We're migrating to the Cisco Community on March 31. The Meraki Community will enter read-only mode starting on March 26 through March 31.
Learn more- Technical Forums
- :
- Switching
- :
- Re: L2 v L3 Setup
L2 v L3 Setup
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
L2 v L3 Setup
A bit of a Meraki noob, so please accept my simple question. (been >20 years since I did my CCNA, and we were talking Token Ring, and VLANs were "new")
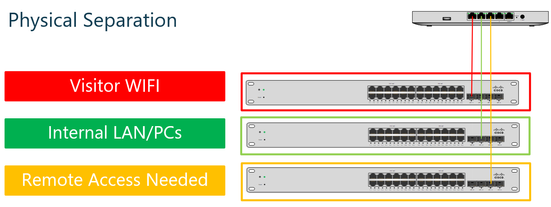
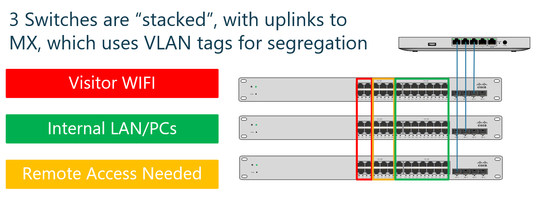
Whilst I think, both the below configurations are technically possible (MX64 and MS120), I would appreciate the expert’s opinion on which is better, and the virtues of changing the MS120 for a device that can do L3 Switching.
And, I am not seeing in the documentation, how I can assign a separate subnet range to each segment, because I would like to use the MX to assign rules/logic to what can and can’t be allowed in/out of each subnet and between subnets. Is this indeed possible with the proposed devices
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You want to enable VLANs on the MX and assign a subnet to each there.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If I understand what you are doing correctly, you appear to be over complicating what you want to achieve.
Meraki supports the use of an isolated guest WLAN. This funnels guests to the internet and saves them from each other.
I an unsure of what the purpose is of the "remote access required" switch - use VLANs to separate classes of users, a port may be configured to pass traffic from multiple VLANs.
I build a logical VLAN architecture from a requirements and security perspective and then configure the network devices to implement the logical model in the physical devices.
With an MX64 as a gateway, I doubt that traffic volumes through the local network will be an issue as the MX64 has a maximum throughput of 200 Mbps.
 @uberseehandel
@uberseehandel
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you for the rapid response.
It's a mixed "Industrial" and "Commercial Office" location, with devices ranging from cameras, to clocking in/out systems, scales, temperature control, production line control, office printers, and packaging/commercial label printers. There is both visitor and guest WLAN required, and also there are presently some server systems, print controllers, and in future an expansion of additional "segments" is likely.
I understand the Guest WLAN isolation and it is a consideration, but there is also a desire to separate out other parts of the infrastructure.
The "Remote Access Needed", was my way of illustrating that some of the internal systems, will require the ability to be accesses remotely, and I wanted to keep them separate from other systems, such as those above. My diagram was overly simplified, but given some recent on-site issues, I want to separate the infrastructure as much as is logically and physically possible (without having to run new cabling), with a view to being able to isolate hosts if/as needed, control the traffic to/from them on a per device basis. I think, will probably end up with about 8 "segments" in total, and I would like to be able to control it at a minimum a segment level, but potentially at a per host level.
Bandwidth is currently a significant challenge in this location, so controlling non-critical traffic is also key.
Thank you again.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@jmgwozhere I'd physically separate the industrial part from the commerrcial. Does the industrial even need internet / remote access?
For the commercial / visitor VLANs, ideally you'd have a L3 switch (such as an MS210) but if you've only got what you have then I'd stack the remaining switches and us the wireless NAT for the guests
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You want to enable VLANs on the MX and assign a subnet to each there.