We're migrating to the Cisco Community on March 29. The Meraki Community will enter read-only mode starting on March 26.
Learn more- Technical Forums
- :
- Security & SD-WAN
- :
- Re: MX behind another MX
MX behind another MX
Solved- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
MX behind another MX
Hello everyone,
just wanted to see if this configuration is possible in any way.
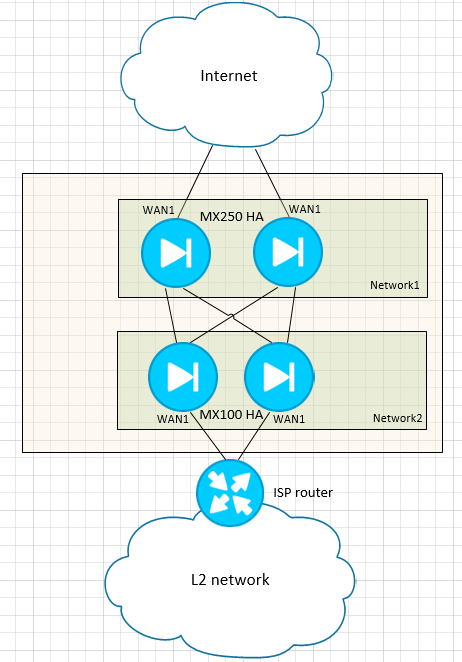
We have two MX250 and two MX100, both should be in HA. The idea was to have the two MX250 as Internet border devices and two MX100 that connect to them and also connect to L2 service provider network through which they would bring up tunnels to other branch MXs connected to that same L2 network. In other words MX100s would be used as kind of a VPN hub for other branches and forward the traffic to MX250s if the traffic is destined towards Internet. Something like this:
I'm not sure however if MX100s can be connected to MX250s via LAN ports in a way that they could have cloud connectivity through them (since service provider L2 network doesn't have Internet access)?
If this is not a viable topology does someone have an alternate proposition/solution?
Best regards
Solved! Go to solution.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
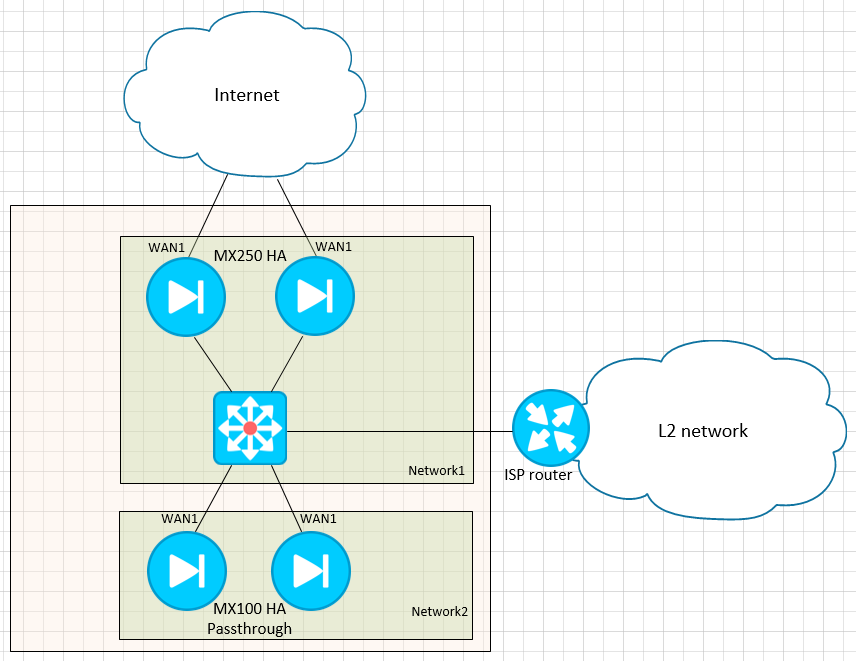
Put the MX100s in VPN concentrator mode and have them in single ended mode off to the side.
Internet to MX250 WAN
MX250 LAN to switch
MX100 WAN to switch
MPLS router connected to switch
Switch is L3 and has routes to internet so everyone gets a connection
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What is the WAN situation at the branches? L2 WAN and internet or just the L2 WAN?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
Just the L2 WAN. The idea is that every branch should go to Internet through those MX250s.
Best regards
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Put the MX100s in VPN concentrator mode and have them in single ended mode off to the side.
Internet to MX250 WAN
MX250 LAN to switch
MX100 WAN to switch
MPLS router connected to switch
Switch is L3 and has routes to internet so everyone gets a connection
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
if the branches are just L2 connected why tunnel it in VPN at all?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@Ryan_Miles we have two L2 networks that we needed to load balance and although @GospodinMat1 hasn't shown that, it may also be the case here? Secondly we wanted to encrypt our traffic over the WAN as you can't just assume it is secure... 😈
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
There's only one L2 network, everything goes over the same provider, however yes, the requirement is to encrypt the traffic that goes from the branches to center.
As I've mentioned, we're open to suggestions, primarily if this can be achieved in any way with just these 4 MXs...
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
the layout cmr suggested should meet your needs then
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you for the proposition! If I understood it correctly, it would look something like this:
I like it since if I had designed the solution from scratch, it would have probably done something similar. We were however given the equipment and told to do the best with what we have, so, as you can imagine I'm trying to come up with something that involves the existing hardware before we ask for some additional. 🙂
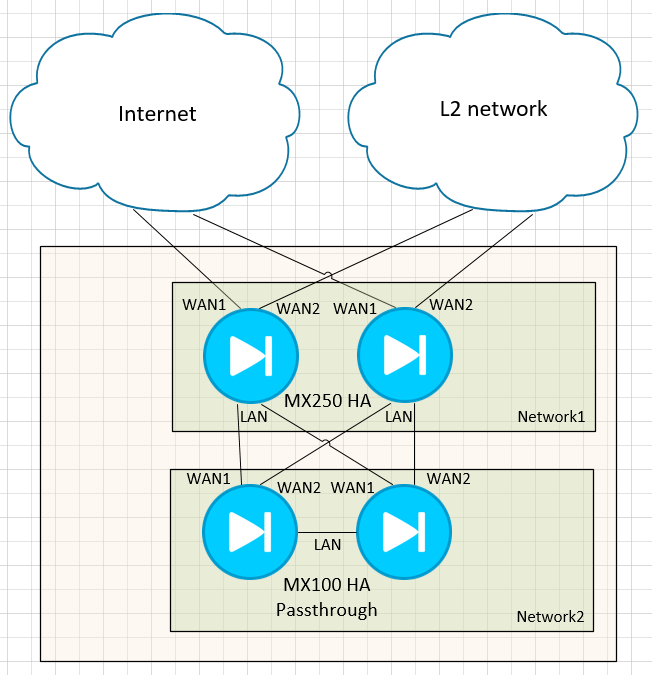
So I guess my question would be if this could be achievable with something like this:
MX100s would still be terminating the VPN tunnels to branch locations on the L2 network while MX250s would, I guess, perform some kind of policy-based routing in a way that everything meant for branch communication would go on the WAN2 interface while all other traffic would go to WAN1.
Do you think this is a viable solution at all? Will we run into some VRRP, STP, or simply general connectivity problems with this topology?
Best regards
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@GospodinMat1 the top diagram is exactly what we do, as for the lower diagram, it might work, but I'm not sure WAN2 would come up on the MX250s. It's also one hell of a complex setup to troubleshoot!
-
3rd Party VPN
174 -
ACLs
91 -
Auto VPN
306 -
AWS
36 -
Azure
70 -
Client VPN
383 -
Firewall
868 -
iOS
1 -
Other
557 -
Wireless LAN MR
1