We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Switching
- :
- Re: MS 425-16 integration with Fortinet
MS 425-16 integration with Fortinet
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
MS 425-16 integration with Fortinet
We will have an infrastructure renovation.
And the equipment that we will use will be MS 425-16 (core) and MS225-48 (access)
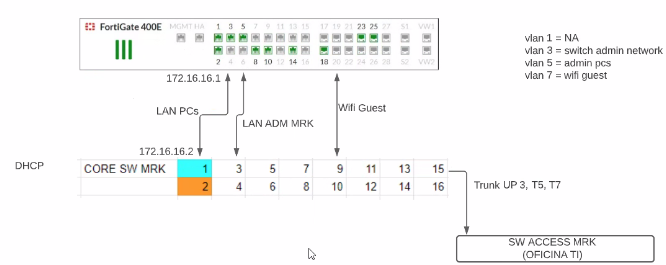
Scenario 1
The MS 425-16 (core) will be connected to the Firewall (Fortinet)
In total, 7 Firewall cables will be connected to the MS.
Namely:
1 cable will be for the (VLAN & SVI) of wifi guest.
1 cable will be for the LAN (VLAN & SVI)
1 cable will be for the (VLAN & SVI) of admin switches.
....and so on
And also the MS 425 want it to be the DHCP
And it is intended to reach the following, as shown in the following image
I do not agree, because meraki does not allow me to assign an IP to a specific port.
The ports can only be access or trunk but not L3.
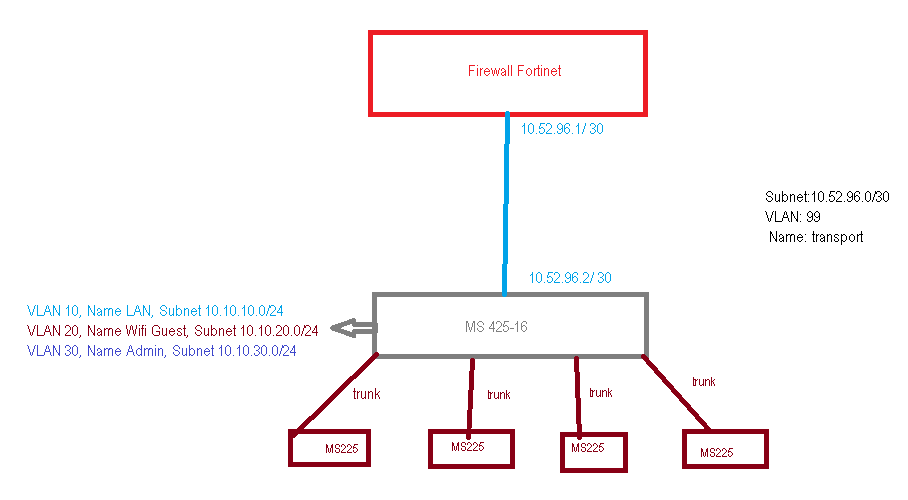
Scenario 2
I have commented having only 1 cable from the MS to the Fortinet and creating a transport VLAN between these two devices and creating the different VLANs in the MS.
When creating it I will already have a default route from MS425 to the fortinet and in this way it will allow me to create my VLANs and also run the DHCP
the scenario is possible ???
is the scenario correct ???
- Labels:
-
Interfaces
-
Layer 2
-
Layer 3
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Both are acceptable options. It mainly comes down to design preference.
One thing to be aware of with option 2 is that you'll have an SVI for each network on the MS, and therefore the ability to route between the networks. If you want to prevent this, you'll need to use Meraki ACL's which (in my opinion) will probably be harder to manage than Forti's stateful firewall rules and zones.
Assuming the Forti can do SVI's, a 3rd option you could consider is having a single link between the MS and the Forti with all applicable VLAN's trunked up.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
but how could I assign an ip to the meraki port??
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can't apply IP addresses directly to the ports on Meraki. You will need to use Vlans and SVI's.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We have done something very similar except our gateways for vlans are on the fortigate, DHCP/DNS provided by fortigate
2 X 10Gb Aggr port with trunked vlans from MS425 to Fortigate.
We find better visibilty and ease of management by letting the fortigate handle services.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That's a good idea, but we want the MS425 to manage L3 and not the Fortigate.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Create SVIs then you just net to create routes, It's very simple:
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Both options are great MS425 or Fortigate depending on as others say your traffic needs.
We have no on prem servers or the need for client to client traffic, everything is cloud. Hence we let the Fortigate do all L3 services.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is much traffic going to be flowing between these VLANs?
If not, have you considered putting all the L3 interfaces on the firewall, as well as DHCP? And only using the switches as L2 devices, rather than L3?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Currently the firewall is L3 and DHCP we want to take that job away from the firewall
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We are doing a similar thing with MS425-32 and a Fortigate and we went with your option 1 approach simply because of the limitation of supported ACL's on the MS, not sure if those limitations have changed but this was setup a 2-3 years ago now.
If using the FGT for L3 just make sure you specify the right size hardware for the job. While switches can do your L3 routing firewalls also have the ability to scan traffic for viruses whereas a switch cannot.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In smaller network you can do L3 on the firewall instead of the coreswitch. However in campus networks with multiple buildings or routed access designs you cannot have that and then you have to rely on switching to do the intervlan security OR you can use VRF's which is a feature that is missing on Meraki switches. That is why the combination Catalyst in core/distribution and Meraki in the access layer is also a good design. This is the whole reason we have Catalyst monitoring now.
On small secret about Catalyst switches and "routed interfaces". When you create a routed port on a Catalyst switch in the background the switch creates an internal VLAN which you cannot configure starting at 4094 (if internal vlan policy is descending) and only assigns it to the "routed interface" and disables some layer 2 protocols like STP on that port. So in essence you can do the same on your Meraki switch. You create an otherwise unused VLAN ID and assign it only on one port and then create an SVI with the correct IP.
About the DHCP thing. You should do DHCP on the device that is routing or on a separate server(which is better). If you want to do DHCP on your coreswtich you can only do that if your gateway lives on the coreswitch.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@GIdenJoe is correct. You need to consider the packer per second load on the firewall. I've had to move a customer that was using an MX250 for all the L3 SVI and DHCP to their MS410-32 because of CPU overload. Firewalls don't operate as inter-vlan routers well. You need to know the PPS processing power of the Fortigate in order to make an educated decision.
A MS425-16 as a PPS forwarding rate of 357.14 Mpps - roughly 21 Gbps at 8 bytes per packet between L3 interfaces.
In contrast, an MX250 only has a PPS forwarding rate of 95.23 Mpps - roughly 5.5 Gbps at 8 bytes per packet between L3 interfaces. This doesn't take into account all the extra work the process needs to do firewall processing and anti-virus and threat protection processing primarily. A switch does not need to perform these additionally tasks and has more dedicated CPU time to perform extra duties such as DHCP.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi do you have a source for the MS425 forwarding rate please? Struggling to find anything online.