Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Re: MX84 RADIUS authentication failing for client VPN
MX84 RADIUS authentication failing for client VPN
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
MX84 RADIUS authentication failing for client VPN
Hello,
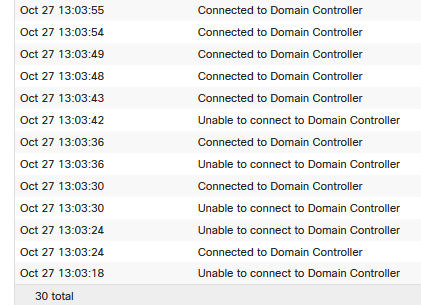
Yesterday I noticed that our MX84 event log has been filling up with DC connection errors (unable to connect to domain controller), and the logs on my DCs have been filling up with DCOM error 10036 (The server-side authentication level policy does not allow the user (RADIUS auth user) SID (*****) from address (MX84 IP) to activate DCOM server. Please raise the activation authentication level at least to RPC_C_AUTHN_LEVEL_PKT_INTEGRITY in client application).
I've done some Googling, but haven't come up with a working solution yet - any ideas?
I was alerted to the issue when our CEO wasn't able to authenticate with the VPN... NOT good.
Solved! Go to solution.
- Labels:
-
Client VPN
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I think it is related to this update. You might need to disable the hardening.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
For reference, we are running firmware v.15.44 and there are a number of others having the same or similar issue related to recent Windows security updates on domain controllers. In my case the update is KB5005568 which I am unable to uninstall.
There is a relevant thread at Microsoft here which gives more insight into the issue.
Is there any reason to believe the 16.x firmware branch would solve the problem?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I think it is related to this update. You might need to disable the hardening.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for the reply PhilipDAth. I've read that topic and applied the recommended change, and although I am seeing users successfully logged into the VPN, authentication still seems to be hit and miss judging from my MX log (see image below).
From looking at the deployment roadmap at that link, it would seem that this issue will become a real problem when Microsoft makes it impossible to disable that CVE fix in 2022, which isn't that far away.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Has there been a proper resolution put into place for this yet? I chose to disable it on one of my servers while we have the option. The ability to manually disable it ends in June per the document referenced above: KB5004442 - DCOM hardening
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I haven't seen anyone having this issue using RADIUS authentication against NPS. Are you sure you are using RADIUS authentication rather than direct Active Directory authentication?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You are absolutely right! I meant AD authentication..not radius. Support ticket opened indicates this a MS problem and not a Meraki problem, but come June this could be a bigger issue because the registry fix won't work.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
NPS (Microsoft's RADIUS server) is built into Windows Server and has no additional cost. Any reason you can't change over to using it?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I can certainly do that. This would remediate this issue then because it is specific to AD authentication?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Correct.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That's the same solution that I came up with. We have been using RADIUS authentication for months now with no issues. Fortunately, I was just testing AD authentication so switching over wasn't a big deal for me.
-
3rd Party VPN
170 -
ACLs
91 -
Auto VPN
296 -
AWS
36 -
Azure
68 -
Client VPN
379 -
Firewall
849 -
iOS
1 -
Other
547 -
Wireless LAN MR
1
