Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Re: W32.779C90C974-100.SBX.TG / ArchiveFile - Disposition Changed
W32.779C90C974-100.SBX.TG / ArchiveFile - Disposition Changed
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
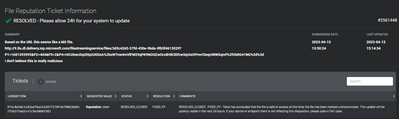
W32.779C90C974-100.SBX.TG / ArchiveFile - Disposition Changed
Getting THOUSANDS of alerts for this at the moment (SHA256: 779c90c974a4f1d927070cbff0d17f5d1daf7bd631603530a408c15ba7bd534b ).
Seems like a recent update to the Microsoft store Windows 10 app is being incorrectly flagged by AMP.
On hold with support now, anyone else seeing the same?
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello all,
This should be resolved now. The file has been mistakenly categorized as malicious causing this to fail. File deposition has been changed. We are truly sorry for the inconvenience. If the updates are failed, please go ahead and try again, they should go through now.
As of now, this is only related to Microsoft files. if you are also seeing issues with Adobe files or any other files. They should be considered as a different issue and please open a ticket with Meraki support for further investigation.
Regards,
Raj
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Only 480 events in the last hour from my network on the first email. I called support and they were about worthless until I got to the supervisor. I also emailed my sales person and the vendor I purchase it through.
| 8/1/2019 17:32 | File Scanned | http | http://11.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/65cc1083-07ec-42e5-b5dd-a39191... | 72.21.81.240 | 80 | 779c90c974a4f1d927070cbff0d17f5d1daf7bd631603530a408c15ba7bd534b | ZIP | 691677 | Malicious | Blocked |
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Same here, getting a couple hundred alerts.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yep - I am seeing this as well. I shut down the port the flagged pc is on but don't know the extent of what else this is. Is this really a windows 10 update to the store?????
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yep receiving quite a few warnings through MX with the same hash.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yep, got inundated with warnings from all my sites.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Getting the same here from multiple networks and machines.
Almost certainly a false positive from AMP - Unless somebody snuck something onto the store and AMP is the first to pick up on it.
Does anybody have a copy of the file?
VirusTotal has it at 0/56: https://www.virustotal.com/gui/file/779c90c974a4f1d927070cbff0d17f5d1daf7bd631603530a408c15ba7bd534b...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Any idea of the filename and location on a PC? I should be able to get the file if I know exactly which file.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Looks like the file names are
- Microsoft.VCLibs.140.00_14.0.27323.0_x86__8wekyb3d8bbwe.Appx
- Microsoft.VCLibs.x86.14.00.appx
Seems to be in the Program Files for Adobe
C:\Program Files (x86)\Adobe\Acrobat Reader DC\Reader
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This looks like a false positive.
This is a Win X Application Package.
One on my computer is there, scanned with A/V nothing, modified back in March...
Could be part of an update, which would explain why we're getting a lot of these alerts at this time.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Gryffindor - I see that filename in that directory, but on my system the hash (and last modified date) doesn't match that of the AMP reported hash.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have the same result.
Copied the file from one of the clients flagged by Meraki.
And the hash doesn't match the threat hash...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The hash of a binary file on disk won't necessarily match the hash Meraki sees, because Meraki sees the hash in the HTTP stream which is encoded (and possibly compressed).
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yeah i checked VirusTotal also - very odd - sure hope its a false positive.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We are getting slammed with this as well.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
getting hammered with these as well. Anyone got anything from support yet?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Undoubtedly a sophisticated new version of ransomware that is spreading throughout all Amp networks. Perfect for how I wanted to spend my night, looking up info on my networks spamming false positives.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Maybe Microsoft infected a malware with Windows 10 to slow it down?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Logged a case a few mins ago and called account rep in Aus who was at HQ with head of support. They will update me soon and I'll post here.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I opened a ticket as well and the tech rep said they were aware of the issue and working with engineering on resolving it
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
For the longest time I've been telling everyone that Windows is just one giant useful virus.
Glad to finally get verification.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I just got off the phone with support who said they are getting tons of calls about this, but are 100% sure it is a false positive and they have escalated internally to get it addressed so it stops flagging.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I've been cross checking related computers and network in Umbrella and not seeing anything, has to be a false positive I hope
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Also, Is anyone else noticing that the timestamp is not todays date?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Same Same, getting lots of flags and retroactive flags.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We're seeing this too.
Rapid 7 hasn't reported to us and Umbrella is showing nothing.
I'm with everyone else and hope it's a false positive!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Just Got off the phone with Meraki Support.
Representative said that it was a False Positive and AMP was blocking windows updates. Engineering was working to get it resolved. I had already opened a ticket so he posted the below information to the ticket and said the ticket would be updated when engineering had more information.
PROBLEMS DISCUSSED:
- AMP blocking Windows update.
------------------------
ACTIONS TAKEN:
- File in question: W32.779C90C974-100.SBX.TG
------------------------
NEXT STEPS:
- Further investigate this malicious activity.
- Keep the customer posted with updates.
[Mod note 1 August: Marking as solution for greater visibility!]
[Mod note 2 August: Un-marking as solution now that we have an update from Raj at Meraki]
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes - we did get alerts from our 120+ MX sites, I also remember this is not the first time AMP has incorrectly flagged Microsoft updates.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I got it too. Thanks for the info on it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello all,
This should be resolved now. The file has been mistakenly categorized as malicious causing this to fail. File deposition has been changed. We are truly sorry for the inconvenience. If the updates are failed, please go ahead and try again, they should go through now.
As of now, this is only related to Microsoft files. if you are also seeing issues with Adobe files or any other files. They should be considered as a different issue and please open a ticket with Meraki support for further investigation.
Regards,
Raj
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks. Does this also apply to the Adobe issue? Or just the Microsoft issue?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
At this moment. This is only in regards to Microsoft updates. Please open a ticket with meraki support if you are also having issues with Adobe files for further investigation.
Thanks and regards!
Raj
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
At this moment. This is only in regards to Microsoft updates. Please open a ticket with Meraki support if you are also having issues with Adobe files for further investigation.
Thanks and regards!
Raj
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have also received numerous alerts from the Adobe files mentioned by calebbaker. Can you confirm if the file desposition has been updated for this as well?
Detection: W32.7B512B45B6-100.SBX.TG
eutl12.acrobatsecuritysettings (SHA256: 7b512b45b6903b562e7f52b04a7715c05f0bb0cfc42438d6f1f2cdbb32124ac6)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The adobe files, I can’t help with checking the disposition on those. (Sorry). You’d likely have to contact Meraki Support.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Adobe files are no longer showing for me as Disposition changed.
Seem to be all good on both.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Great!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello @Dave2000 I am sorry to hear that. Is it the same update that is getting blocked again? Would you mind opening a support ticket for further investigation?
Cheers!
Raj
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Raj66 updated my ticket. I am sure the support guy Indy Cao is thrilled to see it still happening.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We're getting these as well on our FTD VPN FWs with AMP
<*- Network Based Malware From "VPN-FTD01" at Mon Aug 5 20:31:33 2019 UTC -*>
Sha256: 7b512b45b6903b562e7f52b04a7715c05f0bb0cfc42438d6f1f2cdbb32124ac6 Disposition: Malware Threat name: W32.7B512B45B6-100.SBX.TG IP Addresses: x.x.x.x<-23.204.228.68
However Talos shows it as clean...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is there a report available detailing this issue and what has been put in place to prevent this from happening again? Looking for something to send out to our clients detailing this false positive.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Josh214 It is rather unlikely there is a report yet. Despite the thread indication it is "solved", I still have 2 open cases with support.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In my case - this was partly due to a setting (my issue was with AMP on ASA firewalls but similar database) was that in the management console for the file policy you can tell it to override Talo's disposition based on the ThreatGrid score. TAC said because the way the update file works it is capable of being malicious so it gives it a very high threat score. In our case, we told our appliances to mark it as malware if the threat score was Very High. Not sure if this is relatable to you guys but wanted to mention it
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Heads up, just got a blockage for another update.
W32.B8E3DD9E82-95.SBX.TG
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Heads up, we just got a blockage for another update
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Ooof... nothing like a Thursday night fire drill!
Thanks to Meraki Support who took my call. Will watch for updates on my case.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Same thing over here...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for information!!!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Update: overnight I began getting these for Adobe as well. There's no update on my support case.
Has anyone heard back from Meraki Support on what's happening here? Last I heard they were investigating and the comment here marked as "Solved" implies the same.
Thanks.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, also seeing Adobe file being reported here.
2 Different Files:
eutl12.acrobatsecuritysettings (SHA256: 7b512b45b6903b562e7f52b04a7715c05f0bb0cfc42438d6f1f2cdbb32124ac6)
eutl11.acrobatsecuritysettings (SHA256: 3ed06a6ff00c0015e85609f509b11c3cdf0ab9991d74b1d44daab7c264fd99d9)
No hits for these on VirusTotal, coming from an Akamai server with an Adobe URL, so pretty confident this is false positive as well.
My feedback from support was that Engineering was aware of the issue, and I would get an update when it was resolved. I've not gotten an update yet and still seeing blocks for the original Microsoft file. So seems like original issue is still ongoing.
I've whitelisted the SHA256 in AMP in most of my sites, and that clears up the alert issue.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Got this too last night. Good to know that it was a false-positive.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I spoke to Meraki support regarding eutl12.acrobatsecuritysettings (SHA256: 7b512b45b6903b562e7f52b04a7715c05f0bb0cfc42438d6f1f2cdbb32124ac6) and they advised this is also a false positive - most likely due to outdated MX software. Check your MX version and see what you find there.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for the update either way... I'll ignore the Adobe stuff from last night.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Same here. Currently on hold with MERAKI. More than likely it's an update from Microsoft. Blocked the IP CISCO Endpoint until a determination can be made.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
CISCO is now marking them CLEAN in the Security Center Portal
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
yeah we had a firedrill today for SHA-256: 975c0d48c41d2ad76a242d5f7270f4bf8063bb9c753b375ab2c47c9e2060f562
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Intrestingly enough it came in from 72.21.81.240 - Edgecast in Dallas County, TX. If it was from Microsoft why Edgecast. I used ip2location.com to find out.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Exact same SHA-256: 975c0d48c41d2ad76a242d5f7270f4bf8063bb9c753b375ab2c47c9e2060f562 with same IP 72.21.81.240
I had a couple of users with the "Try New Outlook" toggle switch in Outlook yesterday, including myself. I took steps with registry edit to force the toggle switch to be seen by more users. I also believe that toggle switch in Outlook is not used anymore but I could be wrong. Long story short, I made changes late yesterday for Office 365 so certain users could access the Office preview channel. It might be a coincidence so please take this with a grain of salt.
(I am more or less "relieved" others are having the same issue so I know I didn't break anything....)
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If it's NOT broke don't fix it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I wasn't trying to fix anything. Just the timing of me making changes to our environment last night seemed suspicious to me. It looks like it was a Edge related update, based on other Meraki threads and specifically this one:
[RESOLVED] Security Center False Positive Alert - April 13th 2023 - The Meraki Community
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@lmorel It makes sense. I think Windows and Edge are a virus. 😆 Thanks for posting the update
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That approach used to work back in the 1950's.
Nowadays, companies that fail to innovate and change go out of business.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We didn't have the innovations back in the 50's that we do now. If it's NOT broke don't fix it. Besides what're we talking about, messing with the windows registry. You call that innovation?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Where have you been since 1995 while using Windows?? Still same ol' Windows with a fresh coat of paint, every other year. Microsoft is the one calling it innovation 😃
Unless you have no Windows client to administer then good for you and apologies.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If this is a Microsoft package update why is the originating IP 72.21.81.240 (edgecast.com) . Is this a Microsoft owned company? I'm sitll blocking the IP / port within my CISCO Secure EndPoint Advantage dashboard, Check it out for yourself. I use ip2location.com and type in the IP. Look at the results.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We are getting this as well.
File Name / Hash: | ArchiveFile / 975c0d48c41d2ad76a242d5f7270f4bf8063bb9c753b375ab2c47c9e2060f562 |
| File URI
| |
| Server IP | 68.142.107.4 |
-
3rd Party VPN
172 -
ACLs
91 -
Auto VPN
301 -
AWS
36 -
Azure
70 -
Client VPN
381 -
Firewall
856 -
iOS
1 -
Other
552 -
Wireless LAN MR
1