- Technical Forums
- :
- Security & SD-WAN
- :
- Non-Meraki VPN. How to advertise remote network?
Non-Meraki VPN. How to advertise remote network?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Non-Meraki VPN. How to advertise remote network?
Hello to everyone!
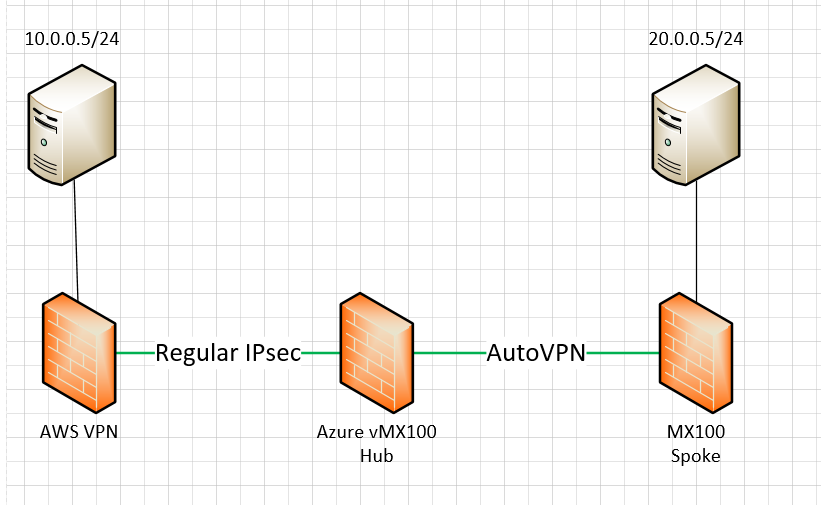
I hope some of you already faced this challenge. In a few words I need to advertise subnet behind non-Meraki VPN across all AutoVPN topology. I have further design (see attachment) or simply here server1<->AWS VPN gateway <-> Azure vMX100 (hub) <-> MX100 <-> server2.
The question is related to configuration on Azure vMX100 (hub). There some options:
1. Default configuration without network tags isn't an option due to necessity of hundreds VPNs between AWS and each spoke.
2. Tag network which contains Azure vMX100 (hub) and put it as only available for VPN between Azure vMX100 (hub) and AWS. Then create local network which includes server1 network. In this case all spokes get advertisements for AWS subnet.
However it's just a routing and I have no idea will it work or not for end-to-end communication.
Thank you all in advance!
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You wont be able to inject a non-Meraki VPN route into AutoVPN. You will need to have each spoke also use a non-Meraki VPN to the AWS instance.
It sounds to me like you need to buy the vMX for AWS - especially if you are talking about hundreds of spokes.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Any chance to do it manually without deploying vMX in Azure? Static routing etc.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, you must have a HUB to do the BGP route for all the sites/branches.
In my case, I have it in MS Azure - Fortigate VF so there will not be any dependency if the branch or sites is down.
MS Azure - Fortigate VF provided 99.99% uptime 🙂
All my branches are using Meraki MX - I mean full Meraki.
Only the cloud I'm not using vMX because vMX is just a VPN concentrate without any security much there.
But there's 1 thing that is beneficial to use vMX from Meraki, VPN will auto comes up with the secondary internet when your primary internet is down in any of the branch or sites. Fortigate VF doesn't, you need to manual setup.
We choose Fortigate VF because we forward the traffic towards the Fortigate because it performs all the security check such as, virus, malware, hackers & so on.
-
3rd Party VPN
170 -
ACLs
101 -
Auto VPN
316 -
AWS
39 -
Azure
71 -
Client VPN
431 -
Firewall
721 -
Other
596