- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Issues with non-Meraki VPN and Z1 to Azure
Issues with non-Meraki VPN and Z1 to Azure
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Issues with non-Meraki VPN and Z1 to Azure
Have a customer setup with a mix of MX/Z1.
All tunnels have status green and since we have Z1 we use IKEver1.
We can reach clients from Azure on the local sites running MX but not on the sites running Z1.
Have anyone had the same issues or am I missing out on something.
- Labels:
-
3rd Party VPN
-
Azure
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Check if it helps
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Are the working and non-working sites running the same firmware?
Do the working and non-working sites all have static IP addresses?
Do the working and non-working sites have the public IP directly on the MX/Z or are they sitting behind something else doing NAT?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The working sites run MX64 and firmware 15.43
The non-working sites run Z1 and firmware 14.56
All the Public IP are directly on MX/Z1
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Are you able to upgrade the Z1s to 15.x so they are the same as the working sites?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The Z1s don´t support 15.x
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I suspect the cheapest fix will be to get the VMX-S. If the number of Z1s is not large you could also consider upgrading them to Z3s.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Another option that would work would be to deploy StrongSwan on Ubuntu, and terminate the Z1 VPNs on that instead. We have used StrongSwan a lot and it's great.
https://www.ifm.net.nz/cookbooks/meraki-vpn-to-azure.html
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
> We have used StrongSwan a lot and it's great
As of MX 15, so are we, and I can confirm it's far easier to work with than what we dealt with in the past 😁
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
ps. If you get the VMX-S all your problems will go away ...
https://meraki.cisco.com/product/security-sd-wan/virtual-appliances/vmx-small/
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
So, both my MX64 and Z1 is using the same vpn-tunnel to Azure.
MX64 is on 15.x and the Z1 on 14.x
On my Z1s I get the following error in the event log:
msg: exchange Identity Protection not allowed in any applicable rmconf.
Will I get this working or do I have to look at another solution ?
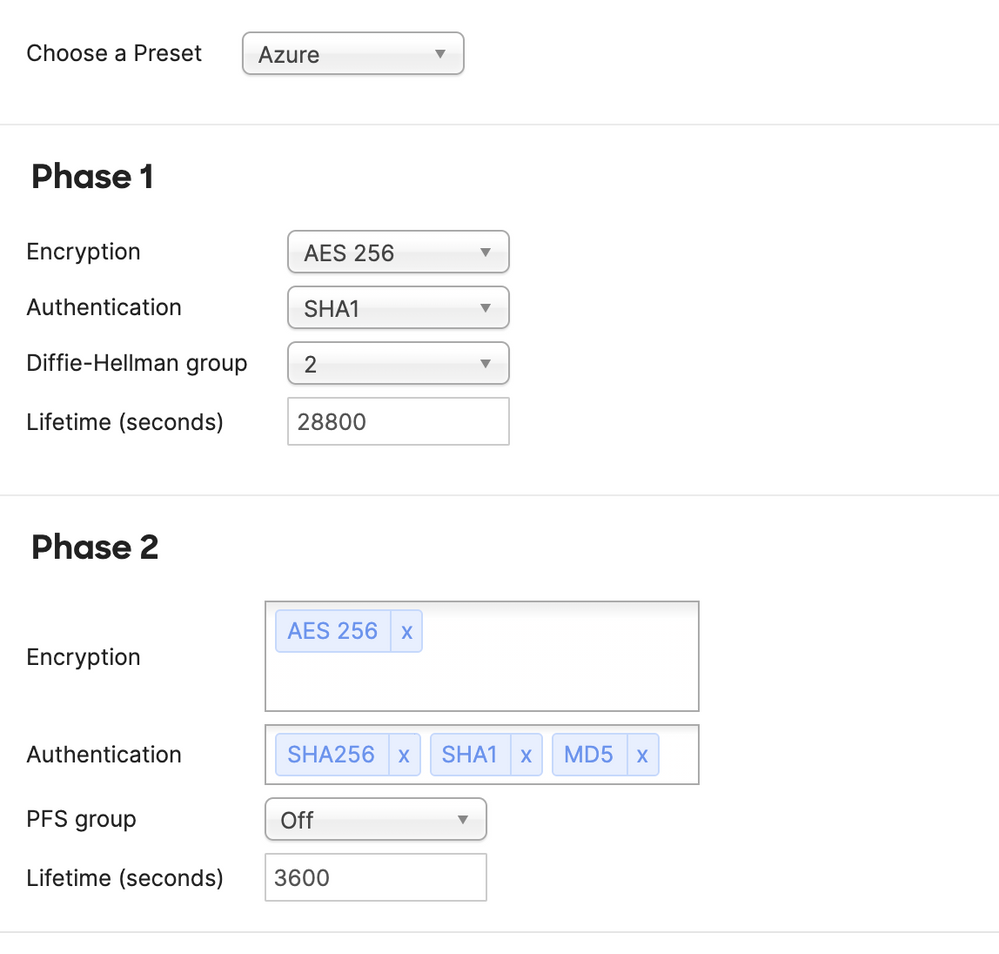
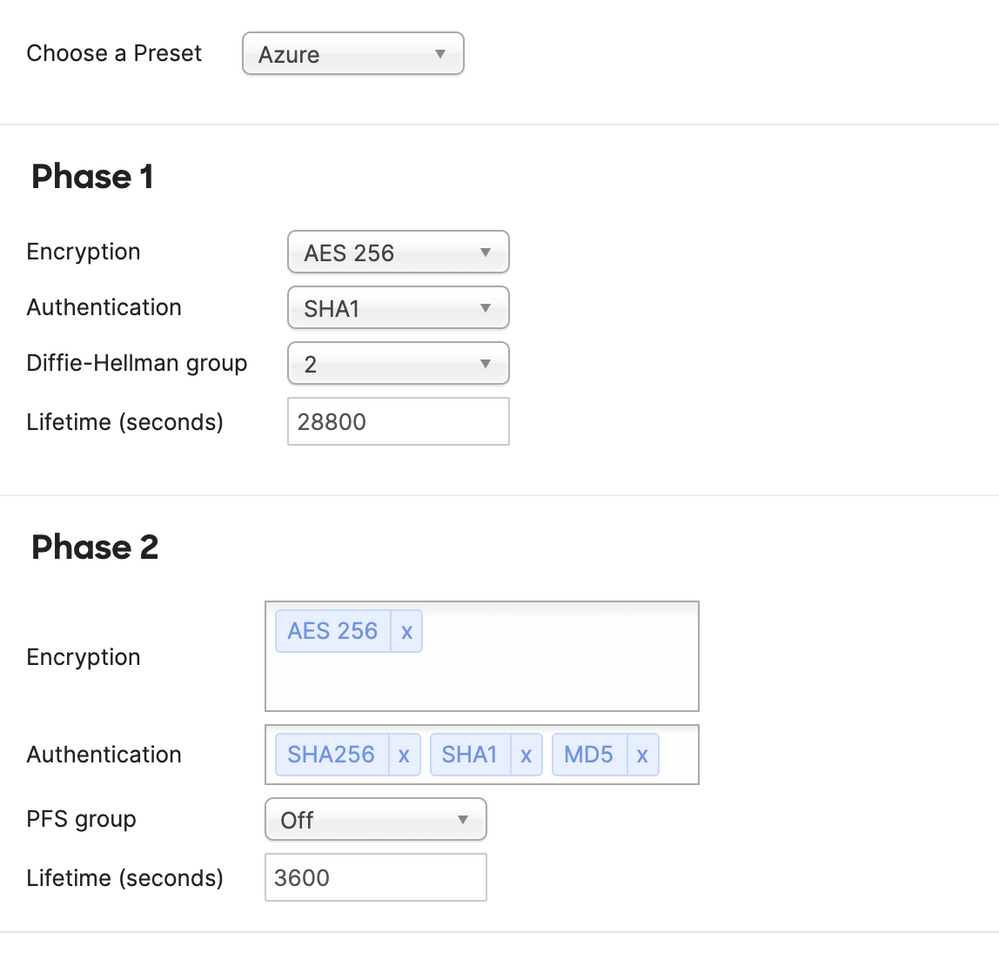
See picture for my settings on the Tunnel
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
"Identity protection" refers to IKEv1 Main Mode; I'm not sure if Azure still allows for IKEv1, but it sounds like it might be expecting IKEv2
-
3rd Party VPN
170 -
ACLs
101 -
Auto VPN
316 -
AWS
39 -
Azure
71 -
Client VPN
431 -
Firewall
720 -
Other
595