- Technical Forums
- :
- Security & SD-WAN
- :
- MX68CW-WW can't make VPN with Fortinet
MX68CW-WW can't make VPN with Fortinet
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
MX68CW-WW can't make VPN with Fortinet
Greetings,
MX68CW-WW on branch cannot VPN to Fortinet at HQ. It will work for 2 minutes if I manually turn off and on Site to Site VPN on Meraki and then after 2 minutes it's down again. TAC advise me to set DPD, turn off PSF. It work for 1 day and after that the issue is cameback.
Meraki and Fortinet get the IP public IP, We try as we could but still not working. Anyone has ever face the problem like this ? Please share solution.
Thank you,
Neo
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Replace the Fortinet. The problem will disappear 🧹🧹
https://www.linkedin.com/in/darrenoconnor/
I'm not an employee of Cisco/Meraki. My posts are based on Meraki best practice and what has worked for me in the field.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Make sure the encryption domains on both ends are identical.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
We run Meraki to Fortigate S2S VPN for a long time without any issue.
I don't know which Subnet you need, but if you have more than one, try to summarize all on one instead of adding each one by one.
Here is a configuration sample for IKE v2 but if you are in IKEv1 just change encryption for 3DES MD5. I dont know if it's change anything but it's worked for me.
Regards,
Fortinet VPN :
config vpn ipsec phase1-interface
edit "xxxxx"
set interface "wan1"
set ike-version 2
set keylife 28800
set peertype any
set net-device enable
set proposal aes128-sha256
set dpd disable
set dhgrp 2
set nattraversal disable
set remote-gw xxx.xxx.xxx.xxx
set psksecret ENC xxxxxxxxxxxxxxxx
next
edit "xxxxx"
set phase1name "xxxx"
set proposal aes128-sha256
set pfs disable
set keepalive enable
set keylifeseconds 28800
set src-subnet 10.32.0.0 255.255.248.0
set dst-subnet 10.32.64.0 255.255.248.0
next
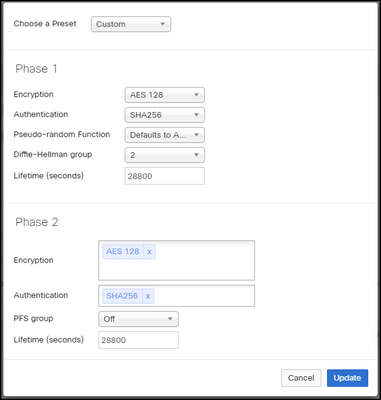
And the configuration on Meraki Side :
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
-
3rd Party VPN
171 -
ACLs
101 -
Auto VPN
318 -
AWS
39 -
Azure
72 -
Client VPN
435 -
Firewall
727 -
Other
601