We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- Received our first ever IDS Alert - Fortinet FortiOS and FortiProxy authent...
Received our first ever IDS Alert - Fortinet FortiOS and FortiProxy authentication bypass attempt
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
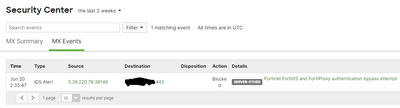
Received our first ever IDS Alert - Fortinet FortiOS and FortiProxy authentication bypass attempt
Have any members seen this one. We don't utilize Fortinet products. Is this coming from someone who uses this equipment or have they been compromised. Thanks in advance for any responses!
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Here was Meraki supports response:
It appears the attempt was blocked by Snort but it doesn't look like this is a known issue but it appears similar enough to something that is known hence it was blocked by Snort.
Meraki Support isn't actually able to make changes to the existing security policies as they are provided by a 3rd party. We can, however, bring it to their attention and they are constantly providing security updates. Unfortunately we have to wait for a Meraki Firmware update as the changes are baked into the firmware etc.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Have you tried checking the source and destination?
Please, if this post was useful, leave your kudos and mark it as solved.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes. Source is an IP in the Netherlands. Destination is my front facing IP.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sounds like a false positive to me, if you don't use Fortinet products then I am not sure why you would see this. Perhaps you should contact support and query it.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I will. Thanks Blake!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It could be a correct detection. I've had similar detections on a firewall that is also non-Fortinet and non-Meraki).
The detection is based on network traffic and connection details.
There will be bad actors on the internet spraying CVE attacks at any available targets, even if they don't know the firewall vendor.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Here was Meraki supports response:
It appears the attempt was blocked by Snort but it doesn't look like this is a known issue but it appears similar enough to something that is known hence it was blocked by Snort.
Meraki Support isn't actually able to make changes to the existing security policies as they are provided by a 3rd party. We can, however, bring it to their attention and they are constantly providing security updates. Unfortunately we have to wait for a Meraki Firmware update as the changes are baked into the firmware etc.
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
306 -
AWS
36 -
Azure
70 -
Client VPN
382 -
Firewall
867 -
iOS
1 -
Other
557 -
Wireless LAN MR
1