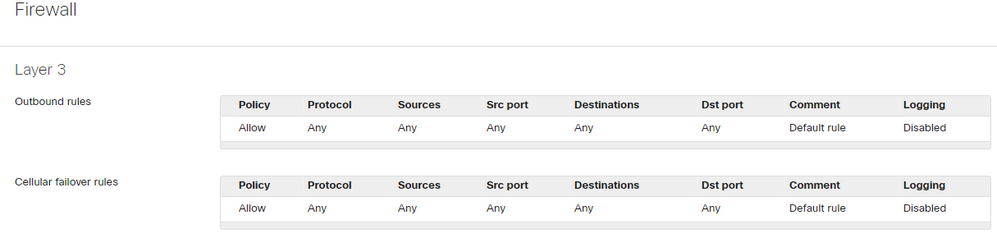
Yes. The regular firewall rules don't apply to VPN traffic.
They would apply to all your sites, but of course only the site that has a relevant subnet will actually be affected.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That firewall is meant to control traffic between site-to-site VPN peers. Let's say for example you have a datacenter, and in that DC there are some servers that you want to be reachable only from some VPN branches. You would then configure the outgoing firewall from the point of view of the branch's subnets and block the access for the subnets you don't want to have access (it's a default allow firewall).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Let's say I want to block the remote site from reaching the servers. I would have to do this with the site-to-site VPN firewall outbound rules ? And these rules would also apply to ALL my other remote site ( 2k ) ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes. The regular firewall rules don't apply to VPN traffic.
They would apply to all your sites, but of course only the site that has a relevant subnet will actually be affected.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for the info.
I'm not really a fan of this , so I'm going to configure these rules on our NGFW behind the MX. I don't like to idea to mess with those site-to-site firewall rules and accidently blocking the traffic for our 2k remote sites.
I will mark this as resolved
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
>I'm not really a fan of this , so I'm going to configure these rules on our NGFW behind the MX. I don't like to idea to mess with those site-to-site firewall rules and accidently blocking the traffic for our 2k remote sites.
I typically use that approach. I often have a "WAN" interface on the DC firewall, and then is where I plug in both MPLS WAN circuits and MPLS AutoVPN terminations.
I use the firewall to provide fine grained control, and the MX VPN firewall rules for course control.
-
3rd Party VPN
172 -
ACLs
91 -
Auto VPN
301 -
AWS
36 -
Azure
70 -
Client VPN
381 -
Firewall
856 -
iOS
1 -
Other
552 -
Wireless LAN MR
1