Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Re: Meraki - alert when previously unseen device connects to the network
Meraki - alert when previously unseen device connects to the network
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Meraki - alert when previously unseen device connects to the network
I understand that "previously unseen" may mean "previously unseen in the last 30 days", but at any rate... does anyone know of a magical way to achieve this?
I'm working on security assessment, and that is one of the objectives...
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Have you considered going the other way, and using something like wired 802.1x to only allow authorised devices to connect?
https://documentation.meraki.com/MX/Access_Control_and_Splash_Page/MX_Access_Policies_(802.1X)
If you have a Meraki MS switch - it's better to do it there.
https://documentation.meraki.com/MS/Access_Control/MS_Switch_Access_Policies_(802.1X)
802.1x can be complicated to setup. If you are a smaller organisation and want something simpler, create a firewall that does a "deny any any" - blocking everything. Then create a group policy called "authorised" which overrides this rule granting access. Then apply the "authorised" group policy to those clients allowed to connect.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
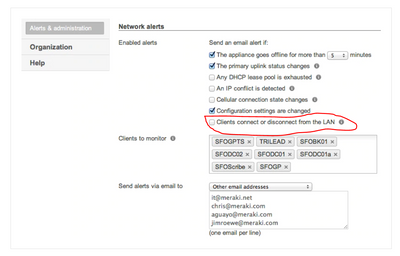
Are you looking for this ?
https://meraki.cisco.com/blog/2013/02/manage-devices-with-instant-alerts/
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It only monitors the clients you specify. What if we want to know if a previously *unknown* client connects? That's what I'm looking for. It is SOO close...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I dont think it is possible as if you talk about the production secure network "unknown clients" will never connected earlier. This is security concerns.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Have you considered going the other way, and using something like wired 802.1x to only allow authorised devices to connect?
https://documentation.meraki.com/MX/Access_Control_and_Splash_Page/MX_Access_Policies_(802.1X)
If you have a Meraki MS switch - it's better to do it there.
https://documentation.meraki.com/MS/Access_Control/MS_Switch_Access_Policies_(802.1X)
802.1x can be complicated to setup. If you are a smaller organisation and want something simpler, create a firewall that does a "deny any any" - blocking everything. Then create a group policy called "authorised" which overrides this rule granting access. Then apply the "authorised" group policy to those clients allowed to connect.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@PhilipDAth, I like your idea of applying a default policy for the VLAN and then over riding it on a per client basis. The only potential issue I see is that if a device is offline for 30 days for some reason, I think the over ride policy will need to be reapplied, but that should be really rare.
Great suggestion, thank you! 🙂
-
3rd Party VPN
155 -
ACLs
85 -
Auto VPN
274 -
AWS
33 -
Azure
63 -
Client VPN
364 -
Firewall
808 -
iOS
1 -
Other
523 -
Wireless LAN MR
1