- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Auto-VPN Hubs - Split Tunnel (Pri Hub) and Full Tunnel (Sec Hub)
Auto-VPN Hubs - Split Tunnel (Pri Hub) and Full Tunnel (Sec Hub)
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Auto-VPN Hubs - Split Tunnel (Pri Hub) and Full Tunnel (Sec Hub)
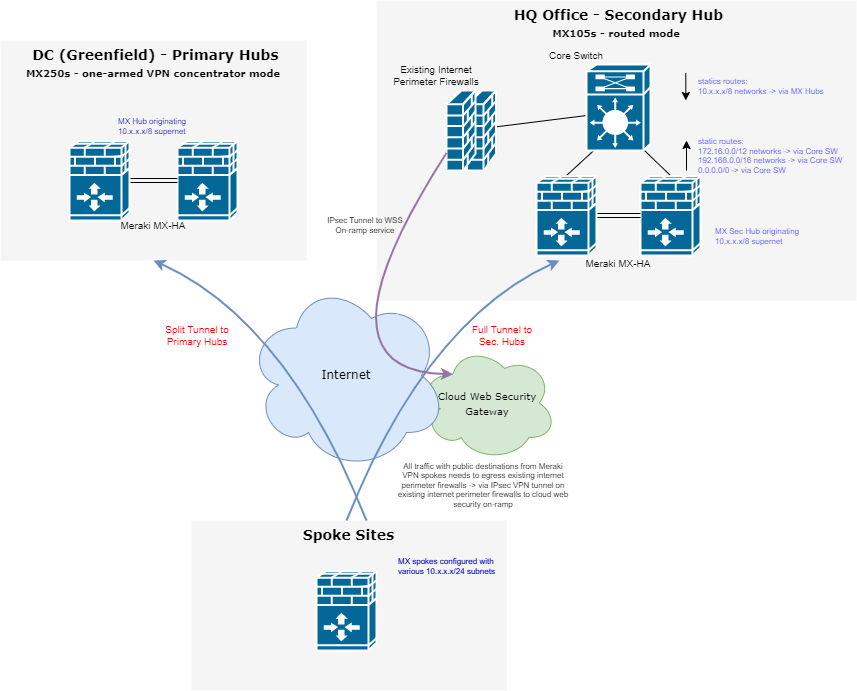
Hello all, I have a hub-to-spoke design that I need to implement for a client where which is somewhat straightforward, however I've never done this design before so would appreciate if anyone could validate.
The client has a requirement to tunnel all publicly destined traffic through their existing internet perimeter firewalls which has IPsec VPN tunnels to a cloud on-ramp web security service.
Therefore my logic is to configure hub as the following priority & settings:
Primary MX hub will be implemented in Split Tunnel mode (greenfield DC CoLo environment)
Secondary MX Hub will be implemented in Full Tunnel mode with "Default Route" option selected (existing HQ Office, also regarded as customers existing DC environment). Secondary MX hub will also need to be in routed mode.
Would this configuration work, so spokes for e.g would transit 10.x.x.x/8 networks via primary hub? And any network traffic destined to public addresses would transit via secondary hub, since the default route option is selected and static routes downstream to core switches/firewall are explicitly configured on secondary hub?
I've based this logic as per documented (from Site-to-Site VPN doco) behavior when Default Route option is selected
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have never seen a design like this, but just to remember that:
- Split tunnel (no default route): Send only site-to-site traffic, meaning that if a subnet is at a remote site, the traffic destined for that subnet is sent over the VPN. However, if traffic is destined for a network that is not in the VPN mesh (for example, traffic going to a public web service such as www.google.com), the traffic is not sent over the VPN. Instead, this traffic is routed using another available route, most commonly being sent directly to the Internet from the local MX-Z device. Split tunneling allows for the configuration of multiple hubs.
- Full tunnel (default route): The configured Exit hub(s) advertise a default route over Auto VPN to the spoke MX-Z device. Traffic destined for subnets that are not reachable through other routes will be sent over VPN to the Exit hub(s). Exit hubs' default routes will be prioritized in descending order.
Concentrator priority
The concentrator priority determines how appliances in Hub (Mesh) mode will reach subnets that are advertised from more than one Meraki VPN peer. Similarly to hub priorities, the uppermost concentrator in the list that meets the following criteria will be used for such a subnet.
A) Advertises the subnet
B) Currently reachable via VPN
It is important to note that concentrator priorities are used only by appliances in Mesh mode. An appliance in Hub-and-Spoke mode will ignore the concentrator priorities and will use its hub priorities instead.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Ok understood, I got mixed up with terminology.
To clarify with proposed hub priority - Site-to-Site VPN settings for spokes on dashboard will look like this
1. DC-Hub (no default route selected)
2. HQ-Hub (default route selected)
I understand difference between split tunnel and full tunnel, however given what's written in doco regarding behavior when default route is selected and also explicit 0.0.0.0/0 route is configured on HQ-Hub.
My interpretation is that public traffic from spokes will route through via HQ-Hub despite DC-Hub being higher in priority.
--------------------------------------------------------------------------------------------------------------------------------------------
Default Route
When configuring Hubs for a Spoke, there is an option to select a hub as being a Default route. If this option is selected, then that hub will be configured as a default route for the Spoke (0.0.0.0/0). Any traffic that is not sent to a configured VPN peer network, static route or local network will be sent to the default route. Multiple hubs can be selected as default routes. Hubs marked as default routes take priority in descending order (first priority at the top).
https://documentation.meraki.com/MX/Site-to-site_VPN/Site-to-Site_VPN_Settings
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes that would work.
From dc2 you also need to set the static routes (or at least the 0.0.0.0 one) to be part of the vpn. This will automatically also advertise these routes to your spokes
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Great, yeah I was planning on making sure the default route is advertised into SD-WAN VPN at HQ office location.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Take a look at some topologies examples:
Please, if this post was useful, leave your kudos and mark it as solved.
-
3rd Party VPN
166 -
ACLs
100 -
Auto VPN
313 -
AWS
38 -
Azure
70 -
Client VPN
427 -
Firewall
701 -
Other
588
