- Technical Forums
- :
- Security & SD-WAN
- :
- Meraki external route not working.
Meraki external route not working.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Meraki external route not working.
I have a FortiGate firewall in front of my Meraki MX appliance. FortiGate has site to site IPSEC tunnel with one of our DC and Meraki is the Hub for auto VPN setup for my other sites. i am getting some routes through Firewall IPSEC and those subnets are reachable through Meraki Hub. but when i advertise those learned routes into auto VPN my spokes cant reach those subnets though. when i try to trace these subnets instead of taking me to the auto VPN route shows it is taking the default route. is there any advise?
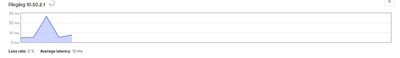
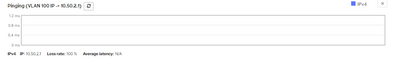
reachability though MX Auto VPN Hub.
Route being recieved on spoke via auto VPN.
no reachability from spoke LAN switch.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is the Fortigate IPSec tunnel is terminated on the same MX that is working as Hub in AutoVPN? If so, Meraki unfortunately does not support routing between Third-Party VPN and AutoVPN.
It you need to route between Spokes sites on Meraki AutoVPN and the Non-Meraki VPN, you'll need an extra MX.
Like what you see? - Give a Kudo ## Did it answer your question? - Mark it as a Solution 🙂
All code examples are provided as is. Responsibility for Code execution lies solely your own.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@rhbirkelund remote tunnels are terminated on the fortiGate. MX only has auto VPN tunnels and routes to reach remote subnets pointed towards fortiGate.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is the spoke lan switch/ip from a vlan (management vlan?) that is selected to be in the autovpn?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can you draw a picture with some example networks?
And have you the NAT-Exemption enabled for the MX?
At least when the Fortigate is in front of the MX, all traffic flowing to the Fortinet would be NATed by default which can cause problems and make this really complex.
I would put the MX in concentrator mode or place them side by side instead of behind the other.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@KarstenI here it is. this network was handed over to me as it is 😞 . i am able to reach both 10.50.x.x and 10.60.x.x from LAN subnets of the hub. i am advertising these routes in auto VPN as well but spokes cannot reach DC subnets though.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Are that subnets green in the routing table on the spoke?
From the hub you can ping the switch ip of the spoke ?
There are no sitetosite vpn firewall blocking traffic?
-
3rd Party VPN
169 -
ACLs
102 -
Auto VPN
323 -
AWS
39 -
Azure
73 -
Client VPN
449 -
Firewall
651 -
Other
603