- Technical Forums
- :
- Switching
- :
- Re: Proper STP port configuration for Core switches on two separate network...
Proper STP port configuration for Core switches on two separate networks
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
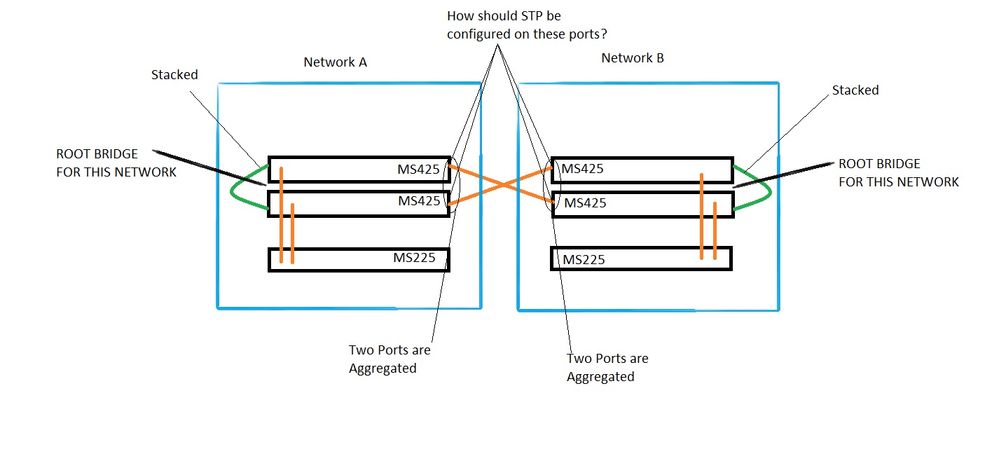
Proper STP port configuration for Core switches on two separate networks
I have two networks that have a pair of stacked MS425-32 switches as the root bridges on each side. These networks are setup as two separate networks on the Meraki dashboard and they are each configured to be the root bridge in Switch Settings for their network. These two pairs of core switches connect to each other with two fiber connections. I want to make sure that these two sets of switches remain the root bridge for their sides of the network. Currently I have RSTP disabled on the aggregate ports on the MS425 stacks. STP Guard is set to Disabled. I don't think this is the right setup. I don't want spanning tree updates on one network to effect the other network, possibly causing an issue with which set of MS425's is the root bridge - each set should be the root bridge for its side of the network. How should STP be configured on the ports that connect these two networks together on the MS425 stacks?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@skifdank why do you have them as two separate networks and then have them direct L2 connected or are they using a transit VLAN and only routing over this connection?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@cmr Its a transit VLAN on the connections between the two core switches that we use to route traffic between the two networks. Both sides have a set of MX firewalls on top that we use for internet and auto-vpn failover in case the link between the two switches goes down. Geographically the sites are a couple miles apart.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @skifdank , I believe the configuration to be correct on those switch interconnect ports. If you have RSTP disabled on those ports then no Spanning-Tree information will be processed.
Are you seeing any STP errors in the event log for either network?
Enabling RSTP on a Switch Port
In the RSTP field of the switch port configuration menu, you may select Enabled or Disabled.
| Option | Description |
| Enabled | RSTP must be enabled globally (see "Enable RSTP Globally") for any ports to be able to participate in Spanning Tree processes. When RSTP is enabled globally, RSTP will be enabled at the port level by default. A disabled port can be re-enabled by selecting Enabled. While RSTP is enabled on a switch port, that port is able to participate in Spanning Tree processes. It is recommended that RSTP be enabled on all ports. |
| Disabled | RSTP may be disabled at the port level. Disabling RSTP on a port removes the port from any STP processing including any STP guard configuration. Disabling RSTP on a port is not recommended unless the client device connected to the port is incompatible with STP. If RSTP is disabled globally, all ports will have RSTP disabled and cannot have it enabled. |
https://www.linkedin.com/in/darrenoconnor/
I'm not an employee of Cisco/Meraki. My posts are based on Meraki best practice and what has worked for me in the field.
