Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- Re: MX Firewall rule issue
MX Firewall rule issue
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
MX Firewall rule issue
Hi,
I have been working on our rule list recently and an error I get fairly often when trying to create a rule is...
"(IP address) does not apply to any configured local or VPN subnets in the source field".
I don't care if its not a locally configured IP range, I want to create that rule....why is it stopping me doing this?
thanks,
- Labels:
-
Firewall
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi ,
What are you trying to achieve ? The L3 firewall outbound rules will only block or allow traffic "sourced" and routed by the MX.
On the MX, outbound traffic refers to traffic originating from one VLAN that is destined for another VLAN or traffic originating from the LAN that is destined for the Internet or a remote network that is located over a static LAN route.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
For example, we have over 60 networks in a WAN and I am trying to standardize as many of the firewall rules as possible.
They all have the same VLAN that needs to be isolated. Cant talk to other deices, other devices cant talk to it (it just allows internet access).
We have firewall rules to stop traffic to and from that VLAN to any private IP.
Some sites use different private address ranges than others - so to make things easy, I have a group that contains all the private ranges - 192.168 / 172.16 / 10.0.
The idea being that we can have the exact same rule applied to every network to do the same job - but Meraki says no because one or more of those ranges may not be configured on the Meraki.
Also, what about subnets configured on non-meraki hardware?
Also, - why does it matter? If I create a rule that doesn't do anything because the source never applies to anything....so what? If I want to configure that rule for whatever reason I should be able to.
Does this restriction somehow help stop accidental, catastrophic mistakes?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Other option could be to use a group policy and attach it to the vlan interface
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
thanks for the reply,
but....I would rather address the issue directly than find a work around.
Also, trying to keep things as simple as possible as we have so many networks and staff scattered around the world, not to mention the possibility of new team members joining in the future - don't really want people to have to scratch their head and dig all over the place to try and find where something might be getting blocked.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The only option is to use a source for that vlan that falls within a supernet. And use the supernet as source in the firewall rule
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
sorry, dont quite understand.
If im creating a rule to block all traffic FROM all private address ranges, TO vlan subnet - how does that work?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It doesnt .
Maybe it works if you create 3 small dummy vlan/subnet in the rfc1918 subnet on all locations.
I dont know why meraki doesnt allow it, but afaik it has always been this way
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
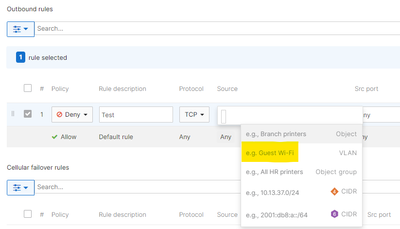
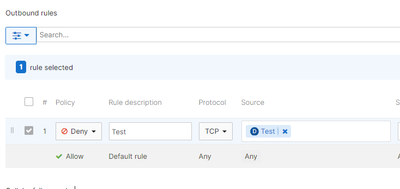
I'm struggling to find the documentation, and you don't say if you are using templates, but you can reference VLANs directly instead of by IP address.
Some info here:
Because I can't find the docs, I've done some screen shots for you. See how in the "help" section it says "VLAN"? You can just type in the VLAN name.
For example, I created a VLAN called "Test" and applied this rule to it:
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Maybe I have made an assumption here. Are you talking about a L3 outound rule, an AutoVPN firewall rule, a group policy firewall rule, or something else?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
sry, yes its outbound firewall rules.
I want to block anything from 192.168.0.0/24 172.16.0.0/16 10.0.0.0/8
going to a particular VLAN.
I have those 3 private ranges in a Group.
All our sites use 1 or more of those private ranges. I just want to have the same rule on every site.
The rule works fine on most sites, but I dont know why. One example of a working site has 2 VLANs configured using ips in the 10.0 range, but none of the others.
It does also advertise a static route in the 172 range.
But it doesnt have anything 192 whatsoever - yet it let me create the rule using the private address Group we made that contains all three private subnets.
If it was behaving consistently, I would expect it to not allow the rule because of the 192 subnet in the group that is set as the source.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Use vlan objects in your firewall rules instead. I do that for 150+ sites. Works like a charm.
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Adrian4,
My team actually ran into a similar need for this while testing eBGP in routed mode (you can't filter based on source routes learned via eBGP either).
The workaround we found was to create a static route for the source network you are trying to create a firewall rule for, we chose to use 0.0.0.0 as the next hop (assuming route recursion, this should send it towards wherever you learn your default route from). You can then disable this route so it has no effect, but the firewall rule will be allowed to be entered.
Here's an example:
You want to enter a firewall rule defining source as 192.0.2.0/24, destination any, deny
Enter a static route 192.0.2.0/24 next-hop 0.0.0.0, save, disable that route, save.
Enter the firewall rule you desire, save.
Our team assumption is based on the reading here that Sources need to be from the "configured subnets" on the "MX Addressing & VLANs page" and thankfully static routes are included in that validation. We agree with you that the validation makes no sense honestly, why should any firewall care if you have an extra firewall rule disallowing source addresses that you may or may not own? What does that actually prevent? Hope this helps anyway
Also the group policy option is objectively terrible if you use it to override L3 firewall rules, as any device(s) governed by that firewall ruleset become independent flows when it comes to state tracking of the main L3 firewall rules, effectively making your firewall rules become stateless (useless)
-
3rd Party VPN
170 -
ACLs
91 -
Auto VPN
296 -
AWS
36 -
Azure
68 -
Client VPN
379 -
Firewall
849 -
iOS
1 -
Other
547 -
Wireless LAN MR
1