Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Re: MX to AWS non-meraki peer VPN only routing one vlan at a time
MX to AWS non-meraki peer VPN only routing one vlan at a time
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
MX to AWS non-meraki peer VPN only routing one vlan at a time
Good day everyone, this is my first time posting in the forums so I apologize if I miss any details.
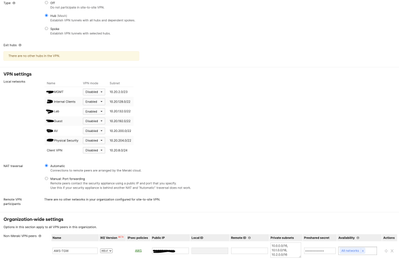
I have a client office running HA MX250 to an AWS TGW.
Meraki side has 2 VLANs included in the VPN and 3 private subnets (each a VPC in AWS)
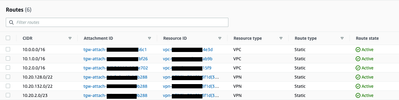
The AWS TGW route table has the following static routes. There is a 3rd VPN route included because I has removed one from the MX but have not update AWS TGW route table
The issue I am having is that from the MX side, only one of the two include VLANs can actually send traffic to the VPC resources. If I run a ping from the meraki dashboard using the L3 interfaces to ping a gateway of a subnet in AWS, only one succeeds at a time.
In the AWS site to site VPN config document that is downloaded from the VPN configuration page:
! AWS hosted VPN solution is a route-based solution, since Cisco Meraki only supports policy-based solution you will need to limit to a single SA. So please make sure to
! select "yes" for just one subnet, if you have more than one subnet, consolidate them into a single subnet before proceeding with the VPN configuration.
If I am understanding this correctly, I am not able to have more than 1 subnet included in the non-meraki peer VPN due to this SA limitation. I have been trying to google how the Security Associations are established and it seems like the limitation is from the phase 2 IKE negotiations, since Phase 1 happens between the public addresses.
Any confirmation or correction on my above understanding is greatly appreciated!
Solved! Go to solution.
- Labels:
-
3rd Party VPN
-
AWS
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That restriction is as expected. I would consider getting a VMX-S.
https://meraki.cisco.com/product/security-sd-wan/virtual-appliances/vmx-small/
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That restriction is as expected. I would consider getting a VMX-S.
https://meraki.cisco.com/product/security-sd-wan/virtual-appliances/vmx-small/
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you for confirming the behavior. We'll present the vMX as on of the options now that it also has multiple sizes.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
On the AWS side have you tried a "Transit Gateway" in place of the "Virtual Private Gateway" ?
My reading of Transit Gateways is that it acts like a router inside AWS to connect multiple VPCs together and provide
a single "public" interface. They do cost money though, slightly more than the VPN (in my region), so would be about double your current cost as you still need to pay for the VPN.
Though may not get around the 1 subnet limit on the Meraki side unless all VPCs in the Transit Gateway map into a single CIDR.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Its a limitation of using IKEv1. IKEv1 allows only one SA at a tunnel, secondary SA will not be formed until the primary is deleted. Use IKEv2 to fix the issue. It allows multiple SA at a tunnel and the traffic flows seamlessly.
Another Temporary workaround is it use higher prefix on the Meraki. Instead of allowing various 10.20 segment , configure one static route with 10.20.0.0/16 and enable it on VPN.
-
3rd Party VPN
162 -
ACLs
88 -
Auto VPN
287 -
AWS
35 -
Azure
66 -
Client VPN
366 -
Firewall
831 -
iOS
1 -
Other
538 -
Wireless LAN MR
1