- Technical Forums
- :
- Switching
- :
- Re: IPv6 ACL Deny Any drops all IPv4 traffic
IPv6 ACL Deny Any drops all IPv4 traffic
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
IPv6 ACL Deny Any drops all IPv4 traffic
I think I made a silly mistake but I do not quite understand it either.
I dropped a whole Meraki Network of 40 odd switched by applying an ACL.
The idea was to block all IPv6 traffic as I did not want security holes on the network and IPv6 is not a requirement yet.
Anyhows as soon as I applied the IPv6 Deny Any Any it dropped everything from switch management to OSPF everything. Perhaps it was not the brightest moment, but I still ponder why though. Why would an IPv6 Deny any drop everything else.
So I thought if I could at least get the management up to revert the change it might work, so I cycle the port from another Aggregation switch downlinking to this network, I do not even see a dhcp request which is a broadcast.
I guess I am going to have a long day resetting switches tomorrow 😞
Just curious if anyone else has played with IPv6 ACL's and experienced the same thing?
May 22 22:14 ipv6 deny all // Deny IPv6May 22 22:15:12 105.247.201.14 logger: <134>1 1527020112.408011792 ESL_ML_AGS_M32_01_03_Service_Tunnel_ICT_Room_ events type=ospf_neighbor_down ip='10.0.1.81' router_id='10.4.0.1' vlan='1112' May 22 22:15:13 105.247.201.14 logger: <134>1 1527020113.454672201 ESL_PL_AGS_P14_01_02_Chefs_Quarters_ events type=ospf_neighbor_init ip='10.0.1.94' router_id='10.5.0.1' vlan='1112' May 22 22:15:14 105.247.201.14 logger: <134>1 1527020114.457921800 ESL_ML_AGS_M32_01_03_Service_Tunnel_ICT_Room_ events type=ospf_neighbor_down ip='10.0.1.110' router_id='10.6.0.1' vlan='1113' May 22 22:15:23 105.247.201.14 logger: <134>1 1527020123.587479040 ESL_KP_AGS_ICT_01 events type=ospf_neighbor_init ip='10.0.1.97' router_id='10.5.0.1' vlan='1113'
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
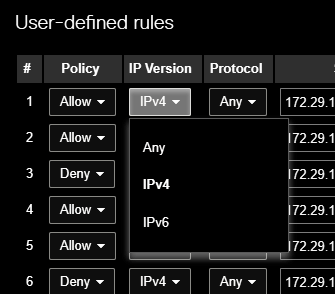
Where did you configure this? Because if I go to Switch> there is only IPv4 ACL.
If this was helpful click the Kudo button below
If my reply solved your issue, please mark it as a solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I think it could be part of the Beta Firmware, we upgraded to Beta as we needed to facilitate Multicast Routing.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yep must be part of the new features. I don't have that on 9.37.
If this was helpful click the Kudo button below
If my reply solved your issue, please mark it as a solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks yeah I did log a case I also think the code is buggy.
I was lucky as I saw in this article after 2 hours configuration reverts.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Note that blocking IPv6 may be risky anyway - modern Windows systems communicate between themselves using IPv6 as there preferred transport. Your internal systems may well be communicating using their IPv6 autoconf settings.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Unless the admin is disabling IPv4 on each endpoint's NIC, it should not be a problem.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Disabling IPv6 on every endpoint - what a pain to solve a problem that doesn't exist.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
There is a support case open for this. See comment below from support dated June 22nd.
Good news! I broke our lab. It took longer than in your network due to some validation checks that we do in our labs, but it looks like the switches are doing IPv6 DNS lookups (AAAA) as part of their connectivity tests. Now that I have it in a broken state, I need to do a few more granular tests, but I wanted to let you know that we have some progress!