Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Since 802.1X device are renewing lease every hour
Since 802.1X device are renewing lease every hour
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Since 802.1X device are renewing lease every hour
Hi ,
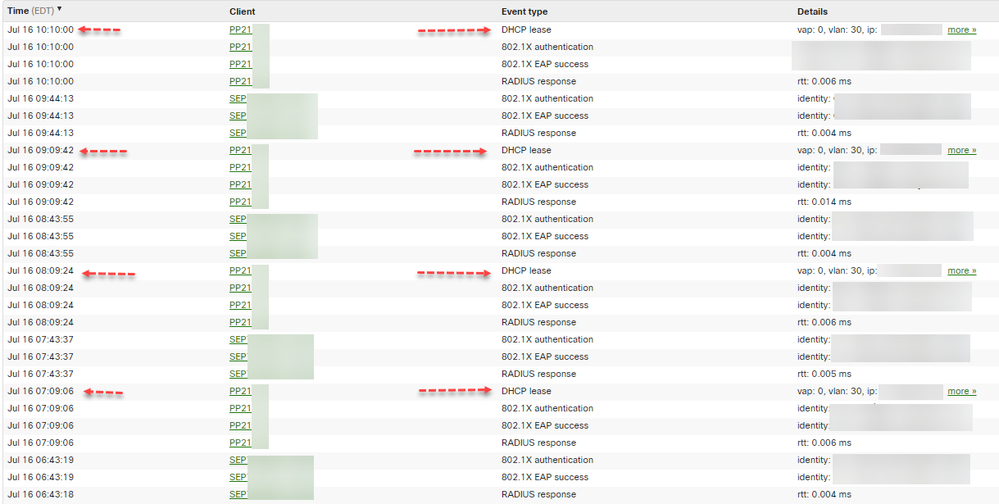
This is a fairly complex issue. We are running the 14.39 firmware with MX65(W) and MX68. We activated the 802.1X / MAB auth ( hybrid ) and since that activation every device is renewing it's DHCP lease every single hour ( 1 hour 16-18 secs )
This is annoying because it is flooding our logs and the lease we are giving to our devices are 24h ( should renew at 12h ) This is affecting all our 2k teleworker. Devices that are authenticated via MAB do not renew every hour. Cisco IP phones ( multiple models , also do not renew but are reauthing every hour ).
In Cisco ISE we don't see anything suspicious and everything is working fine on our MS. MX is a different story. See the logs below :
As anyone seen this issue ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have only done this using Microsoft NPS. And that is not normal behaviour.
You're not using COA or anything like that to re-authorise the device on the ISE side?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm curious how you have .1x auth on a MX68. My MX68W does not have .1x/MAB auth on the ports, neither in 14.x or 15.x firmware....
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sorry I didn't read this closely enough. The MX68 does not support wired dot1x yet.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you , but I'm well aware of the situation of the MX68 , the log below is exactly the same for all our MX65(W) , should have mentioned it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
There is no switch in the situation the devices are directly plugged into the MX. Device -> MX -> ISE. In that case the MX is the Authenticator.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
No worries !
That is part of the issue , there is 0 settings for MAB / 802.1X on the MX ( except de radius port and server ) and I can't find any documentation from Meraki. I think I will have to open a support ticket about this one and post the result here.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @RaphaelL
Kindly post what you get from Support, we are interested in this too.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This is what I got from support :
After gathering the data and discussing this with our Engineering team we've determined that this is the expected behavior for MX devices using 802.1X based authentication. The current reauthentication timer on the MX is set at 3600s / 1hr, and I've confirmed that unfortunately at this time we are unable to change that value at all, so this is all working as expected in this situation from what we can see.
I'm still worried about the DHCP renew at every reauth. I don't think that is a expected behavior...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Well ,
Support was able to reproduce the same issue in their lab. But it is only affecting Windows OS...
"I was able to get a Windows 10 client setup in my lab and in that case I am now seeing the client perform a DHCP Renew every time it reauthenticates via .1x, exactly like we're seeing in your client sites. So in this case it appears that the DHCP transaction after a .1x reauth is expected for Windows 10 clients at least. "
Has anyone experienced this issue ? Anyway to fix it ( parameters in windows or something ) ?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hey there , bumping my old thread.
Has anyone got any issues so far with the reauth timer ( 1h ) and their Cisco IP Phones ?
Every hour or so we keep having a ' UCM disconnected / is down' sort of message on the phones and it looks to be happening during the reauth.
Thanks !
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi ,
Even with MX 14.53 and Win 20H2 we are still seeing Windows PC renewing their lease at every reauth on MX ( only on MX once again ... )
Has anyone tested with Win11 ? We don't have Win11 devices yet.
Thanks ,
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
did this every get reoslved?
Thanks
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
No.
There is a static re-auth time of 3600s on MXs , when a Windows station does a 802.1X re-auth it goes to the DHCP renewal process. There is nothing to fix here, just a odd behavior.
-
3rd Party VPN
164 -
ACLs
88 -
Auto VPN
289 -
AWS
36 -
Azure
66 -
Client VPN
368 -
Firewall
833 -
iOS
1 -
Other
540 -
Wireless LAN MR
1