Get answers from our community of experts in record time.
Join now- Technical Forums
- :
- Security & SD-WAN
- :
- How to require MFA every time for AnyConnect with Azure AD?
How to require MFA every time for AnyConnect with Azure AD?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to require MFA every time for AnyConnect with Azure AD?
So we have set up AnyConnect to authenticate via SAML with Azure AD for client VPN authentication. We asked the Meraki support to turn off the force authentication option because it makes the users have to type in their full email address and password every time they connect to VPN. However with that turned off, many users are never prompted for their username, password or MFA if they are signed into Office 365 on their computers. What we would like is for the users to not be prompted for their username or password, but still get prompted for their MFA each time they connect. Is this behavior possible to enable either from the Meraki side or from the Azure AD side?
- Mark as New
- Bookmark
- Subscribe
- Mute
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
First let's address the whole concept of SAML and SSO - SSO stands for "single-sign-on". That means you only need to sign into one system to be signed into every system. It's the entire premise of using a SSO.
I would encourage you to think about the point of using a SSO and then trying to disable SSO. It's just not quite right ... and you can see why it might be hard to make it do something it was specifically to solve.
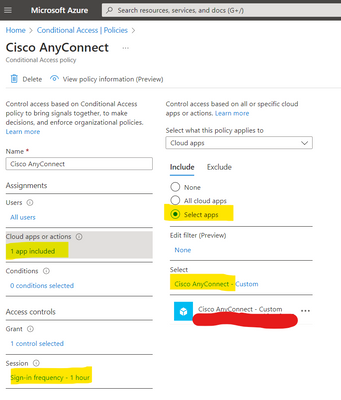
Having said that - you can create a condition access policy and specify a session limit. Alas in Azure the minimum session limit is 1 hour, but this would at least meant AnyConnect sessions more than 1 hour apart would always require a full authentication again.
With nicer SAML providers like Cisco Duo - this is simple a "radio button" style option.
-
3rd Party VPN
172 -
ACLs
91 -
Auto VPN
301 -
AWS
36 -
Azure
70 -
Client VPN
381 -
Firewall
856 -
iOS
1 -
Other
552 -
Wireless LAN MR
1