We're migrating to the Cisco Community on March 31. The Meraki Community will enter read-only mode starting on March 26 through March 31.
Learn more- Technical Forums
- :
- Switching
- :
- Re: Meraki and Comcast EDI
Meraki and Comcast EDI
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Meraki and Comcast EDI
So have a new internet circuit from Comcast and its delivered via their EDI. So they have a ciena device that does a Layer 2 passthrough copper handoff for CPE. Problem is its only one interface and they give us two subnets a /29 and a /30. From their documentation:
You receive two subnets from Comcast with Comcast Business Ethernet Dedicated Internet (EDI) circuits:
Wide Area Network (WAN) point-to-point connection between your network and Comcast Business
Public LAN (Local Area Network) IP Block
WAN Point-to-Point Connection
In an EDI plan, the WAN subnet is typically in the form of a /30 (255.255.255.252) network since the circuit is a point-to-point connection type.
Note: Comcast’s standard configuration is to use the /30 WAN point-to-point IP block. It is possible to have the WAN subnet in the form of a subnet larger than a /30, however this is an individual case basis that must be approved by Comcast Business.
The WAN point-to-point network provides security against Denial of Service (DOS) spoofing attacks and a clear demarcation point between your routed networks and Comcast Business.
I have a Meraki MS350 that can do layer 3 and an MX100 meraki appliance. Anyone have experience with this that could help me figure out the config?
Thanks!
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
One of your firewall's WAN interface could then get the following settings:
IP: 50.x.x.49
Subnet mask: 255.255.255.248
DFGW: 50.0.0.54
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@leadtheway I would think you simply connect the MX100 WAN1 interface to the EDI handoff as a WAN point-to-point connection, and if it cannot get a DHCP address from Comcast (if hey instead provide you with an IP), then you can connect locally to the management port of the MX and prime it with the static IP and DFGW settings to get it online in Dashboard. For more info on that piece, search the documentation for "local status page" and it's the first result. And your MS350 would just sit behind the MX, I was assuming it's a NAT/Routed mode MX and the MS350 is on the LAN side on one of the local VLANs (configured on the Security Appliance > Addressing and VLANs page for the MX). Sorry if I didn't understand, wasn't sure what you were trying to do, or might have already tried (or not) and if something wasn't working.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes indeed. They even give an example in the docs:
Provided IP information to Comcast:
Point-to-Point (P2P WAN Block): 107.0.74.0/30 ( Subnet mask: 255.255.255.252)
Provider (ISP) IP Address: 107.0.74.1
Customer IP Address: 107.0.74.2
Customer Allocated Public IP Block ( LAN Block): 24.102.88.0/24
Usable IPs: 24.102.88.1 – 24.102.88.254
DNS :Primary: 75.75.75.75 / Secondary: 75.75.76.76
So like @MerakiDave said, you assign the 107.0.74.2 Subnet mask: 255.255.255.252 address to the MX (if it doesn't get that from DHCP). Comcast will have a route for the 24.102.88.1 – 24.102.88.254 on their infrastructure so it forwards all traffic for those destinations to your MX @ 107.0.74.2. You can then choose how to do your L3 design.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Doing it that way , how would I get other devices access to the /29 block? I have other routers/firewalls that need ips from that block?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
1. One way to do this is like in this guide:
You could also use access ports on the MX directly instead of trunking towards the switch.
But then your other firewalls/routers are behind the MX's security curtain which might not be what you want.
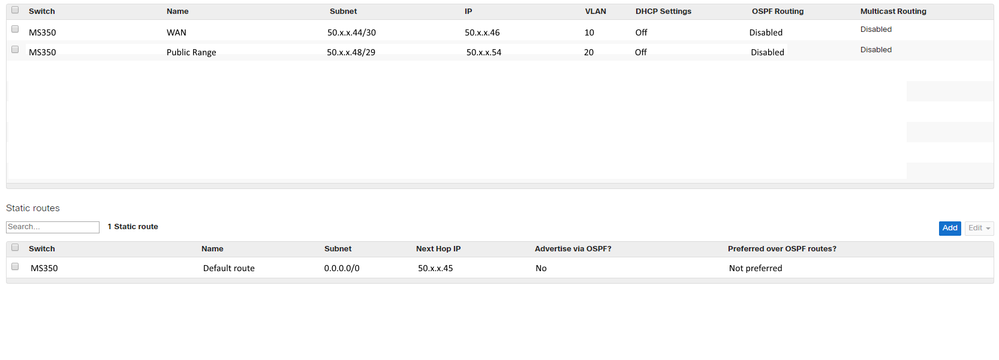
2. Another topology you could make is to use the MS as router. To do that you would create two "interfaces" (which are actually VLANs) in the Switch/Routing & DHCP page. One interface with the /30 and another with the /29 range. On the same page, a bit lower make sure the default route's next hop IP points to the other /30 address (the one the ISP is using).
Then you configure an access port for the VLAN you chose for the /30 and connect that port to the ISP router. And you create a bunch of access ports for the /29 VLAN. You connect those ports to your MX/routers/FW.
This way the security will need to be handled by each device for themselves in the /29 VLAN of course. The only thing you can do in this setup is some ACLs on the switch.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Option 2 is what i was thinking might be the route, so basically create two vlans put one interface in the /30 vlan and plug that into the comcast equipment and on the second vlan for the /29 just connect devices that need an IP from the block to interfaces in that block. The DFGW for the /29 will be the /30 IP address assigned in that /30 vlan?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
No, the default gateway for the devices in the /29 network will be the /29 address you assign to the switch (the IP column in the interfaces table in Switch/Routing & DHCP).
This way the messages are sent to the MS. Who then will forward them to the comcast equipment due to the default route you setup (second table on the same page).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
So the default route on the MS will be a 0.0.0.0 pointing to the ip of the /30 vlan?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes indeed, but not the one you assigned to the switch. The one that comcast assigns to its equipment. Otherwise the switch sends the message to himself.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
the same DFGW that was assigned to the /30 vlan interface IP
so basically this is what I'm working with
| Wan/30 | Lan/29 | Device | |||||
| IP | 50.x.x.46 | Usable Range | 50.x.x.49 | MX 100 | |||
| Subnet | 255.255.255.252 | 50.x.x.50 | |||||
| GW | 50.x.x.45 | 50.x.x.51 | |||||
| 50.x.x.52 | |||||||
| WAN usable ip addresses | used for | 50.x.x.53 | |||||
| WAN | 50.x.x.46 | MS350 | 50.x.x.54 | ||||
| WAN | 50.x.x.47 | Subnet | 255.255.255.248 | ||||
| GW | 50.x.x.45 |
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
One of your firewall's WAN interface could then get the following settings:
IP: 50.x.x.49
Subnet mask: 255.255.255.248
DFGW: 50.0.0.54
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Perfect. thats really easy to understand. Just curious, I can still use the MX100 for the gateway for our internal vlans right?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Also, will the ports on the firewalls that plug into that /29 vlan on the MS have to be in access mode with those vlans also residing on the MX or whatever other router
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The instructions I gave are for using the switch for providing the /29 LAN to other devices.
The MX's WAN interface will be connected to this switch in the /29 subnet, just like the firewall's IP settings example I gave. Its LAN interface would be connected to your access switches.
It's possible to use the same switch for both tasks. But then the setup becomes a little more complicated. Basically then you would define yet another VLAN "Access VLAN" with a private IP range of your choice. And then configure some access ports for it. One of those you connect to on of the MX's LAN interfaces. The default gateway for your clients then becomes the IP you gave the MX in that "Access VLAN" you defined.
Trunk ports are necessary when you want multiple VLANs to cross a single interface. In this design no trunks are absolutely necessary as all ports can be made dedicated for a single VLAN. You'll see that there are two cables running from the MX to the switch. By using a trunk you might be able to limit that to one. But then again the setup becomes more complex and therefore harder to maintain/troubleshoot.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
yeah thats my dilemma, I need to use the MS as an access switch as well, and there are a couple different vlans that need to be on it for wireless/lan/printing etc
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
An update: so configured as discussed and the MX works fine. My problem now is currently the MS350 has a port plugged into a backup internet connection via cable modem we used to get it online (port 48). It gets a private dhcp address from that modem, when we unplug it, it loses connection to dashboard. I'm guessing something else needs to be done to configure a management IP?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Try setting the management VLAN to be the /30 VLAN because that's the VLAN the switch will reach the Meraki cloud on.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
no address needed? is Lan IP needed?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
when i set vlan to /30 i get
This device is using a DHCP IP address from VLAN 1 instead of using configured VLAN 999.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
ok i changed it back to vlan 1 and plugged into the MX for the time being on a switchport and the default DHCP server on the mx handed out an address. So that works like that.. but moving forward, I would assume that I would change that to a trunk port as I add more vlans on the MX?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Tbh I'd have to test how the management IP exactly needs to be configured, I'm not sure. Have you tried entering 50.x.x.46 as IP and the VLAN ID you used for your /30?
Indeed, if you add more access VLANS it's probably best to set the port used for the connection between the MX's LAN interface and the MS to trunk mode, otherwise you need to sacrifice a port on the MX for each VLAN.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I should be able to add the vlans for the network to the MX and switch that to a trunk and then be able to change the management vlan to the one i create on the MX as well as any other vlans i should be able to have access ports on the MS correct?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Just ask Comcast for a /29 WAN range. Inform them, if accurate, that you will/might be setting up an HA firewall and need 2-3 public IP addresses. It's also handy to have at least a /29 for testing and firewall migrations.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sorry to drag up an old post, but I'm having the same issue with ATT and a single handoff but a HA pair of MX105. Since they're HA, is the only solution a layer 3 switch in front of the MX pair? This was my first inclination, and I tried first with a MS120 and now a MS220 but still struggling.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Swapped out the MS220 for a MS350 and it works kinda sorta. MXA is up with the assigned address in the /29 but MXB says "not connected" even though I can see pings to it's assigned WAN interface on the pcap - it just doesn't respond.