Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Wireless
- :
- Re: Guest Wi-Fi with AD authentication
Guest Wi-Fi with AD authentication
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Guest Wi-Fi with AD authentication
Hi,
We are looking to overhaul our wireless and encorporate what is currently three SSID's in to one seamless network that is to be used by guests and staff.
However, we want to still keep guests seperate from the staff and have different policies assigned to them. We are hoping to use the AD authentication on this network so that staff can login and use the wireless with their own credentials rather than a set OTP.
Is it possible to have a 'Continue as Guest' on the login page, or would a guest account need creating on AD? If the latter is true, then I think having a seperate guest SSID would be easiest. The only issue being that staff may just use the guest network to save them having to type in any details.
I look forward to hearing any input.
Many thanks
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
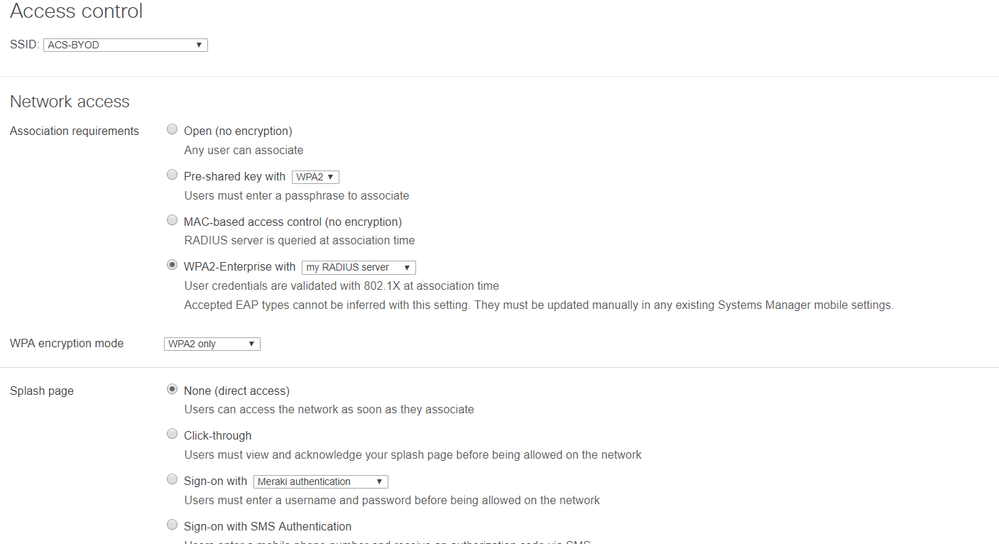
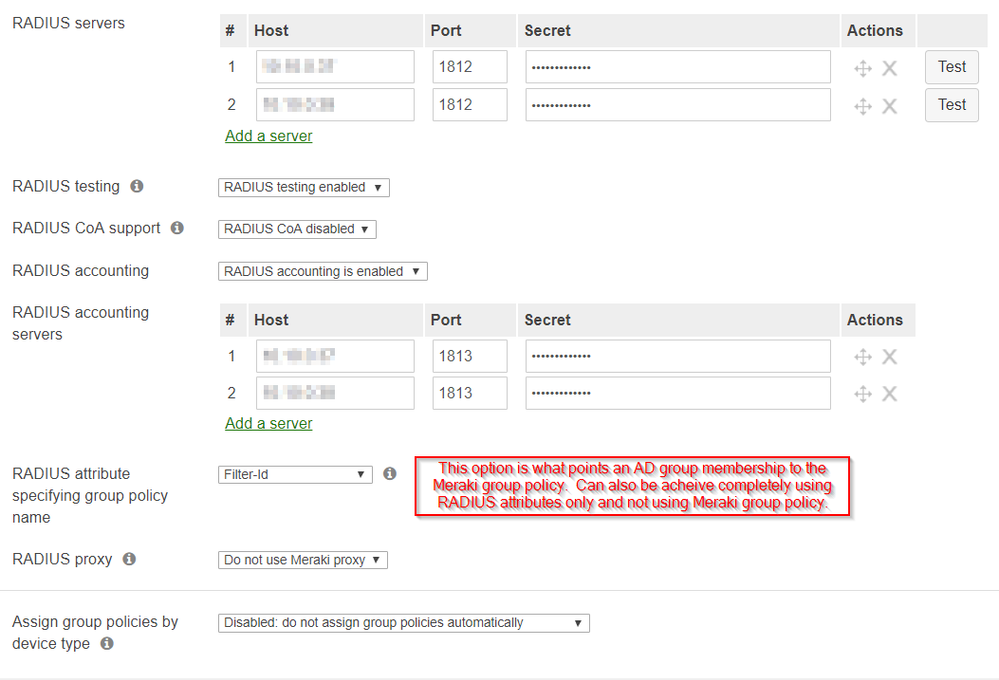
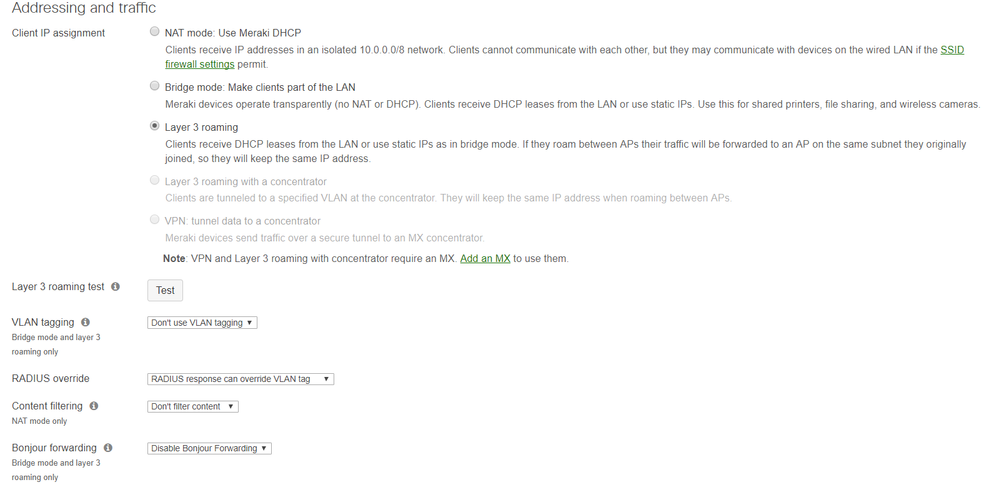
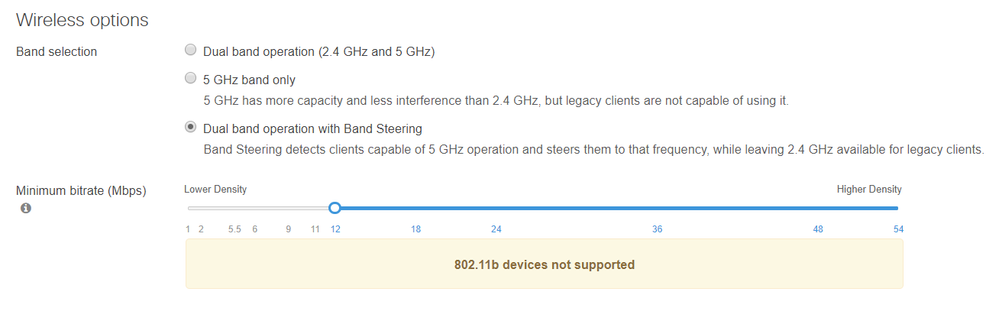
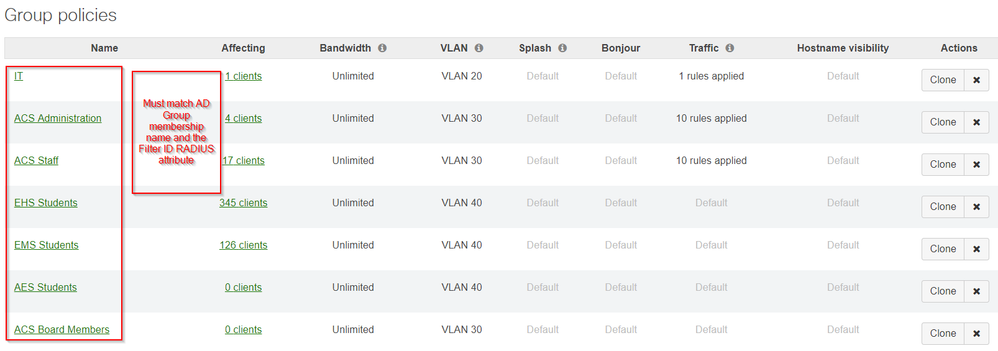
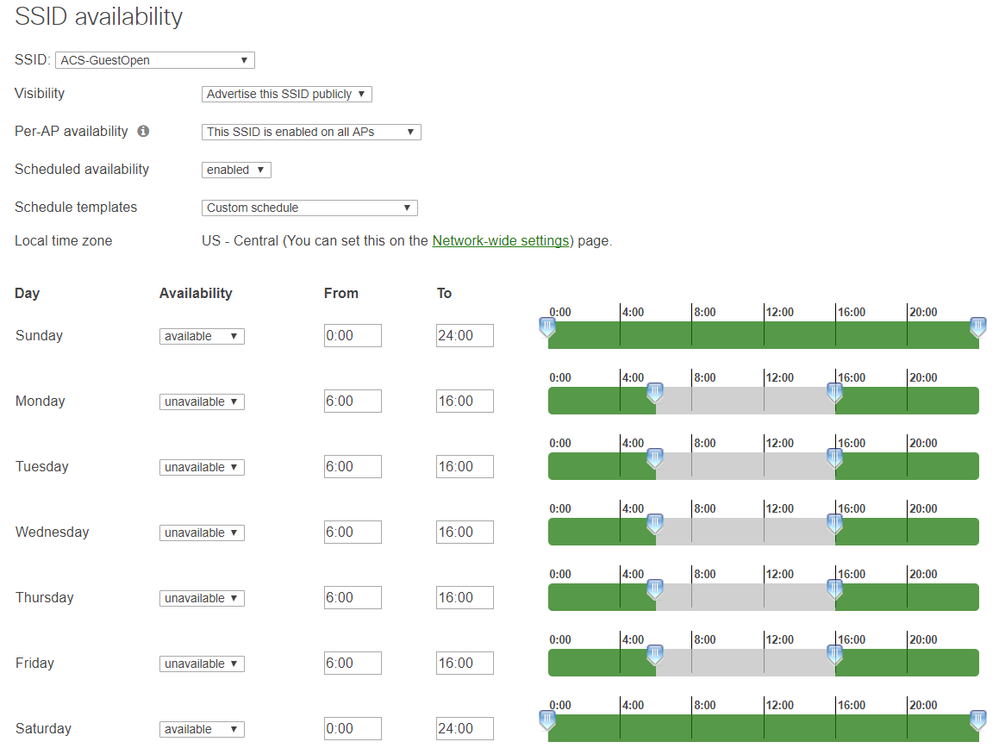
I've included pics of the settings below followed by great Meraki and Microsoft documentation on this process.
I actually have two NPS servers (just for failover purposes and no single point of failure) hearing the requests and load balancing and then three actual RADIUS server roles on three other servers processing the requests for loading balancing at (34%, 33%, 33%).
Documentation in no particular order:
https://technet.microsoft.com/en-us/library/cc730866(v=ws.10).aspx
https://technet.microsoft.com/en-us/library/Cc772591(v=WS.10).aspx
https://technet.microsoft.com/en-us/library/cc731824(WS.10).aspx
https://technet.microsoft.com/en-us/library/Dd197433(v=WS.10).aspx
https://technet.microsoft.com/en-us/library/cc725658(v=ws.10).aspx
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
i would make a seperate guest ssid, deny access to local lan, rate limit the connection and add content filters.
no employee would connect that guest network.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This is very easy to do. Setup a default VLAN for data and another VLAN for your guest wireless SSID. Then create your 2 separate SSIDs and under the guest one, tell it to use VLAN tagging. IN the drop down, select the VLAN you want. I use 4, but you can number it whatever you feel like. Also, add a firewall run denying the guest subnet any access from any port to the main SSID network. You can add an exemption if you want if there's a printer for example, but I generally don't. With the Merakis, it's really easy 🙂
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
HI @Jake
I wouldn't do that. Setup one SSID for staff and use WPA2-Enterprise mode. Every user and machine is authenticated using their AD credentials. There are no splash pages - staff get in without having to think.
Then for guest create a splash page.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Philip,
Unfortunately, setting up a RADIUS server that communicates with AD is not an option, so we would have to use the LDAP method through a splash page.
Many thanks,
Jake
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for your help
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I've looked into this but am I right in saying this would make Meraki group policy assignment by user groups on AD impossible?
This was an important feature for us that I know is available to use with the splash page. Is is possible to implement this with WPA2-Enterprise?
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Unfortunately, setting up a RADIUS server that communicates with AD is not an option, so we would have to use the LDAP method through a splash page.
Many thanks,
Jake
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
we use Cisco ISE as an radius server. The ISE is connected to the Microsoft AD and the Meraki WLAN is connected to the ISE.
Once a user wants to connect to the internal SSID the ISE checks if the device is allowed to go to the internal LAN (it´s checked if windows devices have an certificate and if the useres connecting with their AD account to the SSID). If the device is not allowed to the internal LAN it will placed to the "external" (V-)LAN for internet connect.
Guests will connect to an Guest-SSID with frequent changing preshared keys routet dirctly to an external VLAN for internet access.
regards
redsector
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Maybe you'll get some ideas from this...
At any given time, I have at most 3 SSID's being offered. I'll define them below:
- ACS-Wifi: Production wireless network for district-owned devices using PSK. I push this config to all devices using one management tool or another depending on the device. VLAN 4 with full network access.
- ACS-BYOD: BYOD networks for staff and student personal devices using a combination of RADIUS and Meraki group policies to further segment based on AD group membership. IT, Staff, Students, Admins all get a different VLAN up authentication. This keeps me from having to have multiple SSID's achieving the same result. Depending on the AD group membership, the Meraki group polices are allowing or disallowing certain network access...file servers, etc. Filtered using framed IP address and ias logs on the RADIUS servers to tie username and IP address together thus providing the same internet filter policy as if logged in to a Windows machine. VLAN's 20, 30, 40, 50.
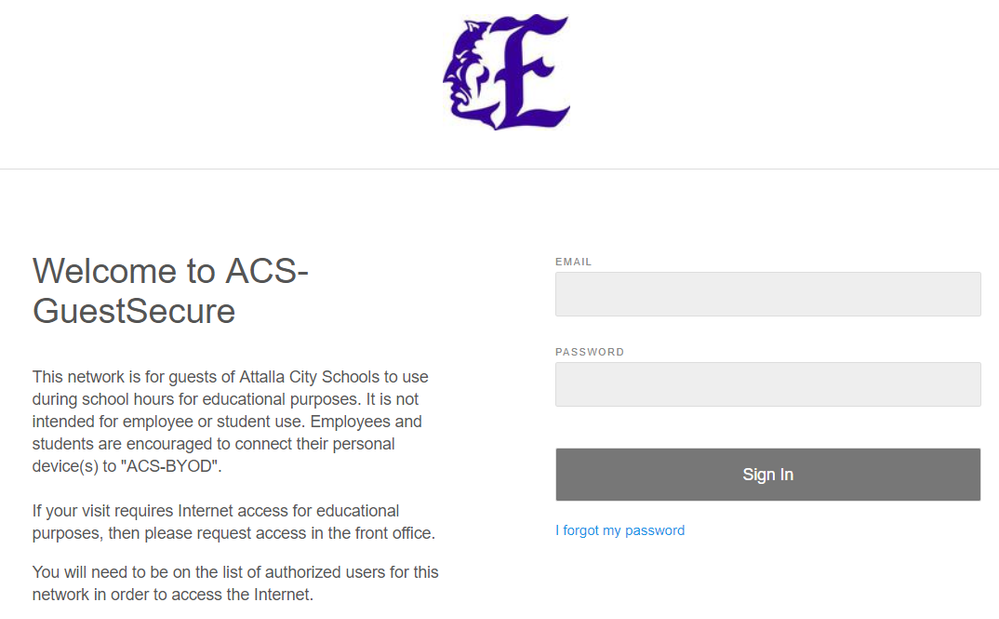
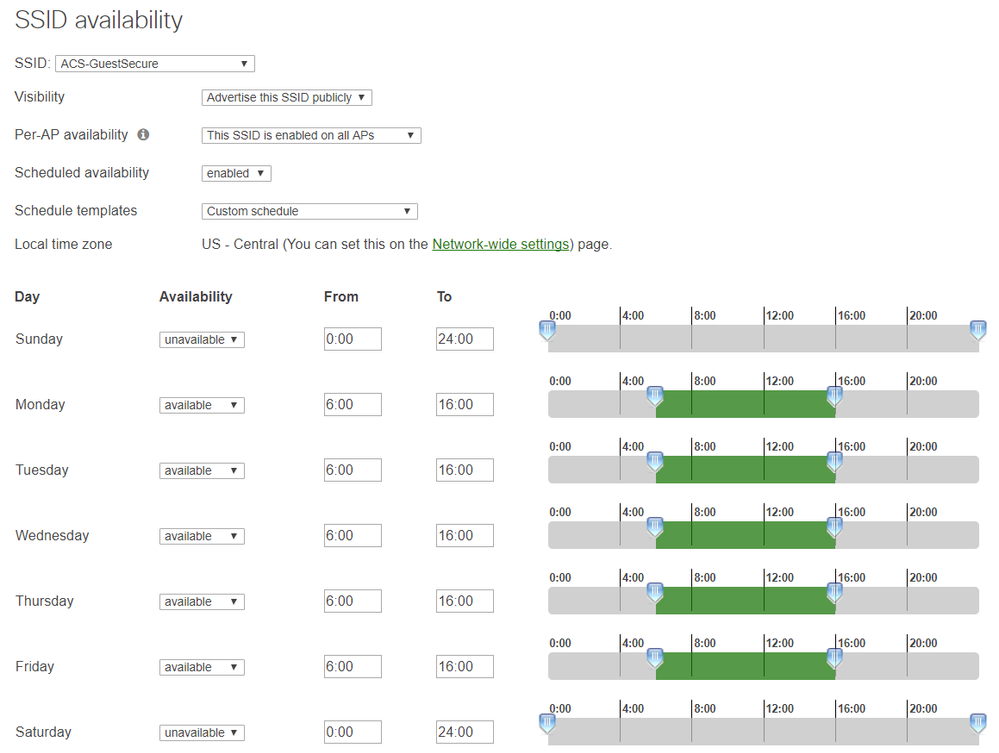
- ACS-GuestSecure (M-F 6am-4pm using Meraki SSID Availability): For non-employee/student visitors here for education reasons (deemed so by principal) that need wifi using Meraki splash page and authentication. I have a guest ambassador at each site and using OneLogin SAML SSO and Chrome extension, the guest ambassador has one click SSO into their portion of the Merak dashboard to create true guest accounts as needed per the discretion of the principal. VLAN 250 and this entire network is filtered using my internal content filter set extremely loose so that education-related visitors should have no issue during their visit.
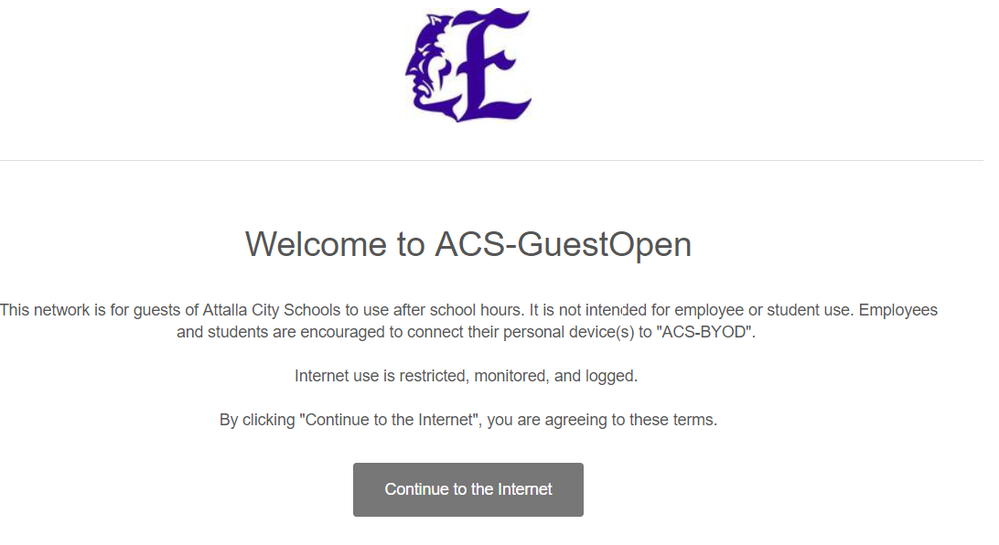
- ACS-GuestOpen (M-F 4pm-6am and all day Saturday and Sunday): For after hours guest wifi for anyone at any of our sites. Meraki click-through splash page after agreeing to our terms of use. VLAN 200 and filtered in the same method above, but with a student level filter policy since it is anonymous.
Below is each splash page followed by their scheduled availability:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you for your detailed assistance.
With your 'ACS-BYOD' SSID, what association requiremens and splash page do you have set?
The AD group membership is something that we want to use to assigne executives a different policy to the other staff. Can this be used with WPA2-Enterprise, or are you using this with an Open network and splash page.
Many thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I've included pics of the settings below followed by great Meraki and Microsoft documentation on this process.
I actually have two NPS servers (just for failover purposes and no single point of failure) hearing the requests and load balancing and then three actual RADIUS server roles on three other servers processing the requests for loading balancing at (34%, 33%, 33%).
Documentation in no particular order:
https://technet.microsoft.com/en-us/library/cc730866(v=ws.10).aspx
https://technet.microsoft.com/en-us/library/Cc772591(v=WS.10).aspx
https://technet.microsoft.com/en-us/library/cc731824(WS.10).aspx
https://technet.microsoft.com/en-us/library/Dd197433(v=WS.10).aspx
https://technet.microsoft.com/en-us/library/cc725658(v=ws.10).aspx
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content