We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- Re: SFTP session disconnecting
SFTP session disconnecting
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
SFTP session disconnecting
All,
I've set up a port forwarding rule to allow TCP 22 to a particular server, in order to support an SFTP server.
The connection is successfully being made, user logs in, but file transfers disconnect after transferring only a few kb.
Error code in the sftp server is: Winsock error - 10054 which indicates the remote client is disconnecting.
Error code in the client indicates something similiar, the connection is being interrupted.
I've used several different clients and even at one point changed SFTP server software. I'm getting the same results.
As such, I've concluded it must be something related to my Meraki MX unit but I don't know where to find logs or what I would even check.
Any ideas would be appreciated
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I see I must have whitelisted that a long time ago and forgot. So that explains why it worked for me 😉
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have an SFTP server behind my MX and have no issue. Have you done a packet capture to look at it?
My rule is TCP 20-22 to an internal server because I have to support some FTP too.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
yes, I have run a pcap but it doesn't show anything obvious.
I've also run a connection locally from a client on the same LAN as the server to eliminate the firewall connect. When I do it this way, I get no disconnection.
If I use the same client but connect using the public IP address and back in via the MX unit, disconnect errors.
I also have another external business partner connecting remotely and also getting the same disconnect problem. Its looking like the MX unit as the issue
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Might check Security Center event log
https://documentation.meraki.com/MX/Monitoring_and_Reporting/Security_Center
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
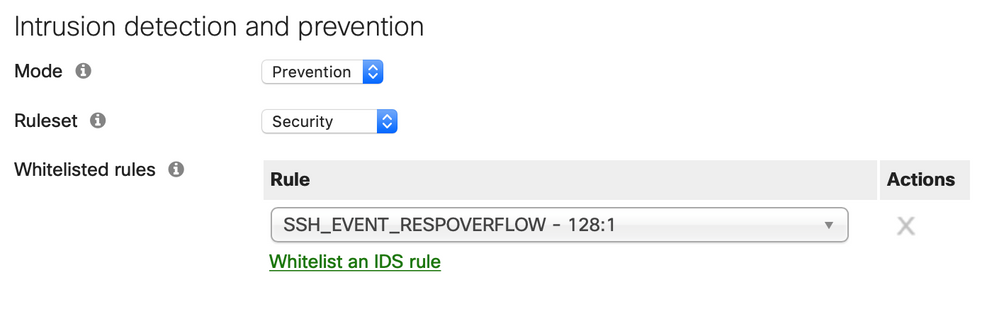
great call! I found this in the logs: IDS Alert SSH_EVENT_RESPOVERFLOW
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I see I must have whitelisted that a long time ago and forgot. So that explains why it worked for me 😉
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
crap, i already have it whitelisted as well but it's still appearing
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In my experience whitelisting these ID events doesn't work very well or quickly.
Your best bet is start by changing the ruleset to balanced instead of security. The next option is change the mode to detection. Then it pinpoints which part of ID is detecting/causing it.
The other thing you might check is AMP settings.
Also if you can provide the SNORT link to the vulnerability it is detecting
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
306 -
AWS
36 -
Azure
70 -
Client VPN
383 -
Firewall
868 -
iOS
1 -
Other
557 -
Wireless LAN MR
1