Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Re: non-Meraki VPN peer is not establishing with zScaler
non-Meraki VPN peer is not establishing with zScaler
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
non-Meraki VPN peer is not establishing with zScaler
Hello ,
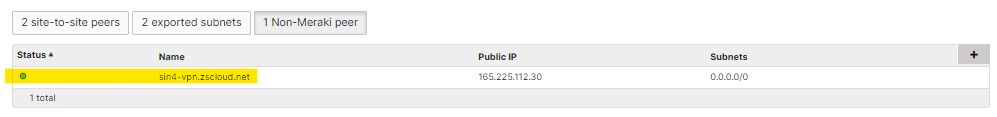
I'm trying to setup non-Meraki ipsec peer with zscaler.
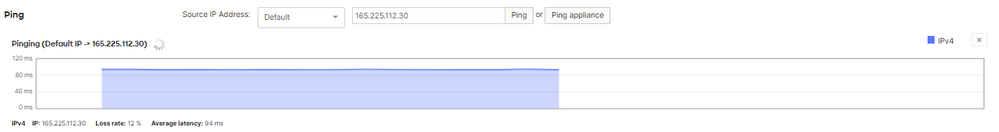
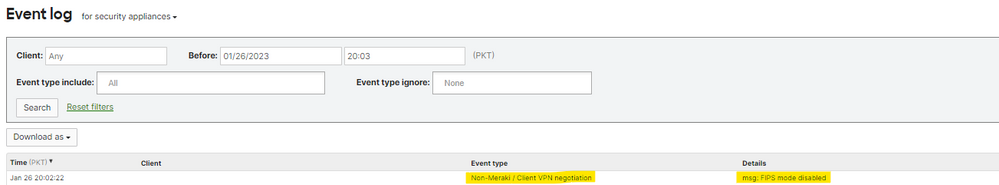
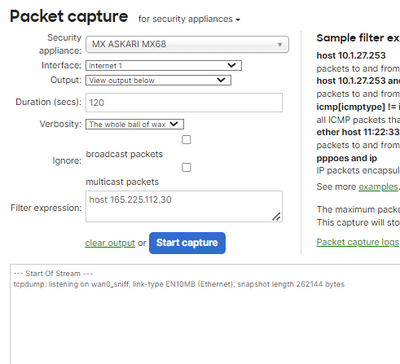
My MX68 device is directly connected to public network. I can successfully ping zscaler public IP from MX68. MX68 is not generating any kind of traffic to zscaler (checked via packet capture on MX68). The only thing which I found in Event Log is
Event Type: Non-Meraki / Client VPN negotiation
Event Details: msg: FIPS mode disabled
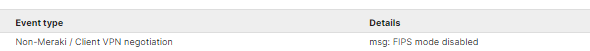
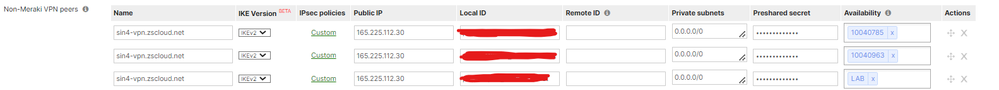
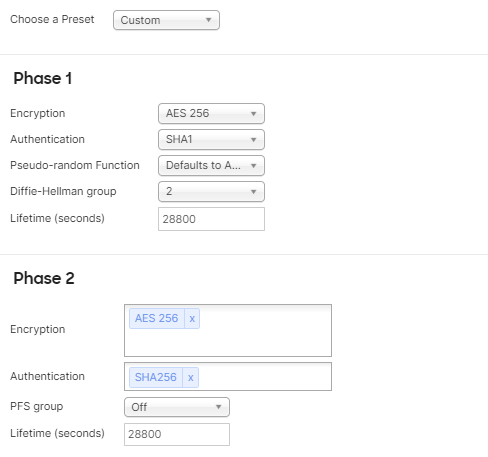
Here is the custom setting in non-meraki vpn provided to us by zscaler team.
Here is the result of capture.
Here is the ping response from MX68 to zScaler public IP.

I tried to find solution but no success, could you advice me what I can do?
Best regards,
Omar
Solved! Go to solution.
- Labels:
-
3rd Party VPN
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dear All,
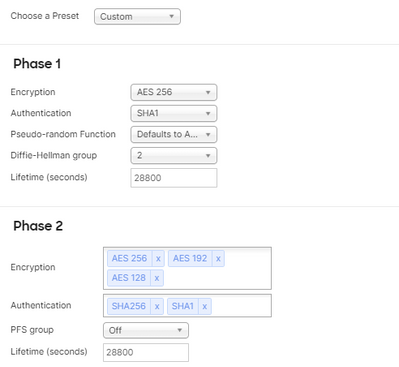
thanks for your valuable feedback and suggestions. Issue got resolved after contacting call support from Meraki team.
Here is the final settings of non-meraki vpn peer after that issue resolved in our case.
I thing i must like to add that the peer does not go up until we forward from traffic. That is one thing we have observed.
e.g.
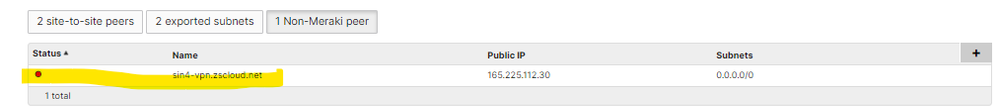
Here is the case that I can see that the route is active in routing table for non-Merkai VPN peer.
But when we see VPN status we found out that peer is down.
We thought in actual the peer is down. But when we send some icmp packet to zscaler then VPN status shows peer is up.
VPN status after icmp packet
We have observed that they are few drop for icmp packer at very start but after that ping observed normal with out any drops and peer shows up.
Another thing we have observed that if there is no traffic on the non-meraki vpn peer then VPN status again show red or peer down after few hours but if we send some traffic or icmp ping then again it comes to green (VPN peer up).
This is all we have observed so far.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Follow these recommendations:
Security & SD-WAN -> Configure: Site-to-site VPN -> Non Meraki VPN settings:
- Preshared secret must be greater than 14 characters
- Authentication cannot be MD5
- Diffie-Hellman Group must be 14
- Phase 2 encryption cannot be NULL
- PFS can be configured to be either off or 14
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
1. Preshared secret must be greater than 14 characters
Yes in our case preshared key is 16 characters.
2. Authentication cannot be MD5
Yes we are not using MD5
3. Diffie-Hellman Group must be 14
I have also check with "Diffie-Hellman Group must be 14". Same issue.
4. Phase 2 encryption cannot be NULL
Yes, In our case Phase2 encryption is AES256, AES192,AES128.
5. PFS can be configured to be either off or 14
In our case it is off. I have also check this with 14.
I have found this above setting from Meraki documentation and i have implemented this but or creation of non-meraki vpn peer, event log message is same. msg: FIPS mode disabled
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is your MX behind a CG-NAT?
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
No. Public IP is directly assigned to MX68.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
And also not even the first and last character of the password can be a special character.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In our case credential does not contain any special character.
first and last character are lowercase alphabet
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Have you tried it? https://community.meraki.com/t5/Security-SD-WAN/IPSEC-Tunnel-withZScaler/m-p/53769
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes I have tries this but same situation. However issue got resolved after getting call support from Meraki team.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Do you have any local subnet set to vpn on?
https://help.cloudi-fi.com/en/articles/3177550-cisco-meraki-mx-routing-tunnels-deployment
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes we have enable 2 local subnet for vpn at MX68.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Another thing i would like to add that below is the configuration of ours non-meraki vpn with zScaler. (peer not established)
While here is the configuration of another meraki dashboard of same customer a another country which is working fine.
Both non-meraki settings have its own credentials.
Also note that both MX have same version.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Open a support case.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have already opened case and check many options with support team. And till yet we did not find out the cause. That's why I have adopted this community so that may be i found some help from experts in meraki field. Mean while i am also in coordinate with support team for resolution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You've tried all possible options, maybe you can try with a different version.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can try changing the phase 2 lifetime to 3600s.
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Just tried with 3600s. Same issue.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Do you see anything in the MX event log on Site-to-Site VPN negotiation?
Like what you see? - Give a Kudo ## Did it answer your question? - Mark it as a Solution 🙂
All code examples are provided as is. Responsibility for Code execution lies solely your own.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In Event logs I only found this message. And this event only occurs if i delete peer and create new one. Changing a already created peer does not generate any log.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If you do a pcap on the MX internet interface, you should be seeing packets on udp/500 and udp/4500, as far as I recall.
Like what you see? - Give a Kudo ## Did it answer your question? - Mark it as a Solution 🙂
All code examples are provided as is. Responsibility for Code execution lies solely your own.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
But in pcap there is not a single packet for UDP500 or to destination zscaler peer ip.
I beleive MX68 is not able to generate any ipsec messages and event log is FIPS mode disable.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dear All,
thanks for your valuable feedback and suggestions. Issue got resolved after contacting call support from Meraki team.
Here is the final settings of non-meraki vpn peer after that issue resolved in our case.
I thing i must like to add that the peer does not go up until we forward from traffic. That is one thing we have observed.
e.g.
Here is the case that I can see that the route is active in routing table for non-Merkai VPN peer.
But when we see VPN status we found out that peer is down.
We thought in actual the peer is down. But when we send some icmp packet to zscaler then VPN status shows peer is up.
VPN status after icmp packet
We have observed that they are few drop for icmp packer at very start but after that ping observed normal with out any drops and peer shows up.
Another thing we have observed that if there is no traffic on the non-meraki vpn peer then VPN status again show red or peer down after few hours but if we send some traffic or icmp ping then again it comes to green (VPN peer up).
This is all we have observed so far.
-
3rd Party VPN
161 -
ACLs
88 -
Auto VPN
284 -
AWS
35 -
Azure
65 -
Client VPN
366 -
Firewall
827 -
iOS
1 -
Other
537 -
Wireless LAN MR
1