- Technical Forums
- :
- Dashboard & Administration
- :
- Restricting a subnet of IPs from accessing Port Forwarding
Restricting a subnet of IPs from accessing Port Forwarding
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Restricting a subnet of IPs from accessing Port Forwarding
We had a problem with one of our clients that has a Meraki Firewall. They have two workstations that use port forward to allow the employee to work remotely from home during Covid lockdowns. Neither of the port forwarding setups use the standard ports for RDP. Today a group of Russian hackers got in and installed ransomware on one machine and encrypted all their data files including the NAS Server Drive. We were able to restore backups from the nightly offsite backup that we do on the workstation, but when the NAS drive was put in, the installer didn't bother to let us know that the mapped drive was not on an actual server anymore - the problem was they used almost the same name for the NAS Drive as the old server name.
I know that you can specify which IPs can get in but in this case, the users have Dynamic IPs that change often.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Stampeder I would strongly advise against using RDP extenrally, you are better off using a VPN or software like teamviewer. Microsoft themselves recommend against using RDP externally as well.
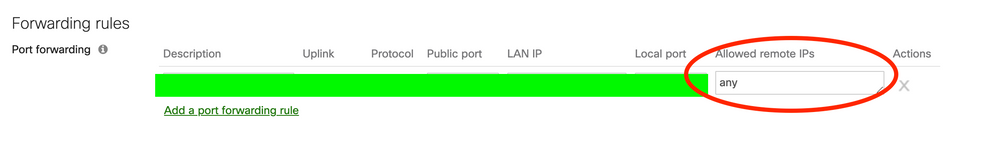
You can restrict incoming traffic using by providing "Allowed remote IP's"
-
Administrators
152 -
Android
1 -
Change log
11 -
Firmware Upgrades
22 -
Inventory
37 -
Licensing
53 -
Other
104 -
Security & SD-WAN (MX)
1