Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Wireless
- :
- Reference architecture for Guest SSID tunneling
Reference architecture for Guest SSID tunneling
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Reference architecture for Guest SSID tunneling
- Labels:
-
Installation
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
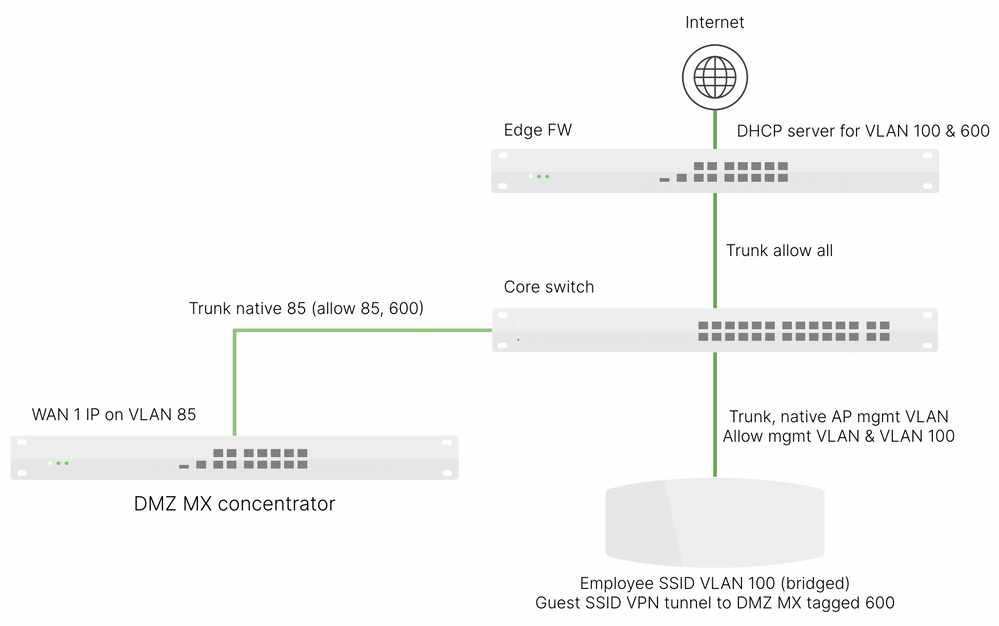
It would essentially be this. I have this set up in my lab.
I'll attempt to answer all the questions from above.
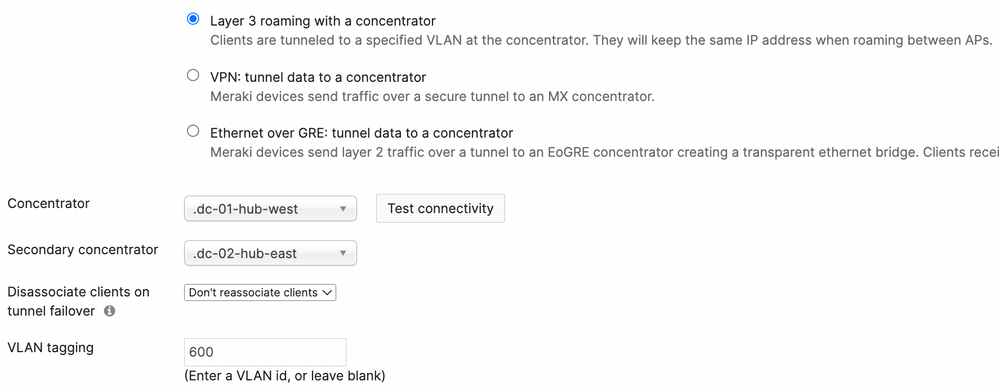
The VPN MX will only have one IP on the WAN 1 interface. This is the mgmt IP and how it talks to dashboard (of course via upstream NAT). A guest SSID can tunnel via L2 from the AP to the MX and egress onto a L2 VLAN present on the switchport connected to the MX. In my example, that's VLAN 600. That VLAN only exists on the link between the VPN MX and the core switch, and the core switch up to the edge firewall which has the L3 interface and DHCP scope for VLAN 600.
In concentrator mode you don't use the MX LAN ports at all.
As long as there's a route between the AP and MX the tunnel should form over the LAN path.
For your branch question. With a tunneled SSID the addressing works the same way it would with a WLC. The client VLAN only exists at the VPN MX and doesn't need to exist as the edge/branch.
In my example below I have firewall rules in two places. On the guest SSID I use L3 firewall rule deny to Local LAN. The Local LAN object means 10.0.0.0/8, 172.16.0.0/12, and 192.168.0.0/16.
Also, at my edge MX I have another rule denying VLAN 600 to the RFC1918 nets. Redundant but it's a failsafe should the MR rule be changed or I want a wired guest.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank-you Ryan. Some follow-up questions. As I understand it, we will connect to a LAN port at least once to perform the initial configuration for the WAN IP/mask/gateway/DNS. I believe that's a back-to-back connection between a laptop and the MX.
Are you saying there will never be a need again to connect directly to the MX for mgmt once initially configured? If I want, for example, to have an internal monitoring (ex. SolarWinds) detect device up/down would I want to configure the LAN ports for that purpose?
At the branch, would you just bind both Corp and Guest SSID's to the same VLAN, so I wouldn't need to build a L3 subnet at the branch for Guest clients?
And, for VLAN 600 in your example, does that subnet need to be scoped to have enough addresses to support the projected number of clients being tunneled to that device?
Lastly, if we only configure WAN interfaces for an HA pair, I assume that network is where the VRRP address also sits, or is there a VRRP address for ever VLAN the MX's connect to?
Thank-you, Parker
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
As mentioned here if you need to set a static IP on a MX you can use the local status page accessible by the dedicated mgmt port (if your MX model has one) or connect a laptop to a LAN port.
After initial setup you no longer use any LAN port in Concentrator mode. Reference
Mgmt of any MX regardless of mode is via the WAN port(s) talking to dashboard.
At a branch a guest tunneled SSID looks like this example config. In my example VLAN 600 only exists in the DMZ and the upstream edge MX. The DMZ MX is what places the tunneled guest onto the (local to the DMZ MX) VLAN.
And yes your DHCP server, whatever it is, needs to be scoped to have enough IPs for all guests.
And yes in Concentrator mode the HA VRRPs go out on the WAN interface. Again, you don't use any LAN ports.
All that said, is your branch using a MX appliance and if so is it doing AutoVPN back to the same guest anchor MX? If so, this likely won't work as outlined in this doc mentioning the double tunnel problem.
Also, is there a specific reason to tunnel guests back to a central location? The far easier way to provide guest WLAN in Meraki is by using NAT mode. Guests are segmented from corp devices, P2P isolation is enabled, no need to manage any DHCP scopes, and no need for more MXs sitting in a DMZ.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello Ryan,
Can you please answer a few questions?
Why do you have VLAN 85 on WAN 1 IP?
Do I Firewall NAT the MX WAN IP for VLAN 85 or 600?
Do I configure DHCP on the MX or Firewall for VLAN 600?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi everyone. We are in the process of rolling out Meraki AP's in all of our locations. We have WAN connectivity between all sites on the 10.0.0.0/8 network. We purchased a pair of MX-450's to be VPN concentrators at one of our sites. The goal is to do SSID tunneling for our Guest wireless network. Ideally, we want to tunnel the traffic to the firewalls, then egress directly out to the internet from the MX450's. Initially, based on the documentation, I had thought that we had to deploy the firewalls in a One-Armed Concentrator mode. Now I'm reading that we can do a Routed Mode Concentrator deployment, which was good news for us, as we do not want to have to add any additional infrastructure to make this work. The question now, for us, is how the tunnels are built. Ideally, the tunnels between the AP's and the firewalls will be established between the private 10.x.x.x ip addresses of the AP's and the Firewall's LAN interface. But nobody from Meraki Sales or Support has been able to answer that question.