Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Source IP and/or VLAN mismatch-Meraki MX-64!
Source IP and/or VLAN mismatch-Meraki MX-64!
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Source IP and/or VLAN mismatch-Meraki MX-64!
Hello All,
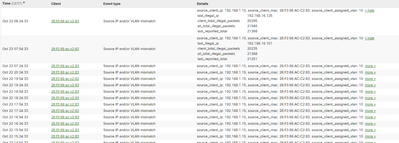
I am getting a lot of events: "Source IP and/or VLAN mismatch" from one device (I think is a camera).
source_client_ip: 192.168.1.15, source_client_mac: 28:F3:66:AC:C2:83, source_client_assigned_vlan: 10 « hide
| last_illegal_ip | 192.168.16.106 |
| client_total_illegal_packets | 19828 |
| all_total_illegal_packets | 20942 |
| last_reported_total | 20906 |
I dont understand why! Anyone have any idea?
Thank you,
Dena
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Does the camera have a static IP configured on the wrong subnet for the VLAN its sitting on?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
VLAN 10 (192.168.1.0/24) is the only vlan for all the devices. I have installed the MX a couple days ago. I didn't segmented the network.
Well I think is a static IP configured but in the same range (192.168.1.0/24).
It seems strange that on the event, it shows :
| last_illegal_ip | 192.168.16.103 |
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Dena, when you look at your Clients list, do you see the camera listed? What IP address do you see on it there?
I would recommend segmenting your network if you can. I realize it depends on the rest of your equipment. Was it previously segmented?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You're probably going to need to track that device down, it might have something misconfigured, maybe DNS or something strange.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes I can see it, is receiving Ip 192.168.1.15.
But the event keep showing again.
I will try to check that device closer.
Thank you
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @Dena,
If the target device reported on the event has been connected LAN interface or sitting downstream through the LAN interface on MX,
You can try taking packet capture and filter by the mac address to see which VLAN ID is actually added in layer 2 header for the confirmation.
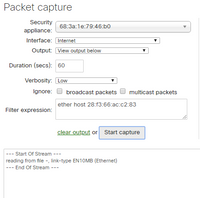
You can take packet capture from:
Network-wide > Packet capture > Set Security appliance as the target device and LAN port as target interface, then download it as .pcap format for you to load and analyse it on your Wireshark.
You can filter by "eth.addr:'Target mac address'" helps you to see traffic from / to the mac address.
Hope this would help your confirmation!
The Meraki ECMS exam is now live! Test your knowledge of Meraki and become an official Cisco Meraki Solutions Specialist. More info on the ECMS exam found here.
For information regarding all of Meraki's training offerings, be sure to check out the Meraki Learning Hub.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi hintoshi,
Thank you for your advice.
yes I have tried to sniff the packed but nothing is captured for this device.
Kind regards,
Dena
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @Dena,
Okay, it sounds like the device had not been generating traffic through LAN ports on the MX during the packet capture was going.
If the device is not generating traffic all time, you could try generating ICMP ping from MX to the device through live tool and take packet capture during the period to see return traffic from the device which would help you to see traffic from it.
Hope this would help!
The Meraki ECMS exam is now live! Test your knowledge of Meraki and become an official Cisco Meraki Solutions Specialist. More info on the ECMS exam found here.
For information regarding all of Meraki's training offerings, be sure to check out the Meraki Learning Hub.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I did performed ping as you advice me (although I can see that the device is doing traffic).
I cannot capture nothing from any client devices. The only captured traffic is of the routerboard that face the ISP (LAN-Meraki-Routerboard-ISP).
Thank you,
Denisa
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @Dena ,
Thanks for the update.
Do you mean you have captured interface toward WAN side rather than LAN side?
If you want to confirm how the VLAN ID in L2 header is, you need to capture the interface toward client side.
If the client sits on downstream of your network through LAN ports on MX, you can select "Interface" dropdown menu on Packet capture page to "LAN", and run the packet capture for LAN interface.
Hope this would help you out!
The Meraki ECMS exam is now live! Test your knowledge of Meraki and become an official Cisco Meraki Solutions Specialist. More info on the ECMS exam found here.
For information regarding all of Meraki's training offerings, be sure to check out the Meraki Learning Hub.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Hitoshi,
:)' my bad, I didn't notice the interface selection was Internet.
However I cannot understand a lot from the packet-capture. There are all the time arp packets between meraki and this linux device Shenzhen Bilian.
Then came up this IP 192.168.16.104 😕
Thank you for your help,
Kind Regards,
Denisa
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @Dena ,
No problem at all!
I am happy to see that you have captured actual traffic from the target device for your clarification.
You can copy same idea for that kind of clarification in future by using packet capture tool on your dashboard.
Enjoy your MX!!
The Meraki ECMS exam is now live! Test your knowledge of Meraki and become an official Cisco Meraki Solutions Specialist. More info on the ECMS exam found here.
For information regarding all of Meraki's training offerings, be sure to check out the Meraki Learning Hub.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Dena,
Did you discover the real problem?
-
3rd Party VPN
172 -
ACLs
91 -
Auto VPN
301 -
AWS
36 -
Azure
70 -
Client VPN
381 -
Firewall
856 -
iOS
1 -
Other
552 -
Wireless LAN MR
1