- Technical Forums
- :
- Security & SD-WAN
- :
- Re: vMX100 and Azure 0.0.0.0/0 route.
vMX100 and Azure 0.0.0.0/0 route.
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
vMX100 and Azure 0.0.0.0/0 route.
Hello everyone, I hope you guys can help me. I'm really desperate on this
We are using vmx 100 as a one-armed concentrator in our production environment, I have successfully deployed an appliance in a full mesh topology, created a route table and able to reach all our branch offices in site-to-site VPN.
By default when you create a route table in Azure the Internet traffic is going through the azure backbone, but
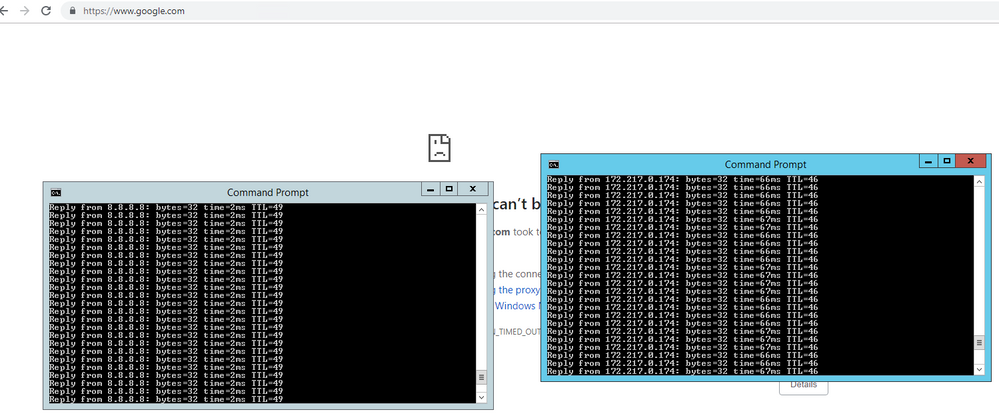
We would like to route all of our internet traffic out via a single IP which is our Meraki vMX 100. In Azure Route Table, I have created a new route (0.0.0.0/0) with the next hop type set to the virtual appliance 10.100.0.4. Well at this point everything works except I cant browse the internet. I can nslookup google.com, ping google.com 8.8.8.8 but unable to surf the internet.
Please help me
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Azamat wrote:In Azure Route Table, I have created a new route (0.0.0.0/0) with the next hop type set to the virtual appliance 10.100.0.4.
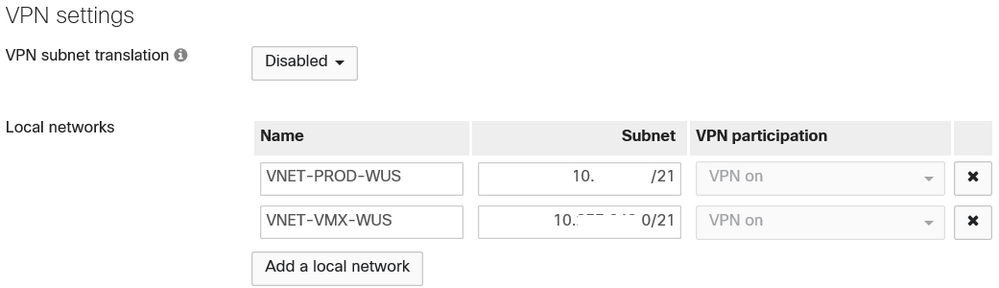
Have you added a route on the vMX back to to the Azure subnets?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Static routes are configured on the Security & SD-WAN > Addressing and VLANs page.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
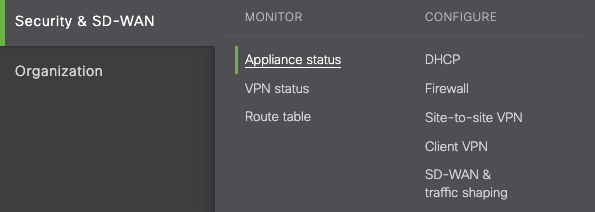
Can you ping URLs, such as, www.google.com or www.vmware.com
If you can, could you run tracetcp to verify which hop is broken?
tracetcp will trace the tcp port as tracert does on ICMP.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
hi @Happiman
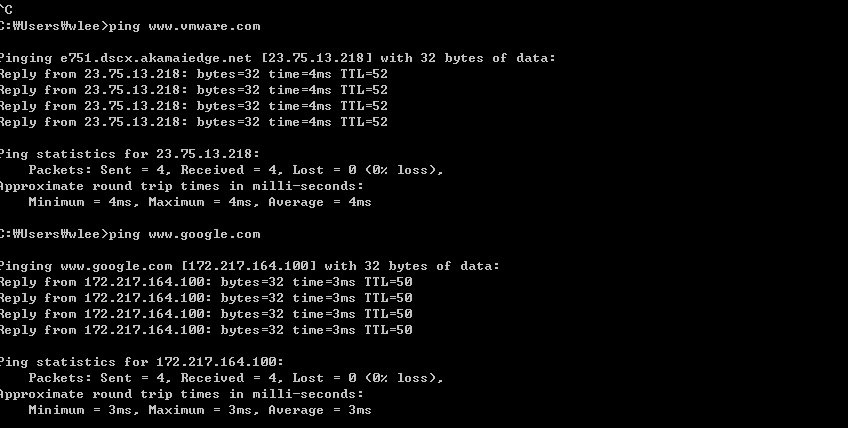
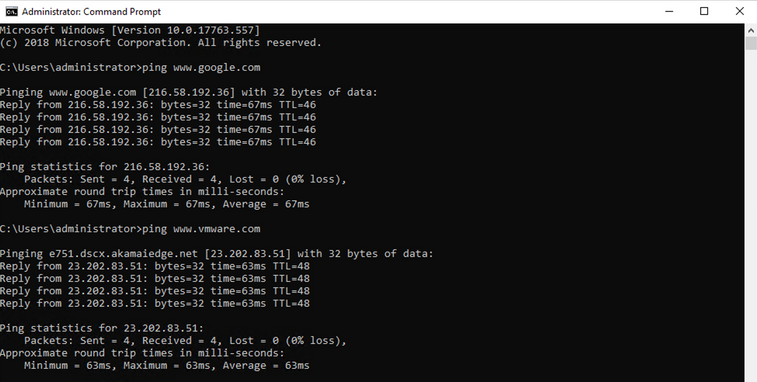
yes I can ping www.google.com and www.vmware.com
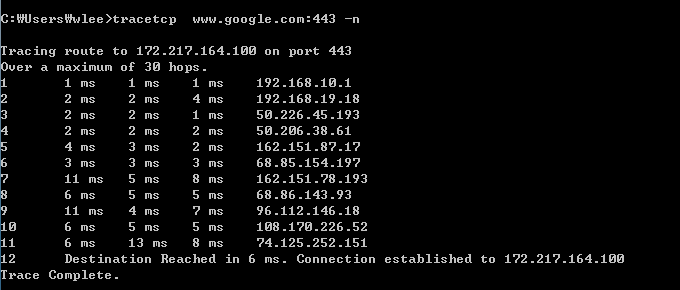
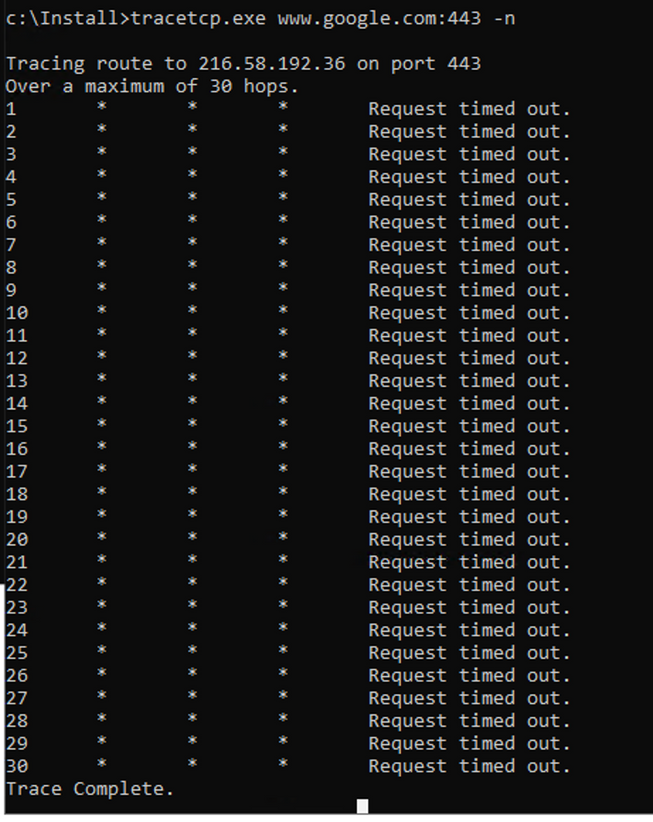
however, tracert and tracetcp give me the following output
do you have any idea why ?
Thanks!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I don't think this should work.
The VMX is a VPN concentrator. It doesn't do NAT.
And to the best of my knowledge, Azure will only do NAT for subnets located in Azure and not remote subnets - so that remote networks can't use Azure for Internet access.
Amazon AWS also imposes the same restriction.
To make this work you would need to configure a proxy server or an additional machine to be a NAT gateway (which I think in Azure would be really difficult).
You need to let your branches access the Internet directly via their MX(s) rather than via Azure.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
hi @PhilipDAth , please look at this article http://vmusketeers.com/2019/04/23/routing-from-a-single-public-ip-with-azure-firewall/ this guy has done it with Azure firewall. Is it possible with vMX100 ? my branches can access the internet via mx84, the problem is with my Azure vms, they cannot surf the Internet.
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes that klooks like it would work. You just need something that can do NATing for you.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
So we have a very similar setup. We have a vmx100 in Azure. We have a route table that is tied to the nsg and the route table has the 0.0.0.0/0 route pointed to the vmx100 internal IP which allows us to route all machines tied to the nsg back to our companies primary internet drain and that works, however - I can not get an internal azure IP tied to this nsg to NAT back out externally to our primary firepower that is tied to our public IPs that we want to use. This is super frustrating. Either I am missing something or this is just not supported my Meraki or Azure? I have had Meraki look at this and Cisco TAC and both agree we see everything passing inbound all the way to our Azure vmx100 interface on the site to site vpn but we never see any return traffic. So either Meraki is attempting to pass this out the public ip of the vmx100 (no packets are captured on this interface either) or azure is not able to accommodate this type of routing when an internal IP is attempting to go back out to a certain public IP that live out in the great big world. Super Frustrated!!
Edit - We do NOT want to use Azure Firewall!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The VMX100 would need to be running a full tunnel have to your DC to make that work. Is that the case?
Have you thought about getting a virtual Firepower for Azure?
-
3rd Party VPN
169 -
ACLs
101 -
Auto VPN
314 -
AWS
39 -
Azure
70 -
Client VPN
431 -
Firewall
713 -
Other
593