- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Is it possible to install a Meraki MX security appliance in an AWS envi...
Is it possible to install a Meraki MX security appliance in an AWS environment
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is it possible to install a Meraki MX security appliance in an AWS environment
Is it possible to install a Meraki MX security appliance in an AWS environment behind our VMX-M device for additional security instead of using the AWS costly security. It would be nice to spin up a virtual instance with Meraki MX security appliance settings.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Just curious if there is a virtual version other than the vMX-M we currently have. As you know the vMX-M does not have any content filtering features on that device.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I don't know - but NAT mode is available for VMX.
If you were keen to do an experiment, you could request another VMX on trial, and do a test deployment, and see what happens.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The "V" in "VMX" means virtual - it is an MX. You typically use the VMX as a VPN concentrator.
Amazon doesn't charge for security groups, used for firewalling, so I am not sure where the cost aspect comes from?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I will need to look further into with our AWS personnel. To confirm with you Philip if you are familiar with the AWS environment, so it is possible to perform content filtering using AWS security groups at no extra cost?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
From what I understand AWS doesn't allow customers equipment in their data centres. VMX is your only option if you want a Meraki security appliance within your AWS VPC
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Blake - We are just looking to content filtering aspect for all our AWS servers.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If you can use a Fortigate to filter, why couldn't you use a vMX?
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
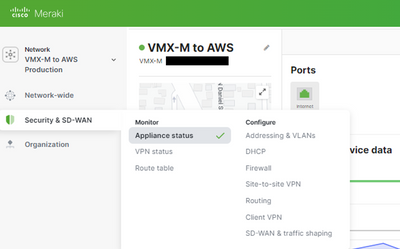
the vMX-M Meraki virtual device does not have any Content Filtering options in the dashboard. Attached a screen shot.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Do you have the Advanced Security license?
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Correct me if I'm wrong, but in the past vMX runs as a VPN concentrator only. It does not provide firewall, content filtering, IPS or other security functions.
Isn't it?
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The vMX-M gives you firewall settings for Layer 3 and Layer 7. The vMX-M does not provide any Threat protection or Content filtering. We are looking to see if there is any Meraki products that will provide that service for our AWS environment.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Wouldn't it be better to talk to your Meraki sales representative?
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This was historically the case. About 6 months ago the VMX gained support for NAT mode, and Meraki changed it so this is now the default deployment option (bad!!!).
https://documentation.meraki.com/MX/Other_Topics/vMX_NAT_Mode_Use_Cases_and_FAQ .
This was done primarily to offer full tunnel client VPN support for VMX. In NAT mode, a user can VPN in and access the Internet (the VMX will NAT their traffic).
HOWEVER, all AutoVPN spoke traffic is also NATed when accessing cloud servers. The bonus of this is you no longer need to configure any routing in the public cloud - as all traffic (client VPN and AutoVPN) is NATed to the VMX private IP address and appears to come from that IP.
This is a major pain. Servers CAN NOT access spokes - because the spokes sit behind NAT. For example, you can't have a server in the cloud send a print job to a printer on-premise over AutoVPN using a VMX in NAT mode (actually I lie - you can make it work, but you have to configure NAT port forwards, just like if you have a physical MX attached to the Internet and wanted to give access to something from the Internet to an internal server - but this is a nasty solution for this use case).
As a consequence of this, I never use NAT mode for VMX. Also note you can't change this setting post-deployment. If you want to change it you have to delete the VMX and re-deploy it.
Looping full circle, now you can have a VMX in NAT mode like a "typical" on-premise VMX.
Does the VMX support IPS or contenting filtering while running in NAT mode (like its on-premise counterpart)? I don't know. I have never used NAT mode on VMX, so have never tested this out. But I think there is a reasonable chance this will work.