We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Creating a route to Non Meraki VPN
Creating a route to Non Meraki VPN
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Creating a route to Non Meraki VPN
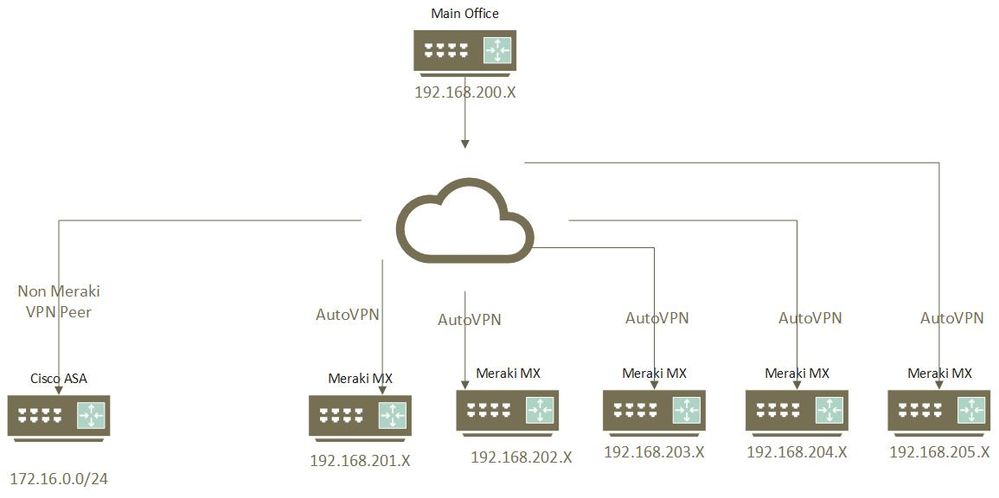
I have 6 Meraki's with AutoVpn working great, recently added a site to site vpn to a cisco asa. I do not know how to get my traffic to flow to that new vpn. The new vpn will only use rdp. Can someone please help me setup a route to be able to rdp to a server on the new vpn?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @bdw72,
I understand we need to introduce an additional router (Preferably MX) in our network at the HUB Location to inject Non-Meraki routes into AutoVPN.
Aaron created the following document explaining this in an awesome manner.
https://www.willette.works/merging-meraki-vpns/
Ajit
AjitsNW@gmail.com
www.ajit.network
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Forgive me here, because I am not a network guru. Is there a way to do this without incurring the cost of buying another MX? By adding a/some static routes?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Assuming Site Alpha and Site Beta. You have AutoVPN between Alpha and Beta. Alpha also has static routes to Vendor Gamma.
If you want Site Beta to access Vendor Gamma by traffic path Beta -> Alpha -> Gamma, you need an additional device due to how AutoVPN works.
Otherwise, I'd spin up a tunnel between Beta and Gamma.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Possibly share your existing network info (subnets, map, VPN settings, etc.)
Might need to add the asa subnet to the Meraki non-Peer VPN settings.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I just need a route from my main office to the Cisco ASA, the other offices do not need to be able to get to the ASA. Can someone help me create that route?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You might want to look this over
https://documentation.meraki.com/MX/Site-to-site_VPN/MX_to_Cisco_ASA_Site-to-site_VPN_Setup
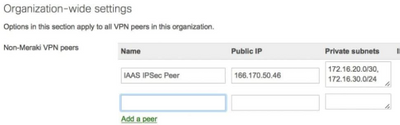
Have you added the 172.16.0.0/24 to the private subnet on the MX VPN settings?
Can ping from MX to ASA and vice versa?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Have you added the 172.16.0.0/24 to the private subnet on the MX VPN settings? I do not know where to do that at. I am not a network person, I was able to get them connected, but need that route.
I can ping their internet IP but nothing internal. like rdp to 172.16.0.12
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This is on the site-to-site VPN settings side of the MX. Where it says private Private subnets you will need 172.22.0.0/24 listed in there.
If it fair to say the ASA ip is 172.22.0.1, can you ping that IP from the MX tools menu?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That part is setup, yes. I do not know what the internal ASA IP is, but i tried pinging the 0.1 address and no luck.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If you check the VPN Status page and then Choose your MX/Network. Then choose non-Meraki peer button you should see the VPN status button is green. Also you will see what subnets are used. You could try running an IP scan on the subnets to see if you can find the ASA.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Turns out the vendor vpn was not working properly, they moved it to a different firewall and I can ping their internal address. Thank you for all your replies, I am slowly learning how this works, much appreciated.
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
306 -
AWS
36 -
Azure
70 -
Client VPN
383 -
Firewall
868 -
iOS
1 -
Other
557 -
Wireless LAN MR
1