- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Deny Local LAN Question
Deny Local LAN Question
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Deny Local LAN Question
Greetings,
I've set up the firewall and traffic shaping for two different SSIDs on my network to "deny any local LAN' . One is in NAT mode, the other is in bridge mode.
I don't have any group policies set up. I don't have any whitelisting or blocking set up.
I've noticed that if someone connects with a laptop that is a member of the domain it seems to override this rule and they have full access to the LAN connecting to either of the SSIDs. Is that how it's supposed to work?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Have they disconnected and reconnected to the network since you setup the deny rule?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, I've connected and disconnected multiple times to both SSIDs.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That's strange behavior. I can't think of any mechanism that would do this. Other than the standard group policies, whitelists and blacklists.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It looks like it may be working correctly now. I need to do a little more testing. Last night I made the changes and saw the behavior, but this afternoon I don't.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
They should only be able to access DNS and DHCP and nothing else on the local LAN.
"Note: DNS and DHCP traffic is exempt from this rule. If the SSID is in NAT mode, only DNS traffic is exempt since the AP acts as a DHCP server for connecting clients."
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This is how I expected it to work, and it did for one device, but not for another.
So, now it seems to be even more strange. It's a Microsoft Surface Pro device. It is connecting to Wi-Fi. It doesn't matter which SSID it connects to, it has full access to the LAN.
When I search for this device in the dashboard I can't see it being connected to any APs.
When I search by name, I find the device and it shows that it's status is an "offline wired client" and it's associated with one of my Meraki switches.
How is this even possible?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
>but not for another
If you whitelist the device or apply a group policy which overrides the firewall rules they you could get this happening.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I don't have any whitelists, blocking or group policies in effect.
Even then I would think it would still show the device connected to an AP/SSID and not show it being an offline wired device connected straight to a switch.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
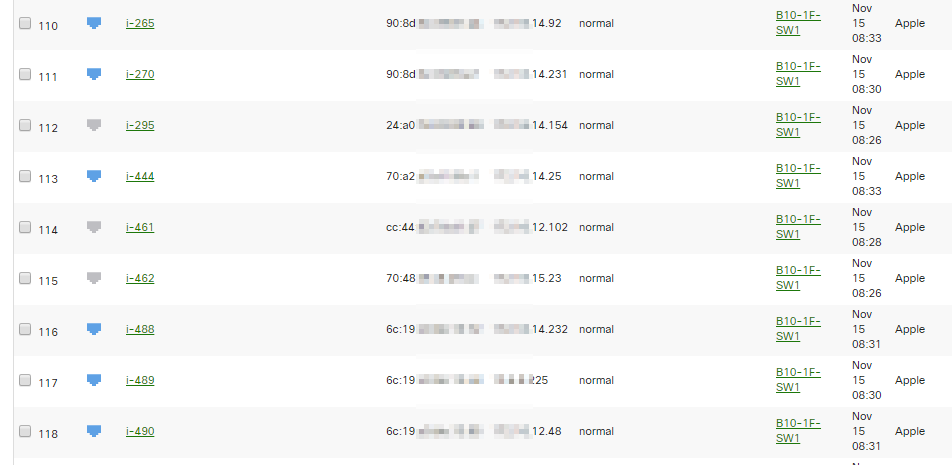
Yeah, we noticed same problem (wireless clients are recognized as wired clients, like Ipads, Macbook...) on our network... then network policy to wireless clients do not work.
Supports don't know either.....
Here are some iPads
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
No, it's all Meraki switches and Meraki APs.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What's actually connected on the port the client is reported to have been connected to last?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It's the port connecting to Access Point
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
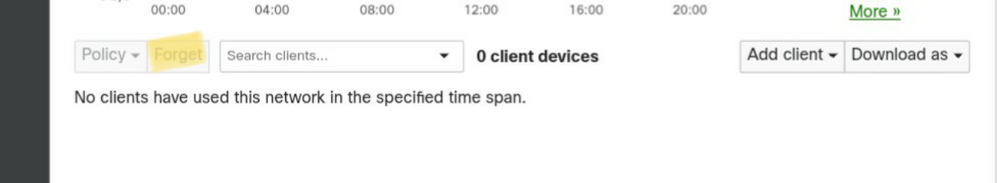
Do you have the"forget client" button in your dashboard? If you do I'd try using that to see if it's some kind of weird caching behavior.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I don't seem to have that button in my dashboard. Just the Policy drop down box.
-
3rd Party VPN
170 -
ACLs
101 -
Auto VPN
314 -
AWS
39 -
Azure
71 -
Client VPN
431 -
Firewall
715 -
Other
594