- Technical Forums
- :
- Switching
- :
- Re: How do you setup redundancy between MS-125 switches and 2x MX250
How do you setup redundancy between MS-125 switches and 2x MX250
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How do you setup redundancy between MS-125 switches and 2x MX250
Hello guys,
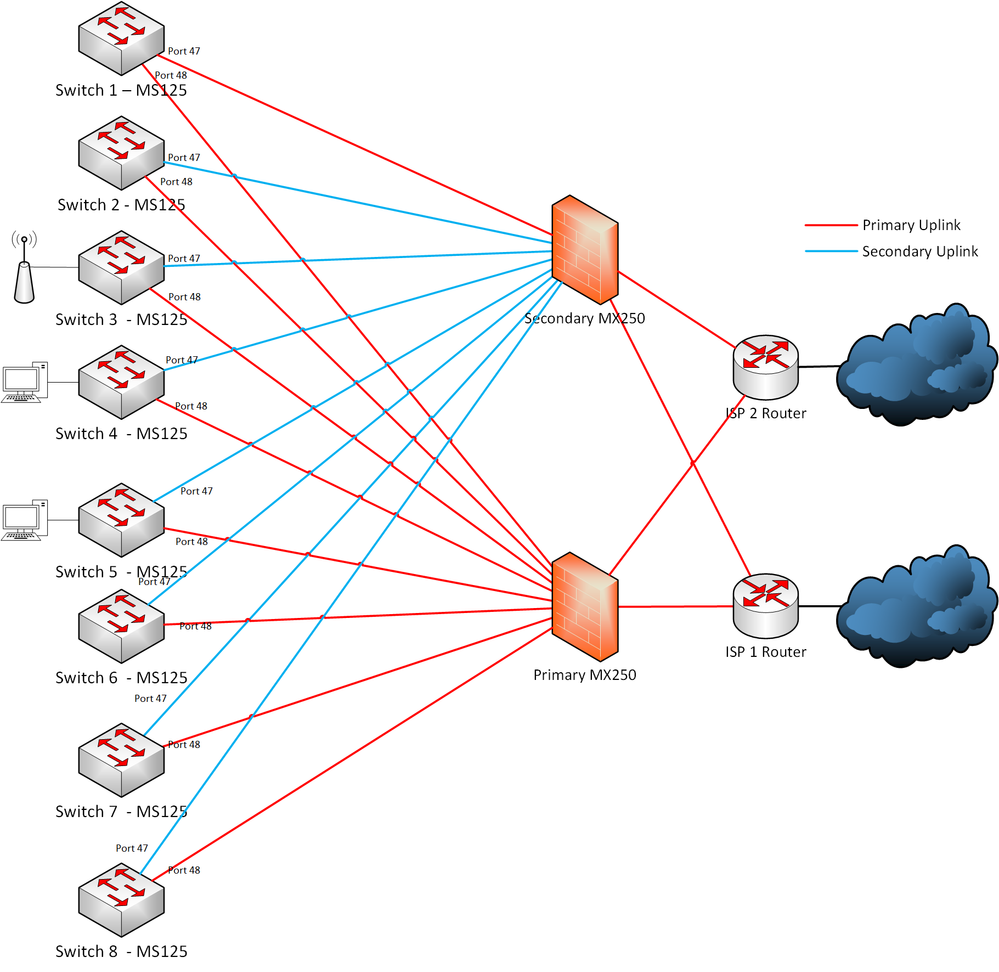
We have the following network topology but, we struggle with the RSTP configuration. (We have this topology to provide a maximum redundancy on the network and followed the recommendations from Meraki Documentation : https://documentation.meraki.com/MX/Deployment_Guides/MX_Warm_Spare_-_High_Availability_Pair#Require...
Red links are the ones we expected to be active when everything is ok and the blue are the redundant ones.
Ports 47 & 48 are defined in trunk mode and have the following options also activated : Unidirectional link detection & Loop guard
We have activated RSTP on the switches to avoid loop, but it seems to not do the right thing.
We also set the RSTP Priority to 0 on Switch 1 so it is the root bridge.
In fact, RSTP is blocking the Port 48 on Switches 2 to 8 (Which was supposed to be the main link to the Primary MX250)
Which makes the traffic coming from switches 2 to 8 to go through the Secondary MX250 (which is in passive mode) then go through switch 1 and finally to the Primary MX250, instead of using the direct link available...
How can we fix this, what are we missing ?
Would it be possible for example to do the following ?
- Set the secondary uplinks to only be used if the Primary MX goes down or,
- Set the spare MX250 to not do any switching while it's in passive mode.
Thanks for your help !
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
https://community.meraki.com/t5/Security-SD-WAN/MX250-RSTP/td-p/38708
MX250s do not participate in STP.
Hope this helps
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hey @atict ,
Given the number of switches you have you should introduce an aggregation/distribution layer instead of connecting all the access switches directly to the MX.
Also, there's this doc:
that says:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
maybe (not sure at all) this work if you give mx lan1 lan2 lan3 etc.. a different (unique) native vlan and not use that native vlan (tagged or untagged) on the other ports.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The MX250 cannot handle having more than two switches connected to it at a time???? A firewall with a rated throughput capacity of 4Gbps, 8 copper gigabit and 16 fiber 10Gbit capable SFP+ slots? You can't be serious. Really?
If this is really true, you should return the MX250 to your Cisco vendor and, assuming you can't get your money back from Cisco, tell him or her you want a Cisco Firepower 2120 or 2130, which can handle 3Gbps and 5Gbps respectively. I don't personally run Firepower but it's the product that's gotten Legacy Cisco back in the leaders' quadrant in Gartner for enterprise firewalls.
I am happy with our Meraki switch gear and APs but would not consider the MX from what I've read in these here forums. I don't have anything else positive to say about the MX, so I'll just leave it at that.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Brons2 This has more to do with proper architecture than anything else. If you have a heap of switches, you're going to get better behavior if you have a core switch stack that everything else connects to. Firewalls aren't intended to act as the core of a switched network.
This is especially true if you've got a heap of local traffic. Who wants to send that through a firewall, instead of a nice snappy core stack? One doesn't have to do a full core->distribution->local access stack in a lot of cases, but... like, have a core switch.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Nash yes, my network is architected as you say, it's the traditional network design. The aggregation layer is a stack of MS425s. However, the OP is only talking about 8 switches, it doesn't seem like a big ask to plug them into the MX.
On a side note, our firewall vendor actually advertises the ability the flatten your network and let it do all the internal core functions. We haven't actually done this, but it's pretty tempting when the MS425s are up for replacement. Firewall vendor X supports everything the MS425s are doing. Yes, it's not the customary network design, but the only constant in the IT world is change.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Change is a thing that exists, but I'm going to go out on a limb and note that no senior engineer I know would use a firewall to perform all routing for a network. That includes some folks who live at the bleeding edge of network development.
Vendors say a lot of things. Not all of them are good ideas.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm with @jdsilva .
Your could make two of the switches core switches, and connect all other switches and MX's to those. That option will probably cost you nothing.
It looks like you are using a lot of 10Gbe. If so, I would personally get a pair of MS425-16's and stack them together and then 10Gbe connect everything to them.
https://meraki.cisco.com/products/switches/ms425-16
If you only want a small amount of 10Gbe, then you could consider a pair of 24 port MS225s.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks everyone for your answers.
We’re gonna try with 2 core switches connected to the 2 MX's and then the rest of the switches will be connected to these 2 core switches as suggested.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Your topology is doing exactly what RSTP and classic STP does.
So switch 1 is the RB so that one will have both links in designated state and forwarding.
And all other switches will have equal cost on both links towards that RB. But since sending port 48 is numbered higher, port 47 will be the Root Port FWD and port 48 will be ALT BLK on the other switches.
So to fix your problem you have to make sure switch 1 port 47 goes towards the primary MX.
I myself however prefer not connecting the uplinks of access layer switches directly to an MX but going through a CORE switch stack which allows for better east west traffic. If both MX'es are in the same room you can also connect your MX directly to your CORE stack and then only two links i total would be blocked.